Source: www.techrepublic.com – Author: Karl Greenberg

85% of IT decision-makers are prioritizing identity and access management investments more highly than other security solutions. This is according to the CISO Survival Guide by Cisco’s startup arm, Cisco Investments, with cybersecurity venture capital firms Forgepoint Capital, NightDragon and Team8.
The guide, which explored the cybersecurity market around identity management, data protection, software supply chain integrity and cloud migration, resulted from interviews with Cisco customers, chief information security officers, innovators, startup founders and other experts.
The 30,000-foot view: Interviewees said that, above all, they need more interoperability and less friction, and data that is actually useful and comprehensible for decision-makers.
The key spending priorities the report unearthed constituted a fairly even split, with user and device identity being cited by the largest number of CISOs, followed by cloud identity, governance and remote access.
Cloud security is the top concern, with the emerging area of cloud infrastructure entitlements management an area of special interest.
Jump to:
- What CISOs want: Ease of use, holistic platforms, CIEMs
- Top motivators for identity management solutions
- Choices, choices: Exploding options and growing complexity are blockers
- Nothing to fear but fear itself?
- Other findings: Those who have access to information have the keys to security
- Shifting IT from cost to innovation center
What CISOs want: Ease of use, holistic platforms, CIEMs
The key areas CISOs consider to be of most concern around identity access management, clouds and data are:
- The fragmented world of security silos is due to a paucity of unified platforms covering IAMs, identity governance and administration and privileged access management.
- Cloud infrastructure entitlements management is ascendent and enterprise customers are adopting those that are offered by cloud service providers.
- Can we please nix the acronyms? CISOs are chafing at the proliferation of acronyms like CIEM.
On that last point, the authors of the Cisco Investment Study note, “This trend imposes cycles for CISOs to vet and unpack these purportedly new categories, only for them to discover they are a rehash of existing solutions.”
Top motivators for identity management solutions
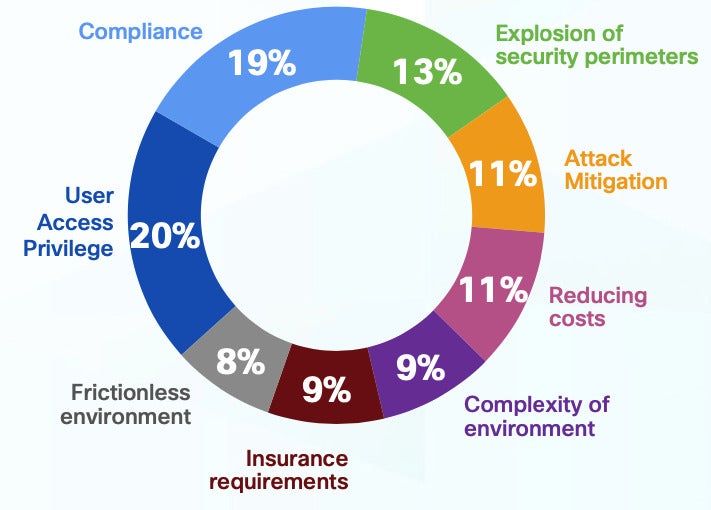
The top motivators that CISOs cited for investing in identity management solutions are managing user access privileges, identity compliance and the rapid growth of organizations’ threat surfaces (Figure A).
Figure A
Here’s what IT decision makers are looking for in next-generation identity platforms, according to the study:
- Ease of integration (21% of those polled).
- Platform based solution, versus single-point or endpoint offerings (15%).
- Ratings from independent analysts (15%).
- Price (11%).
- Market adoption (11%).
- Simplicity of deployment and operations (10%).
- Ability to deploy at scale easily (9%).
- Ability to add features easily (8%).
Choices, choices: Exploding options and growing complexity are blockers
It is also not surprising that the majority of CISOs are stymied in achieving access and management goals by the sheer number of tools available and the growing complexity of their own operations.
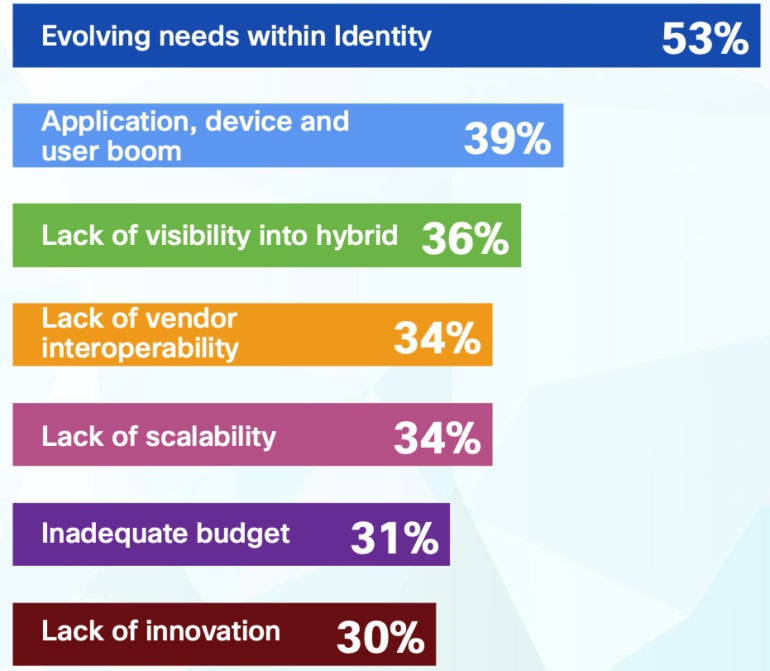
The study noted that over one-third of the IT security decision makers said the cornucopia of identity and access solutions and the increasing number of devices and users involved make adopting access management tools more challenging. 53% of the CISOs polled for the report said they are challenged by “evolving identity needs” (Figure B).
Figure B
Nothing to fear but fear itself?
Cisco offered some suggestions for companies stymied by choices and afraid of the implications of applying zero trust to their complex organizations, including downtime caused by the mechanics of integrating new protocols: Chill, it’s not as bad as you think.
“What I’ve seen with new technologies is that everyone is afraid of them, but when you start putting them in place, there’s much less to be afraid of than CISOs initially thought,” said Larry Lidz, Cisco’s cloud CISO, in the report. “So, I think that the fear of adoption is much higher than the actual noise around adopting it.”
Other findings: Those who have access to information have the keys to security
In the study, Forgepoint analysts said controlling access to information remains the crux of cybersecurity, with data identity and privileged access management being top priority for CISOs. They noted that data security represents yet another hub category with many spokes, including data access control and data loss prevention.
SEE: Explore these cloud security best practices.
NightDragon looked at the software supply chain: 55% of respondents said they placed compliance among their top three software supply chain concerns.
“Companies must create a holistic software supply chain strategy to manage the load,” said the NightDragon report. “Ultimately, this involves managing OS code, the delivery pipeline and third-party software — again, in a unified approach.”
Shifting IT from cost to innovation center
Forgepoint noted that as organizations integrate security into business objectives, CISO’s roles will change to become less about justifying IT investments and more about making these initiatives a driver of strategic goals beyond “just” cybersecurity.
To that point, Cisco last week launched a Lifecycle Services program meant to help organization decision-makers at the highest levels understand how IT can be more than a ledger item in the cost column.
Driven by machine learning and artificial intelligence telemetry, according to Cisco, the service is designed to help CISOs bring return on investment data to bear on how they communicate the business value of IT. By doing so, the company noted, the conversation shifts from one about justifying the cost of technology to how it is essential to innovation toward an organization’s goals.
SEE: Download our guide on the CISO security threat landscape.
“Too often IT is focused on the delivery of new technologies and platforms, rather than business objectives, benefits and outcomes,” said Cisco.
Cisco said Lifecycle Services will help IT leaders scale technology strategies that support top business priorities across their organization by giving them access to Cisco experts, proprietary digital insights, ML/AI tools and measurement best practices to report on KPIs in support of the overall business mission and goals of the organization.
“Increasingly, organizations need the flexibility to consume on-demand services in order to deliver greater value and enhanced experience for their customers,” said Leslie Rosenberg, vice president of network life-cycle services and infrastructure services at IDC. “The Lifecycle Services offer from Cisco provides businesses the ability to align their priorities with clear and measurable outcomes to ensure their technology investments support their business, technology and operational goals.”
Original Post URL: https://www.techrepublic.com/article/cisco-collaborative-startup-guide/
Category & Tags: Cloud,CXO,Security,ai,artificial intelligence,ciem,cisco,ciso,cloud infrastructure,cloud infrastructure entitlements management,cloud security,cybersecurity,data loss prevention,data security,dlp,identity access management,identity management,machine learning,security,zero trust – Cloud,CXO,Security,ai,artificial intelligence,ciem,cisco,ciso,cloud infrastructure,cloud infrastructure entitlements management,cloud security,cybersecurity,data loss prevention,data security,dlp,identity access management,identity management,machine learning,security,zero trust
Views: 1




















































