Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading The rise of cloud applications and infrastructure makes the Web browser the logical place for instituting...
MGM Restores Casino Operations 10 Days After Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cha-ching! MGM Resorts’ hotel and casino operations are back in business following a devastating ransomware attack. Operations,...
Growing Chinese Tech Influence in Africa Spurs ‘Soft Power’ Concerns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Chinese companies are rapidly deploying technology to enable telecommunications, mobile payments, smart cities and underwater fiber...
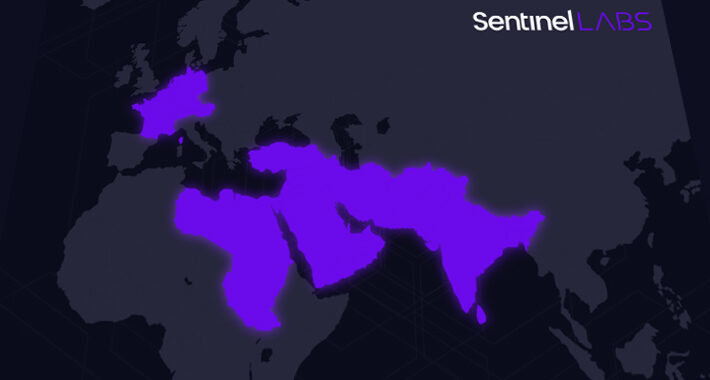
‘Sandman’ hackers backdoor telcos with new LuaDream malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A previously unknown threat actor dubbed ‘Sandman’ targets telecommunication service providers in the Middle East, Western Europe, and South Asia,...
GitHub passkeys generally available for passwordless sign-ins – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan GitHub has made passkeys generally available across the platform today to secure accounts against phishing and allow passwordless logins for...
Apple emergency updates fix 3 new zero-days exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Apple released emergency security updates to patch three new zero-day vulnerabilities exploited in attacks targeting iPhone and Mac users, for...
Microsoft Copilot rolls out with Windows 11 22H2 update next week – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft will start rolling out its Copilot digital assistant to all customers next week, on September 26th, together with a...
Pizza Hut Australia warns 193,000 customers of a data breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Pizza Hut Australia is sending data breach notifications to customers, warning that a cyberattack allowed hackers to access their personal...
Unlocking the Future of Cybersecurity: Meet Us at GovWare 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS Today’s ever-evolving digital landscape presents unparalleled opportunities alongside formidable cybersecurity challenges, making the security of organizations’ networks and applications more crucial....
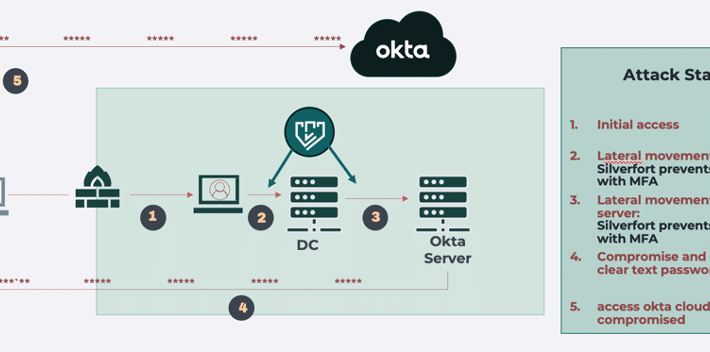
MGM Breach Takeaway: On-Prem Has Become Attackers’ Gateway to the Cloud – Source: securityboulevard.com
Source: securityboulevard.com – Author: Don Hoffman Last week, the BlackCat ransomware group (also known as ALPHV) attacked the operations of MGM Resorts and forced them to...
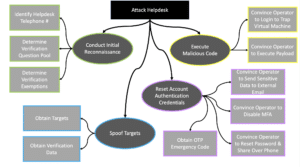
Helpdesk Telephone Attack: How to Close Process and Technology Gaps – Source: securityboulevard.com
Source: securityboulevard.com – Author: emmaline Introduction As we have witnessed in recent weeks with the MGM and Caesars Entertainment breaches, helpdesks are prime attack surfaces that...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Watch Live: Cyber Week 2023 — Main Plenary, Day 1 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-watch-live-cyber-week-2023-main-plenary-day-1/ Category & Tags: CISO Suite,Governance, Risk &...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – FraudCON (Virtual) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-fraudcon-virtual/ Category & Tags: CISO Suite,Governance, Risk &...
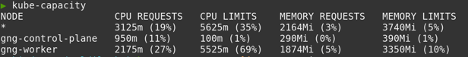
Building a Kubernetes Platform: How to Handle Cost Management & Reporting – Source: securityboulevard.com
Source: securityboulevard.com – Author: Stevie Caldwell Platforms, sometimes called internal developer platforms, are a unified infrastructure that allows all the development teams you have in your...
OWASP Top 10 IoT Vulnerabilities: How to Avoid Them! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction In today’s interconnected world, understanding the OWASP Top 10 IoT vulnerabilities is crucial, especially for small businesses striving to...
New Capabilities with the September Release of the HYAS Platform – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Needs New Product Release News You use the HYAS platform today to better protect and defend your organization from cyber threats...
SAST vs. DAST: Enhancing application security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/sast-vs-dast-enhancing-application-security/ Category & Tags: Application Security,DevOps,Security Bloggers Network,DAST,DevZone,SAST,security...
A Deep Dive into ARMOR Level 3: Automated Response – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joel Wong At Swimlane, “armor” takes on a distinct meaning. It represents automation readiness and maturity of orchestrated Resources (ARMOR). In today’s...
Feds Warn About Snatch Ransomware – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware US Agency Advisory Sheds Light on the Group’s Activities Prajeet Nair (@prajeetspeaks) • September 21,...
Journey to the Cloud: Navigating the Transformation – Part 3 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Security Operations Nikko Asset Management’s Marcus Rameke on SaaS or PaaS vs. IaaS or On-Premises HCI CyberEdBoard •...
Canada Confirms DDoS Attack Disrupted Airport Arrival Kiosks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , DDoS Protection , Fraud Management & Cybercrime How in the World Did Self-Proclaimed Hacktivists Hit System...
Dutch Police Warns Users of Credentials Leak Site – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime 400 Potential WeLeakInfo Patrons Warned of Legal Costs of Criminal Wrongdoing Akshaya Asokan (asokan_akshaya) •...
Cryptohack Roundup: Private Key Compromise Led to CoinEx Hit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Mark Cuban Hot Wallet Hack; Crypto Regulation Mihir Bagwe...
Ohio Community College Data Theft Breach Affects Nearly 300K – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Government , Healthcare Researchers Say Breach Illustrates Why Schools Are Major Targets for Cybercriminals Marianne Kolbasuk...
Intel Innovation 2023: Attestation and Fully Homomorphic Encryption Coming to Intel Cloud Services – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse The attestation service is designed to allow data in confidential computing environments to interact with AI safely, as well as...
Top 5 Ways to Secure Work Data on Your Personal Mac – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Mackenzie Burke Top 5 Ways to Secure Work Data on Your Personal Mac About Top 5 Ways to Secure Work Data on...
Retailers Are Rapidly Scaling Surveillance of Australian Consumers — Why This Is a Red Flag – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Matthew Sainsbury IT professionals across sectors that interact with consumers, and retail in particular, need to make themselves aware of the implications...
SSL Certificate Best Practices Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: SSL certificates are essential for encrypting traffic between systems such as clients, which access servers via web browsers or applications that communicate...
Computer Security Incident Response Team (CSIRT): How to Build One – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac According to the World Economic Forum, “widespread cybercrime and cyber insecurity” is rated as one of the greatest worldwide dangers...
Mysterious ‘Sandman’ Threat Actor Targets Telecom Providers Across Three Continents – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 21, 2023THNTelecom Security / Cyber Attack A previously undocumented threat actor dubbed Sandman has been attributed to a set of...