The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Global Cybersecurity Outlook 2023 Insight Report by WEF – World Economic Forum in collaboration with Accenture
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Digital Forensics and Incident Response (DFIR) Framework for Operational Technology (OT) by NIST – Eran Salfati and Michael Pease
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Internet Crime Report 2022 by FBI Internet Crime Compliance Center
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBERSECURITY The Ultimate Hiring Guide by Stanton house
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Salary for US market and Recruiting Trends Guide 2023 by Stanton House
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The 2023 Crypto Crime Report by Chainalysis – Everithing you need to know about cryptocurrency-based crime
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The RED REPORT 2023 – The Top 10 Most Prevalent MITRE ATT&ACK Techniques Used by Adversaries by PICUS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Cyber Defense Index 2022-23 – A benchmark of the digital security preparedness of enterprises across the threat landscapes of the worlds top economies by MIT Technology Review Insights.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
MANDIANT APT1 – Exposing One of Chinas Cyber Espionage Units
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Data Loss Prevention from on-premises to cloud by Microsoft Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Windows Ransomware Detection and Protection – Securing Windows endpoints , the cloud and infrastructure using Microsoft Intune, Sentinel SIEM and Defender by Marius Sandbu – packt.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Artificial Intelligence Risk Management Framework – AI RMF 1.0 By NIST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Malware Analysis Techniques – Tricks for the triage of adversarial software by Dylan Barker – Packt
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Hacking iOS Applications – A detailed testing guide by Dinesh Shetty – Security Innovation
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
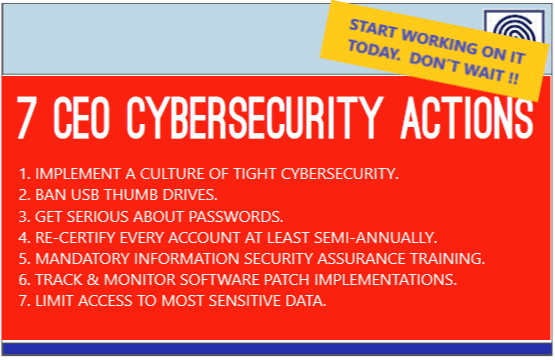
7 CEO CYBERSECURITY ACTIONS – START WORKING ON IT TODAY , DON´T WAIT !!!
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ninjio´s Cyber Hygiene Checklist – Level Up Your Cybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
API Security Fundamentals – Your Handy Guide to Building an Unhackable System by practical-devsecops.com
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Red Team Guides 2023 by HADESS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
10 Cyber Security Myths You Need To Stop Believing by HACKER COMBAT COMMUNITY
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THE ARMY RED TEAM HANDBOOK – The Guide to Making Better Decisions version 9 by – University of Foreign Military and Cultural Studies (UFMCS).
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OWASP API Security Top 10 – The Ten Most Critical API Security Risks by creative commons
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Better Cybersecurity Metrics – SOC Metrics – Threat Hunting Metrics – Cyber Threat Intelligence (CTI) Metrics – Incident Response (IR) Metrics for CISOs by SCYTHE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Making a Business Case for Security – An Interagency Security Committee Best Practice by CISA 2023 Edition
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SANS Faculty Cybersecurity Free Tools – SANS Instructors have built more than 150 open source tools that support your work and help you implement better security.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Artificial intelligence was never a bad think – A self fulfilling Prophesy (My personal vision).
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Guidance for Critical Areas of Focus in Cloud Computing v4.0 by CSA Cloud Security Alliance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Blue Team Strategies – Uncover the secrets of blue teams to combat cyber threats your organization
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TOR AND THE DARKNET – Remain Anonymous and Evade NSA Spying by James Smith
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ChatGTP – The impact of Large Language Models on Law Enforcement by EUROPOL
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...