Source: www.darkreading.com – Author: Curtis Franklin, Senior Analyst, Omdia In the run-up to the 1992 US presidential election, Bill Clinton’s campaign famously had a large sign...
Attacks on Azerbaijan Businesses Drop Malware via Fake Image Files – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading A spear-phishing email posing as a memo from the president of an Azerbaijan company hid malware...
QR Code 101: What the Threats Look Like – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading As QR codes have become ubiquitous, their proliferation has given rise to new and emerging security...
7 Ways SMBs Can Secure Their WordPress Sites – Source: www.darkreading.com
Source: www.darkreading.com – Author: Suhaib Zaheer, Senior VP & General Manager, Cloudways Enterprises large and small rely on WordPress: At least 43% of websites on the...
How the Okta Cross-Tenant Impersonation Attacks Succeeded – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nigel Douglas, Senior Technical Manager, Detection & Response, Sysdig A series of highly sophisticated attacks have sparked significant concerns among organizations that...
Chrome Patches 0-Day Exploited by Commercial Spyware Vendor – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management Limited Details Disclosed but Google said it is a Heap-based Buffer Overflow Bug Mihir...
Zero Trust, Auditability and Identity Governance – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Two years after President Biden’s landmark cybersecurity Executive Order, the question remains: How are federal agencies adapting to the new focus...
Study Reveals Conti Affiliates Money Laundering Practices – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Ransomware Affiliates Relied on Less Complex, Trackable Methods, It Says Akshaya Asokan (asokan_akshaya)...
Infusion Firm Faces Lawsuit After Hackers Hit Parent Company – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Governance & Risk Management Proposed Class Action Claim Against Amerita Linked to Larger PharMerica...
Nord Security Raises $100M on $3B Valuation to Go After M&A – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Security Operations , Web Application Firewalls (WAF) VPN Service Behemoth Doubles Valuation In Just 17 Months Despite Economic Headwinds Michael Novinson...
Cloudflare Users Exposed to Attacks Launched From Within Cloudflare: Researchers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Gaps in Cloudflare’s security controls allow users to bypass customer-configured protection mechanisms and target other users from the platform itself,...
A Key US Government Surveillance Tool Should Face New Limits, a Divided Privacy Oversight Board Says – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Federal spy agencies should be required to get court approval before reviewing the communications of U.S. citizens collected through a...
NIST Publishes Final Version of 800-82r3 OT Security Guide – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs NIST announced on Thursday that it has published the final version of its latest guide to operational technology (OT) security. ...
FBI Warns Organizations of Dual Ransomware, Wiper Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The FBI is warning organizations of new trends in ransomware attacks, where victims are targeted by multiple file-encrypting malware families...
Johnson Controls Hit by Ransomware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Building technology giant Johnson Controls has confirmed being hit by a disruptive cyberattack that appears to have been carried out...
US State Department Says 60,000 Emails Taken in Alleged Chinese Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: AFP The US State Department said Thursday that hackers took around 60,000 emails, although none of them classified, in an attack which...
Progress Software Patches Critical Pre-Auth Flaws in WS_FTP Server Product – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Enterprise technology vendor Progress Software on Thursday shipped patches for critical-level security flaws in its WS_FTP file transfer software, warning...
Verisoul Raises $3.25 Million in Seed Funding to Detect Fake Users – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Verisoul, an Austin, Texas-based company that has developed a SaaS platform for detecting and blocking fake users, announced on Thursday...
Lumu Raises $30 Million for Threat Detection and Response Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Lumu, a cybersecurity firm that helps organizations identify and isolate potential compromises, on Wednesday announced that it has raised $30...
Government Shutdown Could Bench 80% of CISA Staff – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Roughly 80% of the staff at US cybersecurity agency CISA may be sent home at the end of the week...
12 Benefits of Zero Trust for Mid-Sized Businesses – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Antonia Din Zero Trust security is evolving from “nice to have” to an absolute must for organizations everywhere. Fortunately, Zero Trust offers...
Ransomware group demands $51 million from Johnson Controls after cyber attack – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Johnson Controls, a multinational conglomerate that secures industrial control systems, security equipment, fire safety and air conditioning systems, has been...
Privacy Regulator Orders End to Spreadsheet FOI Responses – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s information commissioner has called for an immediate end to the use of excel spreadsheets to publish Freedom of Information (FOI)...
Microsoft Breach Exposed 60,000 State Department Emails – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A sophisticated Chinese cyber-espionage campaign targeting Microsoft Outlook accounts gave Beijing access to tens of thousands of private US government emails,...
MOVEit Developer Patches Critical File Transfer Bugs – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Progress Software has urged customers to patch a critical new vulnerability in one of its flagship file transfer software products, which...
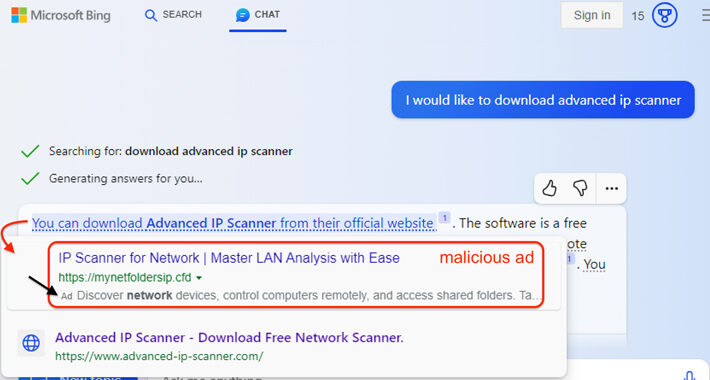
Microsoft’s AI-Powered Bing Chat Ads May Lead Users to Malware-Distributing Sites – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNArtificial Intelligence / Malware Malicious ads served inside Microsoft Bing’s artificial intelligence (AI) chatbot are being used to distribute...
Progress Software Releases Urgent Hotfixes for Multiple Security Flaws in WS_FTP Server – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNServer Security / Vulnerability Progress Software has released hotfixes for a critical security vulnerability, alongside seven other flaws, in...
Cisco Warns of Vulnerability in IOS and IOS XE Software After Exploitation Attempts – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNVulnerability / Network Security Cisco is warning of attempted exploitation of a security flaw in its IOS Software and...
Progress warns of maximum severity WS_FTP Server vulnerability – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Progress Software, the maker of the MOVEit Transfer file-sharing platform recently exploited in widespread data theft attacks, warned customers to...
Microsoft breach led to theft of 60,000 US State Dept emails – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Chinese hackers stole tens of thousands of emails from U.S. State Department accounts after breaching Microsoft’s cloud-based Exchange email platform...