Source: www.govinfosecurity.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy Facebook Sought to Halt Datatilsynet From Imposing Daily Fines...
Constant Vigilance: The Importance of Continuous Cybersecurity Monitoring – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Sean Martin Director of Product Strategy, CSI Business Solutions Group for Managed Services Sean Martin is director of Product Strategy, CSI...
Addressing Security Gaps and Risks Post-M&A in Healthcare – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 In the aftermath of mergers and acquisitions among healthcare entities – and the resulting IT integration and cost-cutting moves – gaps...
OnDemand Panel | Securing Identities in a Zero Trust Environment: A Blueprint for Government Agencies – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Zero Trust Tyler Cohen Wood , David Higgins , Robert Pritchard • September 8, 2023 ...
Webinar | Zero Trust Fundamentals: Start Your Journey Here – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Apple Fixes Zero-Click Bugs Exploited by NSO Group’s Spyware – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security ‘BlastPass’ Can Compromise iPhones Running the Latest iOS Version, Researchers Say Mihir Bagwe (MihirBagwe) • September 8, 2023 ...
ISMG Editors: Reasons to Cheer About Cybersecurity Market – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Healthcare , Industry Specific Also: Feds Out Hospitals Over Tracking Tools; Ongoing Saga of Wiz-SentinelOne Deal Anna Delaney...
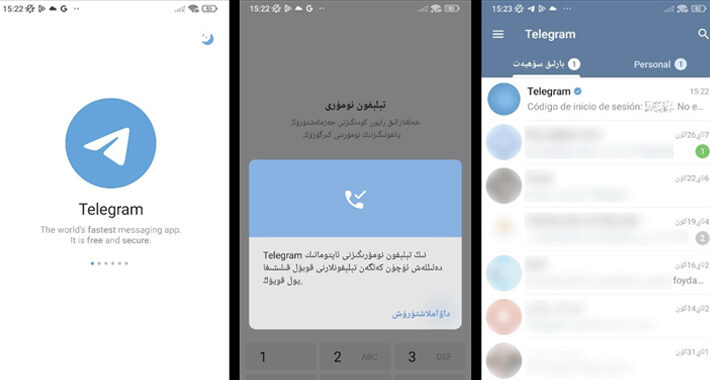
Millions Infected by Spyware Hidden in Fake Telegram Apps on Google Play – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 09, 2023THNMobile Security / Spyware Spyware masquerading as modified versions of Telegram have been spotted in the Google Play Store...
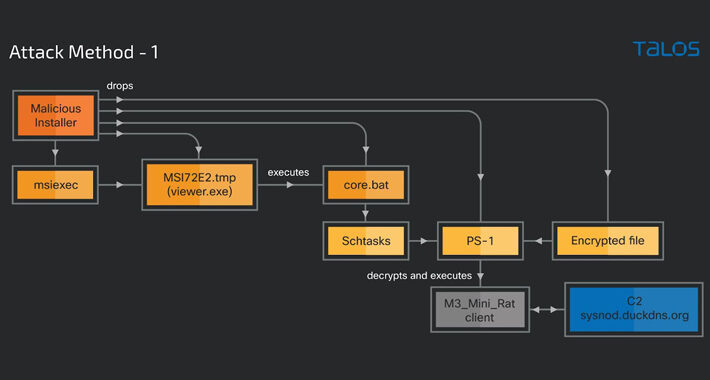
Cybercriminals Weaponizing Legitimate Advanced Installer Tool in Crypto-Mining Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 09, 2023THNMalware / Hacking A legitimate Windows tool used for creating software packages called Advanced Installer is being abused by...
Cisco ASA Zero-Day Exploited in Akira Ransomware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cisco this week raised the alarm on a zero-day in Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software...
New Phishing Campaign Launched via Google Looker Studio – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cybersecurity firm Check Point is warning of a new type of phishing attacks that abuse Google Looker Studio to bypass...
In Other News: LastPass Vault Hacking, Russia Targets Ukraine Energy Facility, NXP Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek is publishing a weekly cybersecurity roundup that provides a concise compilation of noteworthy stories that might have slipped under...
Emsisoft Tells Users to Update Products, Reboot Systems Due to Certificate Mishap – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Endpoint security firm Emsisoft is urging its users to update their anti-malware and other security products and reboot their systems...
US, UK Sanction More Members of Trickbot Russian Cybercrime Group – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The United States and the United Kingdom on Thursday announced sanctions against more alleged members of the Russian cybercrime group...
US Aeronautical Organization Hacked via Zoho, Fortinet Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Advanced persistent threat (APT) actors have exploited known vulnerabilities in Zoho ManageEngine and Fortinet VPN products to hack an organization...
Microsoft, Apple versus China, spyware actors – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg Image: 2ragon/Adobe Stock Revelations this week from Microsoft and Apple speak to the COVID-like persistence of cyber threats and the...
Australian Data Breach Costs are Rising — What Can IT Leaders Do? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Staff Image: Creativa Images/Adobe Stock There’s a good reason Australian organizations are more conscious than ever of the risk of a...
Cisco: Booming identity market driven by leadership awareness – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg Image: leowolfert 85% of IT decision-makers are prioritizing identity and access management investments more highly than other security solutions. This...
Identity Verification vs. Authentication – Source: securityboulevard.com
Source: securityboulevard.com – Author: HYPR Team The recent, numerous high-profile attacks targeting identity processes, like those by the Lapsus$ group, underscore the need for strong identity...
ISO 27001 Implementation Checklist: 10 Tips to Become Certification Ready – Source: securityboulevard.com
Source: securityboulevard.com – Author: Hyperproof Team ISO/IEC 27001 is an information security standard designed and regulated by the International Organization for Standardization, and while it isn’t...
BSides Buffalo 2023 – Dr. Catherine J Ullman – Defending Beyond Defense – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/bsides-buffalo-2023-dr-catherine-j-ullman-defending-beyond-defense/ Category & Tags: CISO Suite,Governance, Risk &...
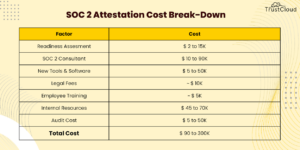
How Much Does it Cost to Get SOC 2? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Satya Moutairou How much does it cost to get SOC 2? A commonly asked question about SOC 2 is “How much does...
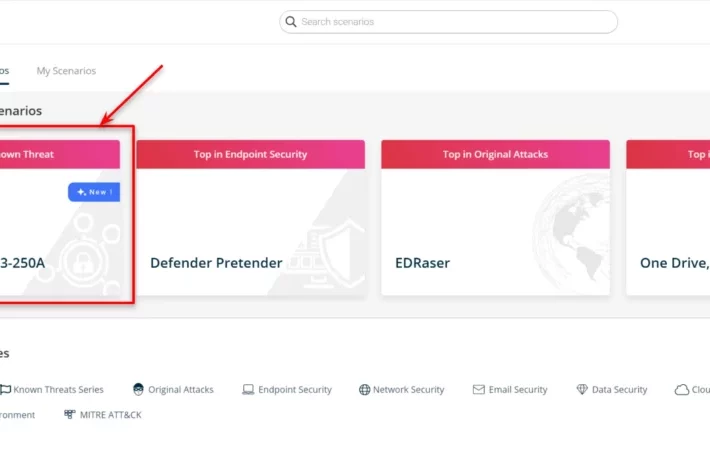
SafeBreach Coverage for US-CERT Alert AA23-250A – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kaustubh Jagtap Author: Kaustubh Jagtap, Product Marketing Director, SafeBreach On September 7, the Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of...
Google Kills 3rd-Party Cookies — but Monopolizes AdTech – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings “Privacy Sandbox” criticized as a proprietary, hypocritical, anti-competitive, self-serving contradiction. Google says its Topics API is ready for prime time:...
Cybersecurity Insights with Contrast CISO David Lindner | 9/8 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 Prompt injection is becoming a serious concern for those using current AI technologies. When using...
Daniel Stori’s ‘Advanced-Species’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/daniel-storis-advanced-species/ Category & Tags: Humor,Security Bloggers Network,Daniel Stori,Erlang...
BSides Buffalo 2023 – Zack Glick – How to Read a Breach Notification – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/bsides-buffalo-2023-zack-glick-how-to-read-a-breach-notification/ Category & Tags: CISO Suite,Governance, Risk &...
Emsisoft to Users: Update Software, Reboot Systems After Certificate Error – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Cybersecurity firm Emsisoft is telling users to update their anti-virus and other security software in the wake of an error...
Why Australian companies need to adopt zero trust… now – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Sadiq Iqbal, Security Engineering Manager and Check Point Evangelist. It might be on the ‘to-do’ lists of many CISOs, yet...
Friday Squid Blogging: Glass Squid Video – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments seigler1 • September 8, 2023 5:58 PM re The SURVEILLANCE STATE …What specific citizen right does 4th AMENDMENT...