Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added three zero-day vulnerabilities affecting iPhones, Macs, and iPads to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure...
EU hits Meta with $1.3 billion fine for transferring European user data to the US – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The European Union condemned Meta with a record $1.3 billion fine for transferring European user data to the US. The European Union...
Dish Network says the February ransomware attack impacted +300,000 individuals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Satellite TV giant Dish Network disclosed a data breach after the February ransomware attack and started notifying impacted individuals. The...
China bans chip maker Micron from its key information infrastructure – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Chinese government announced the ban on the products made by the US memory chip giant Micron Technology over national...
BatLoader campaign impersonates ChatGPT and Midjourney to deliver Redline Stealer – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers identified an ongoing BatLoader campaign relying on Google Search Ads to deliver rogue web pages for ChatGPT and Midjourney....
Meta fined $1.3B for violating EU GDPR data transfer rules on privacy – Source: www.csoonline.com
Source: www.csoonline.com – Author: The Irish Data Protection Commission has levied a record-breaking fine against Facebook’s parent company, Meta, for transferring data to the US without...
Microsoft reports jump in business email compromise activity – Source: www.csoonline.com
Source: www.csoonline.com – Author: Thirty-five million business email compromise (BEC) attempts were detected in the last year, according to the latest Microsoft Cyber Signals report.
BrandPost: Combining threat intelligence, data at scale, and AI to fortify cyber defenses – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
What cybersecurity professionals can learn from the humble ant – Source: www.csoonline.com
Source: www.csoonline.com – Author: When ants work together to defend their colony, it’s all for one and one for all. This model could help forge an...
Cyber Threat Hunting vs Incident Response: What’s the Difference? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici In today’s cyber world, threats are constantly lurking around every corner. As a result, businesses need to adapt and find...
New Type of Attack: BrutePrint Can Breach Your Smartphone’s Fingerprint Security – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac Chinese researchers discovered a new type of attack targeting smartphones. BrutePrint is a brute-force attack that can bypass fingerprint authentication....
An ounce of prevention is worth a pound of cure – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: It has become painfully obvious that cyber security is critical in enabling clinicians to provide quality care to patients....
Cyber Warfare Lessons From the Russia-Ukraine Conflict – Source: www.darkreading.com
Source: www.darkreading.com – Author: James Turgal, VP of Cyber Risk, Strategy & Board Relations, Optiv The Russia-Ukraine war has taught us a lot about cyber warfare....
Pentagon explosion hoax goes viral after verified Twitter accounts push – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Highly realistic AI-generated images depicting an explosion near the Pentagon that went viral on Twitter caused the stock market to...
Crypto phishing service Inferno Drainer defrauds thousands of victims – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A cryptocurrency phishing and scam service called ‘Inferno Drainer’ has reportedly stolen over $5.9 million worth of crypto from 4,888...
CISA orders govt agencies to patch iPhone bugs exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Today, the U.S. Cybersecurity & Infrastructure Security Agency (CISA) ordered federal agencies to address three recently patched zero-day flaws affecting iPhones,...
EU slaps Meta with $1.3 billion fine for moving data to US servers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Irish Data Protection Commission (DPC) has announced a $1.3 billion fine on Facebook after claiming that the company violated...
An AI-based Chrome Extension Against Phishing, Malware, and Ransomware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Criminal IP The Anti-Phishing Council has reported an increase in phishing reports and URLs, particularly targeting financial institutions. Despite using...
China Issues Ban on US Chipmaker Products – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 China has banned products sold by US chipmaker giant Micron, citing cybersecurity concerns. The Cyberspace Administration of China announced the decision...
Meta Fined €1.2bn for Violating GDPR – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Facebook’s owner Meta has been fined €1.2bn ($1.3m) by EU regulators for violating the General Data Protection Regulation (GDPR), the Irish...
UK Man Sentenced to 13 Years for Running Multi-Million Fraud Website – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A man has been sentenced to 13 years and four months for running a multi-million-pound fraud website that led to at least...
The SaaS Security Future: 3 Ways LLMs are Revolutionizing SaaS – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joseph Thacker, Sr. Offensive Security Engineer @ AppOmni As the digital world continues to evolve with artificial intelligence (AI) innovation, there will...
Facebook Fined $1.3B — Zuckerberg Furious in GDPR Fight – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings No legal way to move Europeans’ data to the US since 2015. Cloud industry better take note. Europe has finally...
Frontline 6.5.4 Updates – Source: securityboulevard.com
Source: securityboulevard.com – Author: Digital Defense by HelpSystems Every release helps update and pave the way for additional features and improvements. Based off of user feedback,...
Cybersecurity Staffing Services: A Key to Protecting Your Business – Source: securityboulevard.com
Source: securityboulevard.com – Author: Geetha R In an increasingly interconnected world, where technology has become an integral part of our daily lives, ensuring the security of...
Who Owns Security in Multi-Cloud Operations? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeff Wierer The best-kept secret is the one that is never shared. In today’s technology environment, that is even more true. Where...
Unleash the power of a CREST accredited penetration testing provider: A Comprehensive Guide – Source: securityboulevard.com
Source: securityboulevard.com – Author: Strobes Blog : Vulnerability Management, Penetration Testing, DevSecOps In today’s world, cyber threats are becoming more frequent and advanced, making it crucial...
Comparing Cloud Providers’ Shared Responsibility Models – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bill Doerrfeld More and more enterprises are becoming multi-cloud. And when evaluating cloud service providers (CSPs) for different needs, one important factor...
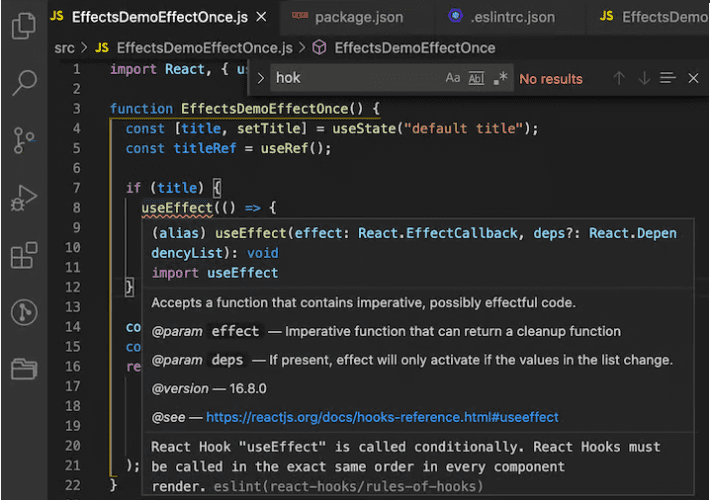
How Do You Handle Side Effects of ReactJS? – Source: securityboulevard.com
Source: securityboulevard.com – Author: UI Designer Using the useEffect To Handle React Side-Effect In ReactJS application development, using the useEffect hook is the most prominent way...
Cloud Computing The Prescription for Modern Healthcare Challenges – Source: securityboulevard.com
Source: securityboulevard.com – Author: seo-ccadmin Cloud computing has become a game-changer for many industries, and healthcare is no exception. Healthcare providers are starting to recognize the...