Source: securityaffairs.com – Author: Pierluigi Paganini
The recently identified Buhti operation targets organizations worldwide with rebranded LockBit and Babuk ransomware variants.
Researchers from Symantec discovered a new ransomware operation called Buhti (aka Blacktail) that is using LockBit and Babuk variants to target Linux and Windows systems worldwide.
The ransomware operation hasn’t its own ransomware payload, however, it uses a custom information stealer to target specified file types.
The Buhti operation has been active since February 2023, it was initially spotted attacking Linux systems, but later Symantec’s Threat Hunter Team also identified attacks on Windows computers.
The group was observed quickly exploiting recently disclosed vulnerabilities, such as the recently patched PaperCut vulnerability.
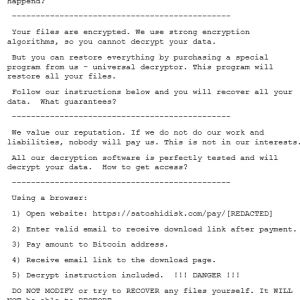
In a recent attack against Windows systems, Buhti operators used a payload that is a modified version of the leaked LockBit 3.0 (aka LockBit Black) ransomware. The builder used by the operators was leaked in September 2022 by a disgruntled developer in response to Russian invasion of the Ukraine.
The ransomware appends the .buthi extension to the encrypted files.
The researchers also observed attacks against Linux systems with Golang-based variants of the Babuk ransomware, which was released on hacking forums in September 2021. This variant used in the attacks targets ESXi systems.
The information stealer used by the group is written in Golang, it allows operators to look for specific files (pdf, .php, .png, .ppt, .psd, .rar, .raw, .rtf, .sql, .svg, .swf, .tar, .txt, .wav, .wma, .wmv, .xls, .xml, .yml, .zip, .aiff, .aspx, .docx, .epub, .json, .mpeg, .pptx, .xlsx, .yaml. ) and then store them in a compressed .ZIP archive.
“The tool can be configured via command-line arguments to specify both the directory to search for files of interest in and the name of the output archive. The -o argument in the command line specifies the archive to be created. The -d argument specifies the directory to search for files of interest in.” reads the post published by Symantec.
The attackers exploited the vulnerability in PaperCut NG and MF (CVE-2023-27350) to install Cobalt Strike, Meterpreter, Sliver, AnyDesk, and ConnectWise hacking tools.
In February, the group was observed exploiting a vulnerability in IBM’s Aspera Faspex file-exchange application (CVE-2022-47986).
“While the reuse of leaked payloads is often the hallmark of a less-skilled ransomware operation, Blacktail’s general competence in carrying out attacks, coupled with its ability to recognize the utility of newly discovered vulnerabilities, suggests that it is not to be underestimated.” concludes the report.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ransomware)
Original Post URL: https://securityaffairs.com/146700/cyber-crime/buhti-ransomware-rebranded-lockbit-babuk.html
Category & Tags: Breaking News,Cyber Crime,Hacking,Malware,Buhti,Cybercrime,hacking news,information security news,IT Information Security,malware,Pierluigi Paganini,ransomware,Security Affairs,Security News – Breaking News,Cyber Crime,Hacking,Malware,Buhti,Cybercrime,hacking news,information security news,IT Information Security,malware,Pierluigi Paganini,ransomware,Security Affairs,Security News
Views: 0