Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: Christophe Coat via Alamy South African government officials are investigating reports that a ransomware gang stole and...
The TikTok Ban Bill, Your Car is Spying on You, Signal’s Username Update – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston In episode 321, the hosts discuss how connected cars are sharing driving data with insurance companies, potentially leading to increased...
HSE Misconfiguration Exposed Over a Million Irish Citizens’ Vaccine Status – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Protected health information and personal details of over a million Irish citizens were accidently exposed by the Ireland’s Health Service Executive...
5 Best VPNs for Travel in 2024 (Free & Paid VPNs) – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Best overall VPN for travelers: NordVPN Best VPN for travelers to China: Astrill VPN Best for travelers to Europe: ExpressVPN...
In the rush to build AI apps, please, please don’t leave security behind – Source: go.theregister.com
Source: go.theregister.com – Author: Team Register Feature While in a rush to understand, build, and ship AI products, developers and data scientists are being urged to...
Microsoft again bothers Chrome users with Bing popup ads in Windows – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft is once again harassing Google Chrome users on Windows 10 and Windows 11 with popup desktop advertisements promoting Bing...
Malawi Passport System Back Online After Debilitating Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Rawf8 via Alamy Stock Photo Malawi’s passport issuance system is back online several weeks after...
Windows SmartScreen Bypass Flaw Exploited to Drop DarkGate RAT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: David Chapman via Alamy Stock Photo DarkGate malware operators have been exploiting a now-patched Windows SmartScreen bypass...
How to Identify a Cyber Adversary: What to Look For – Source: www.darkreading.com
Source: www.darkreading.com – Author: Charles A. Garzoni 4 Min Read Source: Chris Baker via Alamy Stock Photo COMMENTARY Cyber-incident attribution gets a lot of attention, for...
150K+ UAE Network Devices & Apps Found Exposed Online – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Birgit Korber via Alamy The rapid adoption of IT and operational technology (OT) by the United Arab...
Claroty Team82: 63% of Known Exploited Vulnerabilities Tracked by CISA Are on Healthcare Organization Networks – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK and ORLANDO, Fla., March 12, 2024/PRNewswire/ —Claroty, the cyber-physical systems (CPS) protection company, released today at the annual...
Codezero Raises $3.5M Seed Funding From Ballistic Ventures to Secure Multicloud Application Development – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE VANCOUVER, BC,March 12, 2024/PRNewswire/ — Codezero, the innovator in secure enterprise microservices development, today announced a $3.5 million seed-funding round led...
Claroty Launches Advanced Anomaly Threat Detection for Medigate – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK and ORLANDO, Fla. — March 12, 2024 — Claroty, the cyber-physical systems (CPS) protection company, today announced at...
10 Tips for Better Security Data Management – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer Whether it is to support compliance efforts for regulatory mandated logging, feed daily security operations center (SOC) work,...
ChatGPT Spills Secrets in Novel PoC Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: PopTika via Shutterstock A team of researchers from Google DeepMind, Open AI, ETH Zurich, McGill University, and...
Yacht Retailer MarineMax Files ‘Cyber Incident’ with SEC – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Kip Evans via Alamy Stock Photo According to the documents it filed...
How to Identify & Monitor Insider Threat Indicators [A Guide] – Source: securityboulevard.com
Source: securityboulevard.com – Author: The Constella Team Most security protocols look outward when looking for cybersecurity threats. But what about threats from inside your organization? Our...
USENIX Security ’23 – Pushed By Accident: A Mixed-Methods Study On Strategies Of Handling Secret Information In Source Code Repositories – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Alexander Krause, Jan H. Klemmer, Nicolas Huaman, Dominik Wermke, Yasemin Acar, Sascha Fahl Many thanks to USENIX for publishing...
Illicit Credentials Marketplace Admin Gets 42-Month Sentence – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Mihir Bagwe (MihirBagwe) • March 15, 2024 A co-administrator of an illicit online...
Ransomware Groups’ Data Leak Blogs Lie: Stop Trusting Them – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware Mathew J. Schwartz (euroinfosec) • March 15, 2024 Ransomware leak sites are not...
Hackers exploit Aiohttp bug to find vulnerable networks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The ransomware actor ‘ShadowSyndicate’ was observed scanning for servers vulnerable to CVE-2024-23334, a directory traversal vulnerability in the aiohttp Python...
TikTok Ban Raises Data Security, Control Questions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: SOPA Images Limited via Alamy Stock Photo Congress voted in favor of banning the popular social media...
Global Threat Intelligence Report March 2024 by Blackberry Cybersecurity
As we enter 2024, we mark a full calendar year of quarterly BlackBerry® Global Threat Intelligence Reports. And what a year it has been. Over the...
Active Directory Security Guide – The Complete Active Directory Security Handbook
Active Directory (AD), introduced with Windows 2000, has become an integral part of modern organizations, serving as the backbone of identity infrastructure for 90% of Fortune...
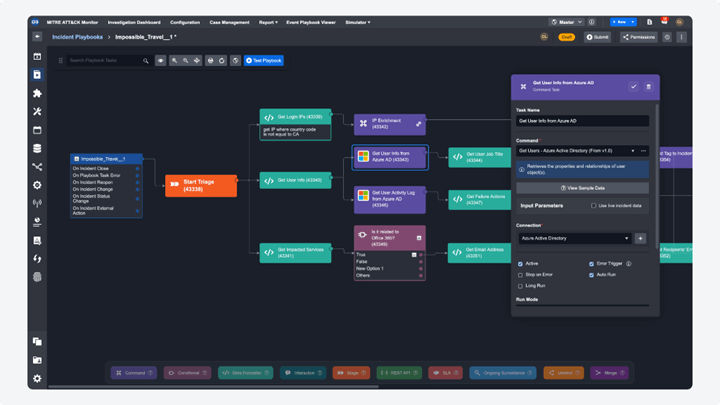
What it’s Like Using Integrations Built by D3 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Pierre Noujeim Integrating a variety of cybersecurity tools and platforms is often a complex and demanding task. This process, essential to the...
International Monetary Fund email accounts hacked in cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The International Monetary Fund (IMF) disclosed a cyber incident on Friday after unknown attackers breached 11 IMF email accounts earlier...
CEO of Data Privacy Company Onerep.com Founded Dozens of People-Search Firms – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The data privacy company Onerep.com bills itself as a Virginia-based service for helping people remove their personal information from almost 200...
Patch Tuesday, March 2024 Edition – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Apple and Microsoft recently released software updates to fix dozens of security holes in their operating systems. Microsoft today patched at...
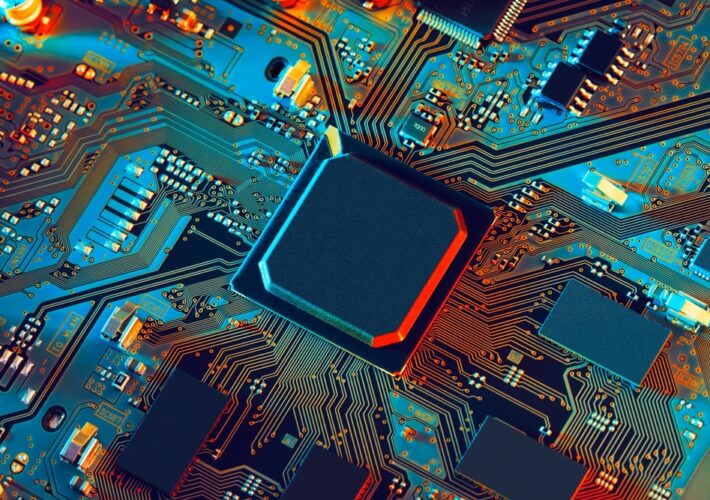
‘GhostRace’ Speculative Execution Attack Impacts All CPU, OS Vendors – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: raigvi via Shutterstock Researchers at IBM and VU Amsterdam have developed a new attack that exploits speculative...
NHS Breach, HSE Bug Expose Healthcare Data in the British Isles – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Panther Media via Alamy Stock Photo This week, a division of the National Health Service (NHS) Scotland...

















![how-to-identify-&-monitor-insider-threat-indicators-[a-guide]-–-source:-securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2024/03/122991/how-to-identify-monitor-insider-threat-indicators-a-guide-source-securityboulevard-com.jpg)