Source: www.bleepingcomputer.com – Author: Bill Toulas Many Discord users attempting to access the popular instant messaging and VoIP social platform today have been met with a...
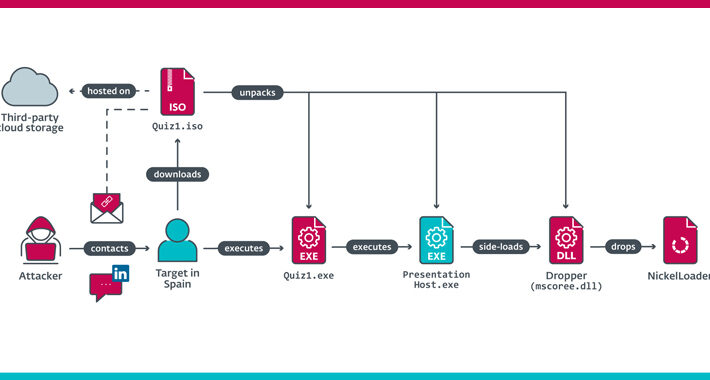
Lazarus hackers breach aerospace firm with new LightlessCan malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The North Korean ‘Lazarus’ hacking group targeted employees of an aerospace company located in Spain with fake job opportunities to...
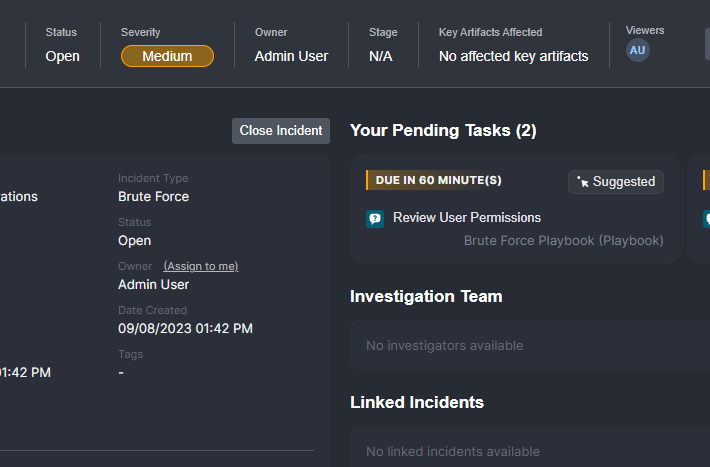
What Enterprise Security Teams Expect from Case Management Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Pierre Noujeim A less-talked about challenge in cybersecurity is managing multiple alert queues. While the volume of alerts is acknowledged as an...
ROUNDTABLE: CISA’s prominent role sharing threat intel could get choked off this weekend – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido Once again, politicians are playing political football, threatening a fourth partial government shutdown in a decade. Related:...
Meraki Chooses Ordr as Ecosystem Partner of the Month! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Julie Criscenti Heck We’ve always known the value of partnering with Cisco Meraki. Recently we learned that we were selected by the...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Transportation Cybersecurity Summit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-transportation-cybersecurity-summit/ Category & Tags: CISO Suite,Governance, Risk &...
CISA Rolls Out a HBOM Framework to Secure Hardware Components – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The federal government for the past few years has focused on protecting the software supply chain in the wake of...
Is that how it works? Hacking and scamming in popular TV shows – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog Friday, September 29, 2023 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Randall Munroe’s XKCD ‘Book Podcasts’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/randall-munroes-xkcd-book-podcasts/ Category & Tags: Humor,Security Bloggers Network,Randall Munroe,Sarcasm,satire,XKCD...
Age Is More Than a Number: Age Verification and Regulatory Compliance for Your Business – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sarah Hunter-Lascoskie In a non-digital world, checking someone’s age has its challenges. People can do a poor job of validating a high-quality...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Academic Perspectives on Cybersecurity Challenges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-academic-perspectives-on-cybersecurity-challenges/ Category & Tags: CISO Suite,Governance, Risk &...
Vulns Found In Another Progress Software File Transfer App – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management ‘There’s a 10-out-10 severity bug you need to patch right now!’ Prajeet Nair (@prajeetspeaks)...
Inside Look: FDA’s Cyber Review Process for Medical Devices – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Hardware / Chip-level Security , Healthcare Jessica Wilkerson of the FDA Details Agency’s ‘Refuse to Accept’ Policy and...
CrowdStrike Boosts Israeli Startup Ties With AWS Partnership – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Next-Generation Technologies & Secure Development AWS & CrowdStrike Cybersecurity Startup Accelerator Will Incubate Early-Stage Firms Michael Novinson (MichaelNovinson) • September 29,...
Editors’ Panel: What Impact Will Cisco’s Splunk Acquisition Have on Industry? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Operational Technology (OT) , Security Information & Event Management (SIEM) Also: OT Security Trends, Challenges; FDA...
NSA Stands Up New Organization to Harness AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development A US Advantage on AI Should ‘Not Be Taken For...
ROUNDTABLE: CISA’s prominent role sharing threat intel could get choked off this weekend – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido Once again, politicians are playing political football, threatening a fourth partial government shutdown in a decade. Related:...
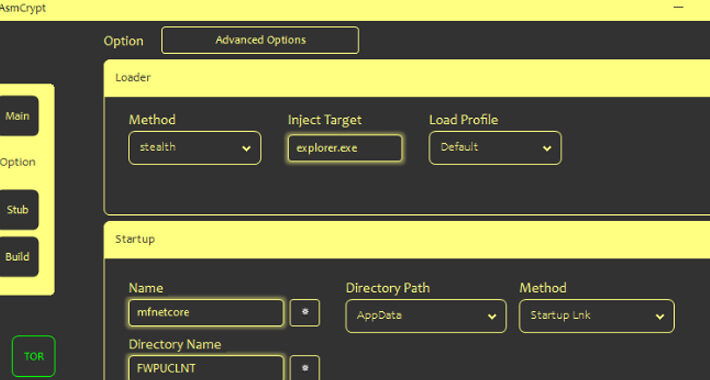
Cybercriminals Using New ASMCrypt Malware Loader Flying Under the Radar – Source:thehackernews.com
Source: thehackernews.com – Author: . Threat actors are selling a new crypter and loader called ASMCrypt, which has been described as an “evolved version” of another...
Lazarus Group Impersonates Recruiter from Meta to Target Spanish Aerospace Firm – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023THNCyber Espionage / Malware The North Korea-linked Lazarus Group has been linked to a cyber espionage attack targeting an...
Post-Quantum Cryptography: Finally Real in Consumer Apps? – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 29, 2023The Hacker NewsQuantum Computing / Network Security Most people are barely thinking about basic cybersecurity, let alone post-quantum cryptography....
Russian Company Offers $20m For Non-NATO Mobile Exploits – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Russian firm Operation Zero has announced a staggering $20m reward for hacking tools capable of compromising iPhones and Android devices. ...
Microsoft’s Bing AI Faces Malware Threat From Deceptive Ads – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft’s Bing Chat has come under scrutiny due to a significant security concern – the infiltration of malicious ads. Malwarebytes researchers...
Phishing, Smishing Surge Targets US Postal Service – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Recent weeks have witnessed a significant increase in cyber-attacks targeting the US Postal Service (USPS), mainly through phishing and smishing campaigns. ...
Chinese threat actors stole around 60,000 emails from US State Department in Microsoft breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Chinese threat actors stole around 60,000 emails from US State Department in Microsoft breach Pierluigi Paganini September 29, 2023 China-linked...
Misconfigured WBSC server leaks thousands of passports – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Misconfigured WBSC server leaks thousands of passports Pierluigi Paganini September 29, 2023 The World Baseball Softball Confederation (WBSC) left open...
CISA adds JBoss RichFaces Framework flaw to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA adds JBoss RichFaces Framework flaw to its Known Exploited Vulnerabilities catalog Pierluigi Paganini September 29, 2023 US CISA added...
Spyware Vendor Targets Egyptian Orgs With Rare iOS Exploit Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading An Israeli surveillanceware company used the three Apple zero-day vulnerabilities disclosed last week to develop an...
DHS Calls Into Question Physical Security in Johnson Controls Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In the latest development of the cyberattack impacting Johnson Controls International (JIC), officials at the Department of...
Cybersecurity Gaps Plague US State Department, GAO Report Warns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading The US Department of State must fully implement its cybersecurity risk program and take additional steps...
Move Over, MOVEit: Critical Progress Bug Infests WS_FTP Software – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading For the second time in recent months, Progress Software is requiring enterprise security teams to drop...