Source: www.govinfosecurity.com – Author: 1 Presented by VMware 300 Minutes Learn how to navigate the cloud landscape with VMware, your compass for...
Cloud Smart Roadshow Irving Texas: Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Presented by VMware Learn how to navigate the cloud landscape with VMware, your compass for a cloud-smart journey. You know how...
Researchers Discover Attempt to Infect Leading Egyptian Opposition Politician With Predator Spyware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press A leading Egyptian opposition politician was targeted with spyware after announcing a presidential bid, security researchers reported Friday. They said...
Alphv group claims the hack of Clarion, a global manufacturer of audio and video equipment for cars – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Alphv group claims the hack of Clarion, a global manufacturer of audio and video equipment for cars Pierluigi Paganini September 24,...
Security Affairs newsletter Round 438 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
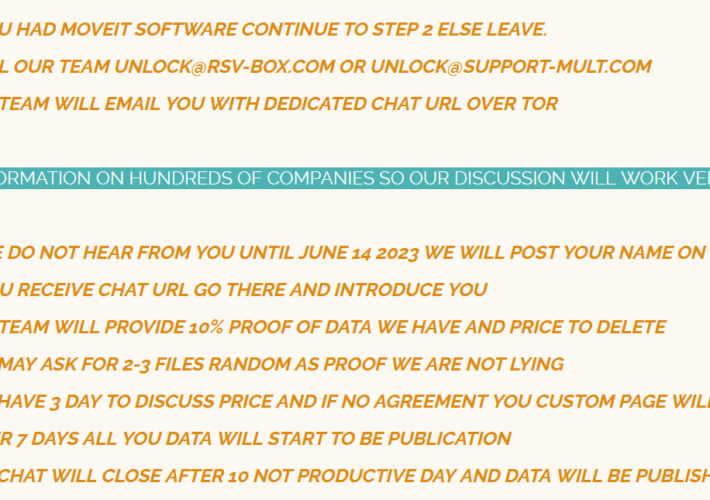
National Student Clearinghouse data breach impacted approximately 900 US schools – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini National Student Clearinghouse data breach impacted approximately 900 US schools Pierluigi Paganini September 24, 2023 U.S. educational nonprofit organization National...
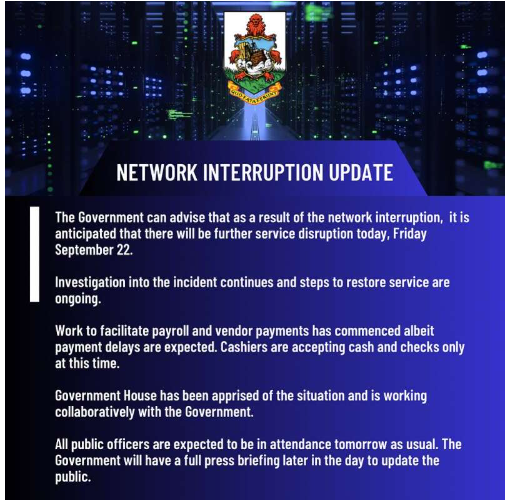
Government of Bermuda blames Russian threat actors for the cyber attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Government of Bermuda blames Russian threat actors for the cyber attack Pierluigi Paganini September 23, 2023 The Government of Bermuda...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – AI Governance in the Wake of ChatGPT – Policy and Governance – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-ai-governance-in-the-wake-of-chatgpt-policy-and-governance/ Category & Tags: CISO Suite,Governance, Risk &...
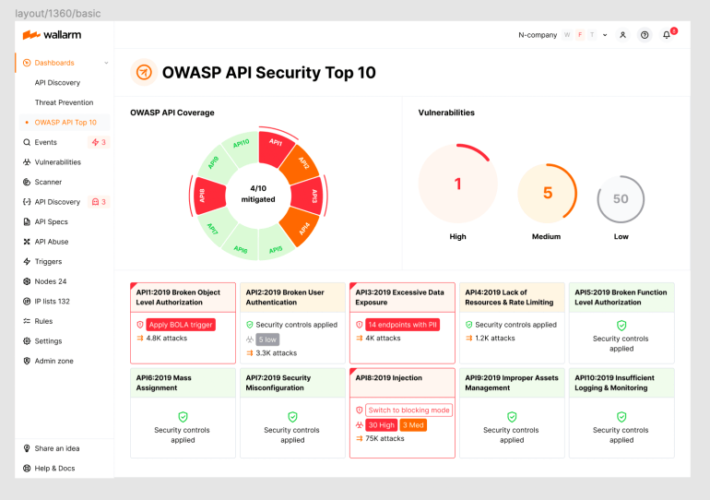
2023 OWASP Top-10 Series: API9:2023 Improper Inventory Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog Welcome to the 10th post in our weekly series on the new 2023 OWASP API Security Top-10 list, with a particular...
The Role of AI and Machine Learning in Strengthening Cloud Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Solvo Cloud computing has become essential for modern business operations, offering flexibility, scalability, and accessibility for data storage, processing, and application...
Is DevSecOps Just DevOps Reinvented? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kimberly Rose The advent of DevOps—short for Development and Operations—provided an efficient approach for streamlining the software delivery pipeline. DevOps has achieved...
What is CMDB? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi In the dynamic realm of IT infrastructure and network management, the CMDB has emerged as a crucial tool for IT...
Web Application Firewall vs Firewall: What You Need to Know – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction In today’s interconnected world, the significance of cybersecurity cannot be overstated. This is especially true as cyber threats continue...
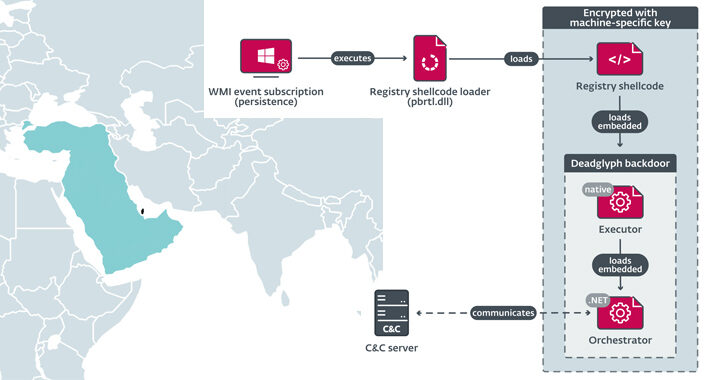
Deadglyph: New Advanced Backdoor with Distinctive Malware Tactics – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers have discovered a previously undocumented advanced backdoor dubbed Deadglyph employed by a threat actor known as Stealth Falcon as...
Apple Fixes Bugs That Infected Egyptian Politician’s iPhone – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Next-Generation Technologies & Secure Development , Threat Intelligence Cytrox’s Predator Found on Device of Ahmed Eltantawy Mihir Bagwe...
Cato Networks Raises $238M on $3B Valuation to Move Upmarket – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Access Security Brokers (CASB) , Data Loss Prevention (DLP) , Endpoint Security Equity Investment Will Allow Cato Networks to Tightly...
Cloud Smart Roadshow Bellevue (Seattle): Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Data Security & Resilience , Cloud Security , DevSecOps Presented by VMware 300 Minutes Learn how...
Cloud Smart Roadshow Costa Mesa (Irvine): Practical Strategies for a Simplified and Secured Cloud Journey – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Data Security & Resilience , Cloud Security , DevSecOps Presented by VMware 300 Minutes Learn how...
Chinese, North Korean Nation-State Groups Target Health Data – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Healthcare HHS Report Lists APT41, APT43 and Lazarus Among Top Threat...
Google CISO Phil Venables on Building Strong CIO-CISO Bonds – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Leadership & Executive Communication , Training & Security Leadership , Video CIO, CISO Must Join Forces to Upgrade Organization to More...
Evasive Gelsemium hackers spotted in attack against Asian govt – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A stealthy advanced persistent threat (APT) tracked as Gelsemium was observed in attacks targeting a Southeast Asian government that spanned...
National Student Clearinghouse data breach impacts 890 schools – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan U.S. educational nonprofit National Student Clearinghouse has disclosed a data breach affecting 890 schools using its services across the United...
Air Canada discloses data breach of employee and ‘certain records’ – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Image Credit: John McArthur (Unsplash) Air Canada, the flag carrier and the largest airline of Canada, disclosed a cyber security incident...
MGM, Caesars Cyberattack Responses Required Brutal Choices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Twin cyberattacks on MGM Resorts and Caesars Entertainment have provided a singular view into what happens when...
Bot Swarm: Attacks From Middle East & Africa Are Notably Up – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The number of reported bot attacks originating from the Middle East and Africa increased over the...
Guardians of the Cyberverse: Building a Resilient Security Culture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dr. Sean Costigan, Director of Cyber Policy, Red Sift Amid relentless cyberattacks and mounting regulatory pressures, security culture has been thrust into...
Do CISOs Have to Report Security Flaws to the SEC? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Evan Schuman, Contributing Writer, Dark Reading Now that the SEC wants to know about any material security incidents within four days of...
Mastering Defense-in-Depth and Data Security in the Cloud Era – Source: www.darkreading.com
Source: www.darkreading.com – Author: Liat Hayun, Co-Founder & CEO, Eureka Security Defense-in-depth is not a new concept in cybersecurity. Borrowed from military terminology, it was created...
BBTok Banking Trojan Impersonates 40+ Banks to Hijack Victim Accounts – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are targeting hundreds of banking customers in Latin America with a new variant of an...
Hikvision Intercoms Allow Snooping on Neighbors – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading A concerning Internet of Things cyberattack vector has been uncovered — one that can turn the neighboring...