Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading A global cyber-espionage campaign conducted by the Iranian nation-state actor known as Peach Sandstorm (aka Holmium)...
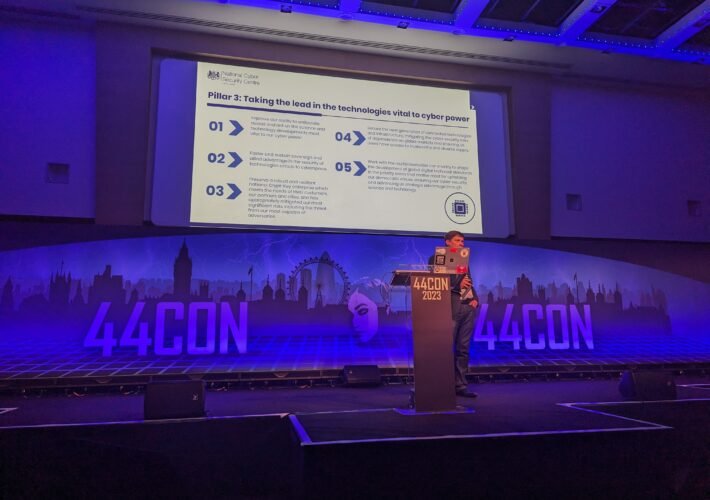
NCSC: Why Cyber Extortion Attacks No Longer Require Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading 44CON 2023 – London – Cyber attackers are becoming less reliant on ransomware to get victims...
Two New York Hospitals Breached by the LockBit Ransomware Group – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu The notorious LockBit ransomware group claims to have breached two major hospitals from upstate New York, the Carthage Area Hospital...
What Effect Does Firm Size Have on Ransomware Threats? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Gabriella Antal In an increasingly digital world, the threat of ransomware looms large over organizations of all sizes. However, the impact of...
5 Examples of DNS IoCs That Are Red Flags for Cyberattacks – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși In the increasingly digitalized world that we live in, doing business without being connected 24/7 is almost unthinkable. Any medium...
ISMG Editors: Are Frequently Used Usernames a Security Risk? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Access Management , Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Also; The ‘Quantum Divide’; Global AI Regulatory...
Enhancing Cloud Security on AWS – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Security Operations Why You Should Consider a Cloud-Native Firewall Service Frederick Harris, Senior Director, Products & Solutions Marketing,...
Critical Considerations for Generative AI Use in Healthcare – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Healthcare , Industry Specific Barbee Mooneyhan of Woebot Health on the Need for Strong AI...
Iranian Hackers Gain Sophistication, Microsoft Warns – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Noisy ‘Peach Sandstorm’ Password Spraying Campaign Is Followed by Stealth Mihir Bagwe...
Live Webinar | Protecting Devices and Software from Next-Generation Cyberthreats – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Device Identification , Endpoint Security , Hardware / Chip-level Security Presented by DigiCert 60 mins IoT devices,...
Live Webinar | Leveraging MITRE’s 2023 ATT&CK Evaluation to Supercharge Your Security Strategy – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Caesars Confirms Ransomware Payoff and Customer Data Breach – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Critical Infrastructure Security , Cybercrime MGM Resorts Continuing to Be Extorted by the Same Alphv/BlackCat Ransomware Group Mathew...
Lessons to Learn From Clop’s MOVEit Supply-Chain Attacks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Governance & Risk Management Data Minimization and Encryption Mitigate Fallout, Says FS-ISAC’s Teresa Walsh Mathew J....
LLM Summary of My Book Beyond Fear – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bruce Schneier Claude (Anthropic’s LLM) was given this prompt: Please summarize the themes and arguments of Bruce Schneier’s book Beyond Fear. I’m...
Attackers Target Crypto Companies in Retool Data Breach – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A data breach late last month of software development platform firm Retool led to the accelerated acquisition of one of...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – The Israel Healthcare Cybersecurity Summit (IHCS) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
Cybersecurity Insights with Contrast CISO David Lindner | 9/15 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1 Software Bills of Materials (SBOMs) are nothing more than a data point for determining risk....
Randall Munroe’s XKCD ‘Exoplanet Observation’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
The Hidden Dangers of Remote Code Execution (RCE) Exploits in Word Documents – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team Remote code execution (RCE) attacks within Word documents have long been a part of the attacker’s arsenal. Their prevalence stems...
BSides Buffalo 2023 – Richard Smith – Enriching Your SOC Investigations With Insights From Active Directory – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
Cyberthreat Intelligence: Are Telecom Networks Easy Targets? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ashish Nainwal In a 5G world, cybersecurity is needed more than ever to protect networks, data and users from threats. There are...
Cybersecurity Goals Conflict With Business Aims – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Cybersecurity is often out of sync with business goals, according to a study conducted by Forrester Consulting, which found 97% of organizations...
Extradited Russian Hacker Behind ‘NLBrute’ Malware Pleads Guilty – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Russian hacker Dariy Pankov has pleaded guilty to computer fraud and now faces a maximum penalty of five years in...
Pentagon’s 2023 Cyber Strategy Focuses on Helping Allies – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Department of Defense (DoD) this week published an unclassified summary of its 2023 Cyber Strategy, outlining plans for...
California Settles With Google Over Location Privacy Practices for $93 Million – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Search giant Google agreed to a $93 million settlement with the state of California on Thursday over its location-privacy practices....
In Other News: China Blames NSA for Hack, AI Jailbreaks, Netography Spin-Off – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs SecurityWeek is publishing a weekly cybersecurity roundup that provides a concise compilation of noteworthy stories that might have slipped under...
Deduce Raises $9 Million to Fight AI-Generated Identity Fraud – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Identity fraud prevention provider Deduce this week announced that it has raised $9 million in a new funding round that...
MGM Hackers Broadening Targets, Monetization Strategies – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google-owned Mandiant says the financially motivated threat actor responsible for the recent MGM Resorts hack has been expanding its targets,...
Google Feature Blamed for Retool Breach That Led to Cryptocurrency Firm Hacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A recently introduced Google account sync feature has been blamed by software development firm Retool after sophisticated hackers gained access...
Caesars Confirms Ransomware Hack, Stolen Loyalty Program Database – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Caesars Entertainment, Inc., a well-known global hospitality brand, has been hacked by a cybercrime gang that stole a vast chunk...