Source: securityaffairs.com – Author: Pierluigi Paganini Recent cyber attack is causing Clorox products shortage Pierluigi Paganini September 19, 2023 The cyber attack that hit the cleaning...
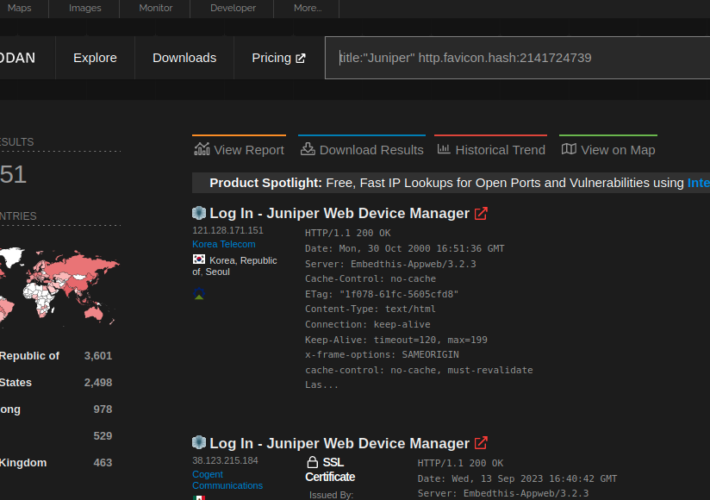
12,000 Juniper SRX firewalls and EX switches vulnerable to CVE-2023-36845 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini 12,000 Juniper SRX firewalls and EX switches vulnerable to CVE-2023-36845 Pierluigi Paganini September 19, 2023 Researchers discovered approximately 12,000 Juniper...
Signal Messenger Introduces PQXDH Quantum-Resistant Encryption – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNEncryption / Privacy Encrypted messaging app Signal has announced an update to the Signal Protocol to add support for...
GitLab Releases Urgent Security Patches for Critical Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNVulnerability / Software Security GitLab has shipped security patches to resolve a critical flaw that allows an attacker to...
Trend Micro Releases Urgent Fix for Actively Exploited Critical Security Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNZero Day / Vulnerability Cybersecurity company Trend Micro has released patches and hotfixes to address a critical security flaw...
Detecting AI-Generated Text – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier There are no reliable ways to distinguish text written by a human from text written by an large language model....
Improper Usage of SAS Token Leads to Massive Microsoft Data Leakage – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Microsoft researchers leaked 38TB of sensitive data to a public GitHub repository while training open-source AI learning models. The Microsoft...
How to Create and Use a Docker Secret From a File – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Jack Wallen TechRepublic Premium TechRepublic Premium Troubleshooting Backup Routines Backup routines are the lifeblood of information technology. Protecting an organization’s data is...
How to Create and Use a Docker Secret From a File (+Video) – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Jack Wallen on September 19, 2023, 9:57 AM EDT How to Create and Use a Docker Secret From a File (+Video) In...
macOS Tune-Up Checklist – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Macs, like Windows computers, benefit from routine maintenance. Regular tune-ups help protect Macs, both desktop and laptop models, from potential data loss,...
Apptega Lands 39 Badges, including GRC Momentum Leader, in Fall G2 Reports – Source: securityboulevard.com
Source: securityboulevard.com – Author: Natalie Anderson Apptega, the end-to-end GRC platform for forward-thinking IT and managed service providers, earned 39 high-performer and momentum leader badges in G2’s...
LockBit Affiliates Use RMM Software in Ransomware Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Affiliates of the Russia-linked LockBit ransomware group are using remote monitoring and management (RMM) software to distribute its malicious payload...
Black Hat: Stephen Chin, JFrog – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alan Shimel Speaker 1: This is Techstrong TV. Alan Shimel: Hey everyone. We’re back here live in our Mandalay Bay suite at...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – AI & Cyber – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-ai-cyber/ Category & Tags: CISO Suite,Governance, Risk &...
Black Hat: Deepen Desai, Zscaler – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mitchell Ashley Speaker 1: This is Techstrong TV. Mitch Ashley: Hey, everybody, Mitch Ashley. I am at the Mandelay Bay Suite, the...
Unmasking Reverse Proxy Phishing: Protecting Your Online Identity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Casey Joyce Phishing attacks have long been a major concern in the cybersecurity landscape. These malicious attempts to steal sensitive information often...
What security or other risks might you encounter with IoT? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction In today’s rapidly evolving digital landscape, the surge of Internet of Things (IoT) devices stands out as a transformative...
CrowdStrike Extends Scope of Managed Cybersecurity Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard At its Fal.Con 2023 conference, CrowdStrike made a host of announcements, including the addition of a slew of capabilities to...
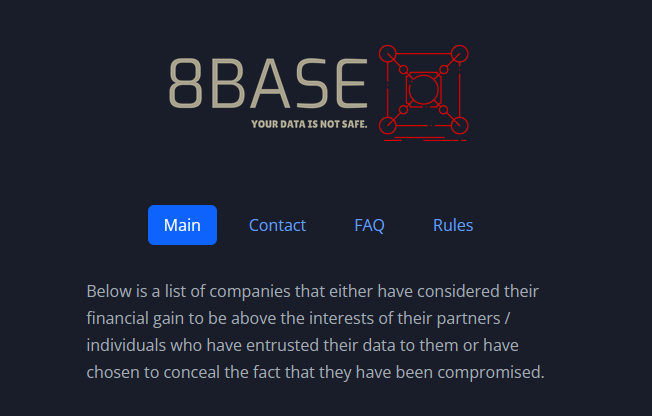
Who’s Behind the 8Base Ransomware Website? – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The victim shaming website operated by the cybercriminals behind 8Base — currently one of the more active ransomware groups — was...
Expert: Keep Calm, Avoid Overhyping China’s AI Capabilities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development China’s Ability to Diffuse AI Across Economy Lags Ability to...
Journey to the Cloud: Navigating the Transformation – Part 2 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Security Operations Nikko Asset Management’s Marcus Rameke on the Advantages of HCI On-Premises CyberEdBoard • September 19, 2023...
Generative AI: Embrace It, But Put Up Guardrails – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Standards, Regulations & Compliance Cisco’s Pam Lindemoen and Daniel...
Why Entities Should Review Their Online Tracker Use ASAP – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Healthcare , HIPAA/HITECH Nick Heesters of HHS OCR on the Agency’s Top Areas of HIPAA Scrutiny...
Cyber Experts Urge House Committee to Avoid Federal Shutdown – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Cybersecurity Spending , Government Annual Federal Funding Will Expire in 12 Days Marianne Kolbasuk McGee (HealthInfoSec) •...
CrowdStrike to Buy AppSec Startup Bionic for Reported $350M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Security Operations Deal Will Offer Visibility Into Application Behavior, Vulnerability Prioritization Michael Novinson (MichaelNovinson) • September 19, 2023...
China-Linked Actor Taps Linux Backdoor in Forceful Espionage Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading “Earth Lusca,” a China-linked cyber espionage actor that’s been actively targeting government organizations in Asia, Latin...
Trend Micro Patches Zero-Day Endpoint Vulnerability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Trend Micro has released an advisory covering a critical zero-day flaw — tracked as CVE-2023-41179 — that...
MGM, Caesars Face Regulatory, Legal Maze After Cyber Incidents – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading In the wake of the new Securities and Exchange Commission (SEC) regulatory requirements to disclose “material” cyber...
Qatar Cyber Chiefs Warn on Mozilla RCE Bugs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The National Cyber Security Agency in Qatar is warning Adobe users to urgently apply patches following the...
Name That Toon: Somewhere in Sleepy Hollow – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Harken, readers! ‘Tis you we love! Come up with a clever cybersecurity-related caption for the cartoon, above! (Our favorite...