We learned some remarkable new details this week about the recent supply-chain attack on VoIP software provider 3CX. The lengthy, complex intrusion has all the makings of...
Training New Hires on Security: Strategies for Success
The rise of cyberthreats and the growing complexity of the IT threat landscape means security training for all organizations must be a paramount concern. Instilling a...
Attackers using AI to enhance conversational scams over mobile devices
Attackers are using artificial intelligence (AI) to enhance conversational scams, such as the so-called “pig butchering” social engineering scams, over mobile devices. Instead of just using...
An Iranian hacking group went on the offensive against U.S. targets, Microsoft says
Welcome to The Cybersecurity 202! Just when I think I’ve seen every amazing octopus video, I stumble across something like this. I will probably never catch...
The Week in Ransomware – April 21st 2023 – Macs in the Crosshairs
A lot of news broke this week related to ransomware, with the discovery of LockBit testing macOS encryptors to an outage on NCR, causing massive headaches...
Critical infrastructure also hit by supply chain attack behind 3CX breach
The X_Trader software supply chain attack that led to last month’s 3CX breach has also impacted at least several critical infrastructure organizations in the United States...
GhostToken GCP flaw let attackers backdoor Google accounts
Google has addressed a Cloud Platform (GCP) security vulnerability impacting all users and allowing attackers to backdoor their accounts using malicious OAuth applications installed from the...
Kubernetes RBAC abused to create persistent cluster backdoors
Hackers use a novel method involving RBAC (Role-Based Access Control) to create persistent backdoor accounts on Kubernetes clusters and hijack their resources for Monero crypto-mining. RBAC...
American Bar Association data breach hits 1.4 million members
The American Bar Association (ABA) has suffered a data breach after hackers compromised its network and gained access to older credentials for 1,466,000 members. The ABA...
University websites using MediaWiki, TWiki hacked to serve Fortnite spam
Websites of multiple U.S. universities are serving Fortnite and ‘gift card’ spam. Researchers observed Wiki and documentation pages being hosted by universities including Stanford, MIT, Berkeley, UMass Amherst, Northeastern, Caltech, among others,...
CFPB Employee Sends 256,000 Consumers’ Data to Personal Email
An employee from the US Consumer Financial Protection Bureau (CFPB) has reportedly forwarded confidential records of roughly 256,000 consumers and confidential supervisory information of approximately 50...
Evil Extractor Targets Windows Devices to Steal Sensitive Data
The attack tool known as Evil Extractor and developed by a company called Kodex as an “educational tool,” has been used by threat actors to target...
Trojanized Installers Used to Distribute Bumblebee Malware
Popular software tools such as Zoom, Cisco AnyConnect, ChatGPT and Citrix Workspace have been trojanized to distribute the malware known as Bumblebee. Secureworks’ Counter Threat Unit...
Did you mistakenly sell your network access? – Week in security with Tony Anscombe – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Editor. Many routers that are offered for resale contain sensitive corporate information and allow third-party connections to corporate networks Did you mistakenly...
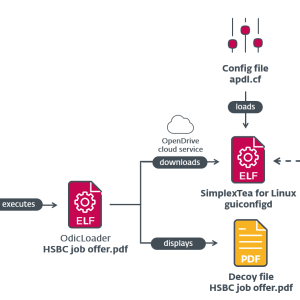
Linux malware strengthens links between Lazarus and the 3CX supply‑chain attack – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Peter Kálnai. Similarities with newly discovered Linux malware used in Operation DreamJob corroborate the theory that the infamous North Korea-aligned group is...
North Korea’s Kimsuky APT Keeps Growing, Despite Public Outing
Globally, interest has surged around North Korea’s Kimsuky advanced persistent threat group (a.k.a. APT43) and its hallmarks. Still, the group is showing no signs of slowing...
Hacking Pickleball
Hacking Pickleball My latest book, A Hacker’s Mind, has a lot of sports stories. Sports are filled with hacks, as players look for every possible advantage...
Using the iPhone Recovery Key to Lock Owners Out of Their iPhones
This a good example of a security feature that can sometimes harm security: Apple introduced the optional recovery key in 2020 to protect users from online...
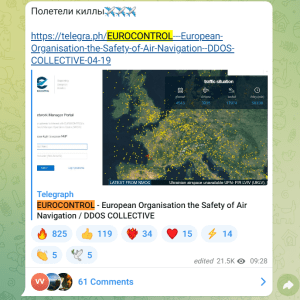
Pro-Russia hackers launched a massive attack against the EUROCONTROL agency – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Pro-Russia hackers KillNet launched a massive DDoS attack against Europe’s air-traffic agency EUROCONTROL. Europe’s air-traffic control agency EUROCONTROL announced that...
Cisco fixed critical flaws in the Industrial Network Director and Modeling Labs solutions – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Cisco released security updates to address critical security flaws in its Industrial Network Director and Modeling Labs solutions. Cisco released...
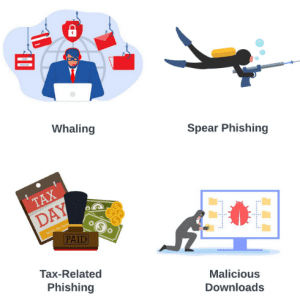
Intro to phishing: simulating attacks to build resiliency – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Phishing attacks are a major threat to organizations, they remain a perennial choice of cybercriminals when it comes to hacking...
Multinational ICICI Bank leaks passports and credit card numbers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. ICICI Bank leaked millions of records with sensitive data, including financial information and personal documents of the bank’s clients. ICICI...
VMware fixed a critical flaw in vRealize that allows executing arbitrary code as root – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. VMware fixed two severe flaws, tracked as CVE-2023-20864 and CVE-2023-20865, impacting the VMware Aria Operations for Logs product. The virtualization...
Lazarus APT group employed Linux Malware in recent attacks and was linked to 3CX supply chain attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. North Korea-linked APT group Lazarus employed new Linux malware in attacks that are part of Operation Dream Job. North Korea-linked APT...
Introduction to Tabletop Exercises (TTX) – A practical Guidebook for Organizations by Capgemini for GFCE – Global Forum on Cyber Expertise
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Navigating the Pandora’s Box that is ChatGPT: Insights from a Global CISO
Jonathan Fischbein is the Chief Information Security Officer for cyber security vendor Check Point Software. He has more than 25 years’ experience in high-tech security markets,...
Why cyber security should be treated as an ESG issue
EXECUTIVE SUMMARY: The World Economic Forum describes cyber security as one of the top five global risks, highlighting the need for organizations to integrate cyber security...
RSAC Fireside Chat: Cybersixgill crawls the Dark Web to uncover earliest signs of companies at risk
By Byron V. Acohido Adopting personas and rubbing elbows with criminal hackers and fraudsters is a tried-and-true way to glean intel in the Dark Web. Related:...
Breach Roundup: US CFPB, NCR and Rheinmetall – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Fraud Management & Cybercrime , Incident & Breach Response , Ransomware Also in Focus: Philippines Law Enforcement Agencies, RentoMojo and Point...
HIPAA Considerations for AI Tool Use in Healthcare Research – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. The potential use cases for generative AI technology in healthcare appear limitless, but they’re weighted with an array of potential privacy,...