Source: www.databreachtoday.com – Author: 1. Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Ransomware Report Was Commissioned by the UK National Cyber Security Center...
Panel Discussion | The FTC Cha-Cha: Dancing to The Beat of Regulations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Fortra Hacker Installed Tools on Victim Machines – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. 3rd Party Risk Management , Fraud Management & Cybercrime , Governance & Risk Management Fortra Reveals Findings From GoAnywhere MFT Attack...
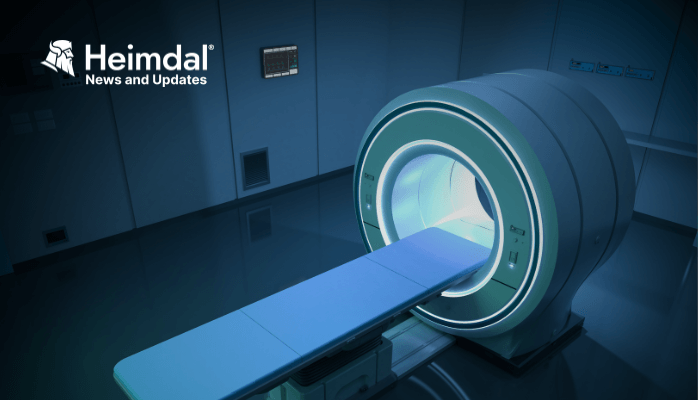
US Medical Service Data Breach Impacts 2.3M People
Shields Health Care Group (SHCG), a medical service provider in the United States, announced a data breach that compromised the personal information of more than 2.3...
Stay Ahead of Cyberthreats with Proactive Threat Hunting
In today’s digital age, cyber threats are an ever-present danger to organizations of all sizes. From ransomware attacks to data breaches, the consequences of a successful...
Cybercriminals Abusing an Abandoned WordPress Plugin for Malicious Code Injection
Threat actors found a new method to inject malicious code into websites. They are now using an abandoned WordPress plugin, Eval PHP. The plugin is still...
Millions of Records With Sensitive Data Leaked by ICICI Bank
ICICI Bank, an Indian multinational valued at more than $76 billion, with over 5,000 branches operating across India and 15 other countries worldwide has leaked millions...
SECURITY ALERT: Heimdal® Detects Massive MitID Smishing Campaign Targeting Nordea Bank Customers
On the 20th of April, Heimdal®’s SOC team has discovered that an unknown APT has been launching smishing attacks against Nordea Bank customers. The data analyzed...
3CX Breach Was a Double Supply Chain Compromise
We learned some remarkable new details this week about the recent supply-chain attack on VoIP software provider 3CX. The lengthy, complex intrusion has all the makings of...
VMware Patches Pre-Auth Code Execution Flaw in Logging Product – Source: www.securityweek.com – Author: Ryan Naraine –
Source: www.securityweek.com – Author: Ryan Naraine. Category & Tags: Application Security,Vulnerabilities,CVE-2023-20864,CVE-2023-20865 – Application Security,Vulnerabilities,CVE-2023-20864,CVE-2023-20865 Virtualization technology powerhouse VMware continues to encounter major security problems in its...
Microsoft Will Name Threat Actors After Weather Events – Source: www.securityweek.com – Author: Ryan Naraine –
Source: www.securityweek.com – Author: Ryan Naraine. Category & Tags: Cyberwarfare,Threat Intelligence – Cyberwarfare,Threat Intelligence Microsoft is ditching the chemical elements in favor of weather-themed naming of...
Ransomware Attack Hits Health Insurer Point32Health – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Ransomware,healthcare,ransomware – Ransomware,healthcare,ransomware Non-profit health insurer Point32Health says it has taken systems offline to contain a ransomware...
Phylum Adds Open Policy Agent to Open Source Analysis Engine – Source: www.securityweek.com – Author: Kevin Townsend –
Source: www.securityweek.com – Author: Kevin Townsend. Category & Tags: Risk Management,Supply Chain Security – Risk Management,Supply Chain Security Software supply chain security firm Phylum has added...
Cascading Supply Chain Attack: 3CX Hacked After Employee Downloaded Trojanized App – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Supply Chain Security,3CX,Featured,Supply Chain – Supply Chain Security,3CX,Featured,Supply Chain More information was made available on Thursday about...
Cisco Patches Critical Vulnerabilities in Industrial Network Director, Modeling Labs – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Vulnerabilities,vulnerability – Vulnerabilities,vulnerability Cisco this week announced patches for critical vulnerabilities impacting its Industrial Network Director and...
Air Force Unit in Document Leaks Case Loses Intel Mission – Source: www.securityweek.com – Author: Associated Press –
Source: www.securityweek.com – Author: Associated Press. Category & Tags: Data Breaches,data leak – Data Breaches,data leak The Air Force is investigating how a lone airman could...
UK Warns of Russian Hackers Targeting Critical Infrastructure – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Cyberwarfare – Cyberwarfare The UK government’s intelligence and security arm this week issued an alert on Russian...
PaperCut Warns of Exploited Vulnerability in Print Management Solutions – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Vulnerabilities,Featured,printer,vulnerability – Vulnerabilities,Featured,printer,vulnerability Print management solutions provider PaperCut has warned organizations that exploitation of a recently patched...
Fortra Completes Investigation Into GoAnywhere Zero-Day Incident – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Data Breaches,Vulnerabilities,data breach,GoAnywhere,Zero-Day – Data Breaches,Vulnerabilities,data breach,GoAnywhere,Zero-Day Fortra has completed the investigation into the recent zero-day incident...
Attackers use abandoned WordPress plugin to backdoor websites
Attackers are using Eval PHP, an outdated legitimate WordPress plugin, to compromise websites by injecting stealthy backdoors. Eval PHP is an old WordPress plugin that allows site...
Google: Ukraine targeted by 60% of Russian phishing attacks in 2023
Google’s Threat Analysis Group (TAG) has been monitoring and disrupting Russian state-backed cyberattacks targeting Ukraine’s critical infrastructure in 2023. Google reports that from January to March...
VMware fixes vRealize bug that let attackers run code as root
VMware addressed a critical vRealize Log Insight security vulnerability that allows remote attackers to gain remote execution on vulnerable appliances. Now known as VMware Aria Operations for...
Lazarus hackers now push Linux malware via fake job offers
A new Lazarus campaign considered part of “Operation DreamJob” has been discovered targeting Linux users with malware for the first time. This new targeting was discovered...
Microsoft 365 outage blocks access to web apps and services
Microsoft is investigating an ongoing outage blocking customers worldwide from accessing and using web apps like Excel Online and online services. The list of affected services...
Malware is proliferating, but defenses are stronger: Mandiant
Image: Askha/Adobe Stock Threat groups are on the rise, and Google Cloud’s cyberdefense unit Mandiant is tracking 3,500 of them, with 900 added last year, including...
Capita confirms hackers stole data in recent cyberattack
London-based professional outsourcing giant Capita has published an update on the cyber-incident that impacted it at the start of the month, now admitting that hackers exfiltrated...
3CX hack caused by trading software supply chain attack
An investigation into last month’s 3CX supply chain attack discovered that it was caused by another supply chain compromise where suspected North Korean attackers breached the...
US charges three men with six million dollar business email compromise plot
Three Nigerian nationals face charges in a US federal court related to a business email compromise (BEC) scam that is said to have stolen more than...
LockBit ransomware for Mac – coming soon?
In the last couple of days it has become clear that the notorious LockBit ransomware gang has been exploring creating what could one day become a...
MacStealer – newly-discovered malware steals passwords and exfiltrates data from infected Macs
I’m still encountering people who, even after all these years, believe that their Apple Mac computers are somehow magically invulnerable to ever being infected by malware....