Source: www.bleepingcomputer.com – Author: Bill Toulas Malicious advertisements are now being injected into Microsoft’s AI-powered Bing Chat responses, promoting fake download sites that distribute malware. Bing...
FBI: Dual ransomware attack victims now get hit within 48 hours – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The FBI has warned about a new trend in ransomware attacks where multiple strains are deployed on victims’ networks to encrypt...
Cisco urges admins to fix IOS software zero-day exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Cisco warned customers on Wednesday to patch a zero-day IOS and IOS XE software vulnerability targeted by attackers in the...
Cisco Catalyst SD-WAN Manager flaw allows remote server access – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Cisco is warning of five new Catalyst SD-WAN Manager products vulnerabilities with the most critical allowing unauthenticated remote access to...
Security researcher stopped at US border for investigating crypto scam – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Security researcher Sam Curry describes a stressful situation he encountered upon his return to the U.S. when border officials and...
Budworm hackers target telcos and govt orgs with custom malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A Chinese cyber-espionage hacking group tracked as Budworm has been observed targeting a telecommunication firm in the Middle East and...
How To Implement Zero Trust: Best Practices and Guidelines – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Franklin Okeke on September 28, 2023, 12:23 PM EDT How To Implement Zero Trust: Best Practices and Guidelines Implement a Zero Trust...
NordVPN Review (2023): Pricing, Security & Performance – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares NordVPN Fast facts Our rating: 4.7 stars out of of 5 Pricing: Starts at $5.79 per month Key features Offers...
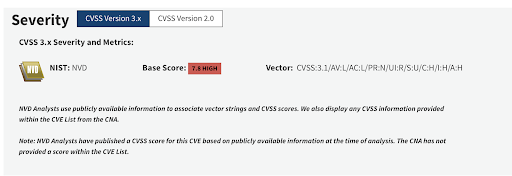
What You Need to Know About the libwebp Exploit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Yael Citro libwebp exploit timeline CVE-2023-41064; CVE-2023-4863; CVE-2023-5129 On September 7th 2023, researchers at Citizen Lab reported a zero-click exploit that was...
Why Ordr? Why Now? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wes Wright I just joined Ordr as Chief Healthcare Officer and, as is often the case in life, there’s a story, personal...
Crocs enhances customer journey and safeguards revenue growth with Kasada – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kasada Customer background Crocs is one of the world’s top non-athletic footwear brands. With over 100 million pairs of shoes sold per...
Threat Spotlight: The Dark Web and AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Flare Executive Overview More than 200,000 credentials to AI language models are currently being sold on the dark web as part of...
Lawsuit Filed Against Google, Meta, H&R Block for Sharing Taxpayer Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Meta, Google, and giant tax preparer H&R Block are being accused of conspiring to illegally use spyware from the tech...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Red Alert – Europe Israel Cyber Security Summit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-red-alert-europe-israel-cyber-security-summit/ Category & Tags: CISO Suite,Governance, Risk &...
Sidecar Containers in Kubernetes: A Personal Journey – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthias Bertschy I had always wanted to use sidecars with Istio or Splunk forwarder in production, but as a Kubernetes maintainer, I...
Unlocking Endpoint Security as a Service: 2023 Insights! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction In the evolving landscape of cyber threats, small businesses find themselves in the crosshairs, necessitating robust and dynamic security...
The Ultimate Guide to Enterprise Risk Management Strategy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kayne McGladrey Enterprise risk management doesn’t have to be scary. Enterprise risk management is a nebulous, hard-to-define topic area. It encompasses a...
Third-Party Risk Management: Best Practices for Protecting Your Business – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kayne McGladrey At this time, nearly every business outsources some aspect of its operations. But it’s becoming increasingly tricky for organizations to...
Chrome Patches 0-Day Exploited by Commercial Spyware Vendor – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management Limited Details Disclosed but Google said it is a Heap-based Buffer Overflow Bug Mihir...
Study Reveals Conti Affiliates Money Laundering Practices – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Ransomware Affiliates Relied on Less Complex, Trackable Methods, It Says Anviksha More (AnvikshaMore)...
Infusion Firm Faces Lawsuit After Hackers Hit Parent Company – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Governance & Risk Management Proposed Class Action Claim Against Amerita Linked to Larger PharMerica...
Nord Security Raises $100M on $3B Valuation to Go After M&A – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Security Operations , Web Application Firewalls (WAF) VPN Service Behemoth Doubles Valuation In Just 17 Months Despite Economic Headwinds Michael Novinson...
Government Shutdown Poised to Stress Nation’s Cybersecurity Supply Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading The looming US federal government shutdown will put the nation’s cybersecurity apparatus under intense strain, increasing the...
Chrome Flags Third Zero-Day This Month That’s Tied to Spying Exploits – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Google has fixed a zero-day vulnerability in its Chrome browser that a commercial vendor has already...
New Cisco IOS Zero-Day Delivers a Double Punch – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A vulnerability affecting Cisco operating systems could enable attackers to take full control of affected devices,...
Johnson Controls International Disrupted by Major Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Johnson Controls International (JCI) this week reported in a filing with the US Securities and Exchange Commission...
Q&A: UK Ambassador on Creating New Cybersecurity Agencies Around the World – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Juliette Wilcox, cybersecurity ambassador for the UK’s Department for International Trade. The UK’s National Cybersecurity Centre...
Novel ZenRAT Scurries Onto Systems via Fake Password Manager Tool – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A novel info-stealing malware variant is lurking behind fake installation packages of the open source password manager...
4 Legal Surprises You May Encounter After a Cybersecurity Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Beth Burgin Waller, Chair, Cybersecurity & Data Privacy Practice, Woods Rogers Vandeventer Black Most security professionals know the parade of problems that...
Supply Chain Attackers Escalate With GitHub Dependabot Impersonation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading In the latest attack to target software supply chains, attackers managed to slip in malicious code...