Source: www.bleepingcomputer.com – Author: Lawrence Abrams The QBot malware operation has started to abuse a DLL hijacking flaw in the Windows 10 WordPad program to infect...
Hot Pixels attack checks CPU temp, power changes to steal data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A team of researchers at Georgia Tech, the University of Michigan, and Ruhr University Bochum have developed a novel attack...
CISA adds recently patched Barracuda zero-day to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added recently patched Barracuda zero-day vulnerability to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security Agency...
Security Affairs newsletter Round 421 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
Is the BlackByte ransomware gang behind the City of Augusta attack? – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The city of Augusta in Georgia, U.S., admitted that the recent IT system outage was caused by a cyber attack. While...
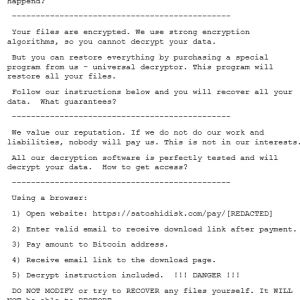
New Buhti ransomware operation uses rebranded LockBit and Babuk payloads – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The recently identified Buhti operation targets organizations worldwide with rebranded LockBit and Babuk ransomware variants. Researchers from Symantec discovered a...
Industrial Giant ABB Confirms Ransomware Attack, Data Theft – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Swiss industrial giant ABB confirmed this week that it was recently targeted in a ransomware attack and that the cybercriminals...
Dental Health Insurer Hack Affects Nearly 9 Million – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Cybercrime , Fraud Management & Cybercrime More than 100 Agencies, Health Entities Impacted by Data Breach Discovered in...
Weekly Update 349 – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt This week’s update is dominated by my experience with “Lena”, the scammer from Gumtree who tried to fleece my wife...
How an innocuous app morphed into a trojan – Week in security with Tony Anscombe – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Editor ESET research uncovers an Android app that initially had no harmful features but months later turned into a spying tool This...
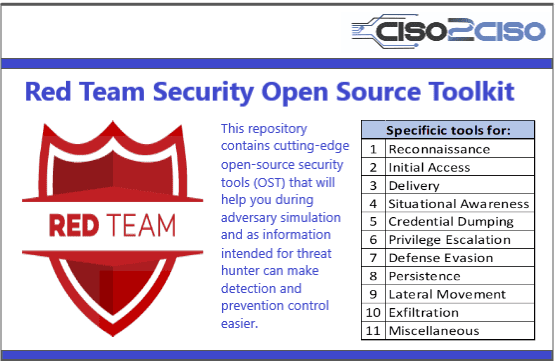
Red Team Security Open Source Toolkit
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BSidesSF 2023 – Alexis Hancock – HSMs in Plain Envelopes: A Code Signing Story – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/05/bsidessf-2023-alexis-hancock-hsms-in-plain-envelopes-a-code-signing-story/ Category & Tags: Security Bloggers Network,appsec education,BsidesSF,BSidesSF...
Live phishing tests not getting the results you want? Here’s what to do. – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scott Wright Well, now what? Many companies will require employees to retake the training or even worse send out more phishing tests...
BSidesSF 2023 – Leif Dreizler – Tracking Meaningful Security Product Metrics – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/05/bsidessf-2023-leif-dreizler-tracking-meaningful-security-product-metrics/ Category & Tags: Security Bloggers Network,appsec education,BsidesSF,BSidesSF...
The Developer’s Guide to Mobile Authentication – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Mobile app developers must ensure that the mobile app is effortless while protecting internal information....
What are FedRAMP Requirements? (And Who Needs to Know) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari For SaaS applications and cloud service providers (CSPs), maintaining compliance with FedRAMP requirements is critical to the bottom line. It...
Daniel Stori’s ‘# $ To Devops Or Not To Devops’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the webcomic talent of the inimitable Daniel Stori at Turnoff.US Permalink *** This is a Security Bloggers Network syndicated...
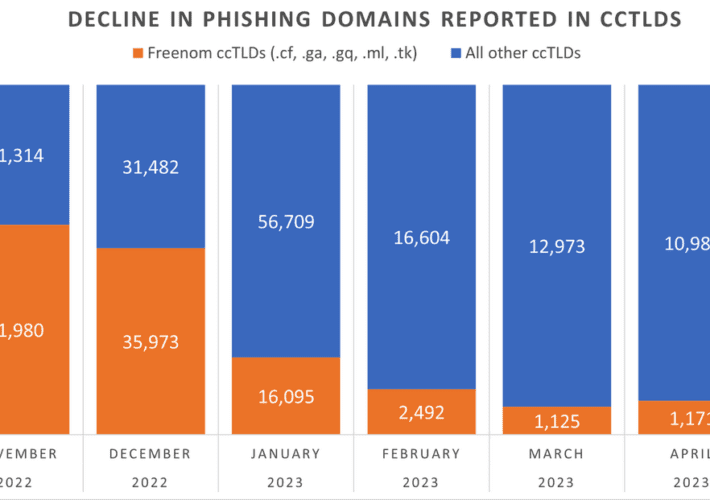
Phishing Domains Tanked After Meta Sued Freenom – Source: securityboulevard.com
Source: securityboulevard.com – Author: BrianKrebs The number of phishing websites tied to domain name registrar Freenom dropped precipitously in the months surrounding a recent lawsuit from...
Are Your Company Secrets Safe on GitHub? Here’s Why You Need to Request a Complimentary Audit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Thomas Segura As a company with a large number of developers, it’s highly likely that some of your company secrets (API keys,...
BSidesSF 2023 – Shobhit Mehta – Lessons Learned While Building a Privacy Operations Center at Headspace Health – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/05/bsidessf-2023-shobhit-mehta-lessons-learned-while-building-a-privacy-operations-center-at-headspace-health/ Category & Tags: Security Bloggers Network,appsec education,BsidesSF,BSidesSF...
Latitude Financial Attack Costs Company Up to AU$105 Million – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Finance & Banking , Fraud Management & Cybercrime Hackers Obtained Access Through a Compromised Credential Mihir Bagwe (MihirBagwe) •...
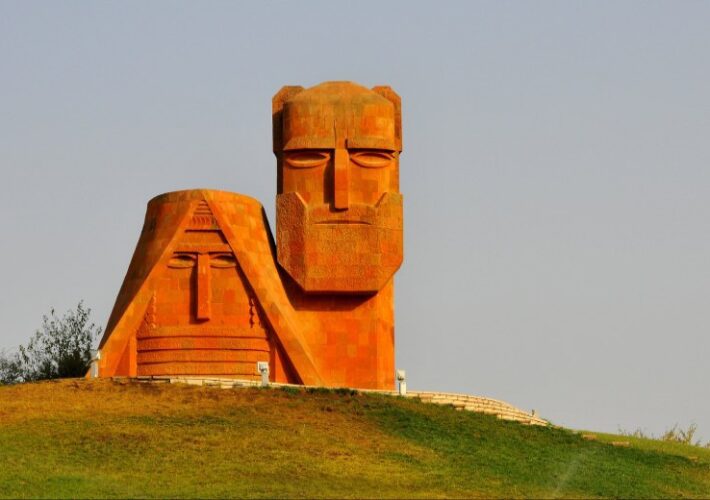
Pegasus Spyware Spotted in Nagorno-Karabakh War – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Access Now Calls Infections 1st Documented Evidence of Pegasus in Context of...
Webinar | Outsmarting the Hackers: Next-Level Strategies for Battling Third-Party Cyber Risks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Chris Holden CISO, Crum & Forster Chris Holden is the Chief Information Security Officer (CISO) for Crum & Forster, a leading...
Medical Specialty Practice Says Recent Hack Affects 224,500 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Ransomware Operation Claims It Downloaded 2 Terabytes of Entity’s Data Marianne Kolbasuk...
Expel, CrowdStrike, Red Canary Dominate MDR Forrester Wave – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Managed Detection & Response (MDR) , Security Operations Secureworks, Binary Defense Tumble From Leaders Category as Winners Start to Emerge Michael...
The Week in Ransomware – May 26th 2023 – Cities Under Attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Ransomware gangs continue to hammer local governments in attacks, taking down IT systems and disrupting cities’ online services. Earlier this month, we...
Microsoft Defender Antivirus gets ‘performance mode’ for Dev Drives – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has introduced a new Microsoft Defender capability named “performance mode” for developers on Windows 11, tuned to reduce the...
Careless IT security worker exploited ransomware attack against his employer, but failed to cover his tracks – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley Bad enough for your company to be held to ransom after a cyber attack. Worse still to then have one...
Organizations Worldwide Targeted in Rapidly Evolving Buhti Ransomware Operation – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A recently identified ransomware operation called Buhti is using LockBit and Babuk variants to target both Linux and Windows systems,...
Google Cloud Users Can Now Automate TLS Certificate Lifecycle – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google on Thursday announced the availability of its Automatic Certificate Management Environment (ACME) API for all Google Cloud users, allowing...