The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THE TREATH REPORT SUMMER 2022 by Trelix
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Anomaly Detection in Cybersecurity for Dummies by Ram Vaidyanathan
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blue Team Cheat Sheets by Chris Davis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Civil-Military Cooperation and International Collaboration in CYBER OPERATIONS by UNG.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DDoS Attack Threat Landscape trend from Q2 2022 by CLOUDFLARE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 Thales Data Threat Report Critical Infrastructure Edition – Security threats to critical infrastructure.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Common TTPs of modern ransomware groups by Kaspersky Crimeware
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Financial Cybersecurity Risk Management by Paul Rohmeyer & Jennifer Bayuk- Springer – APRESS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
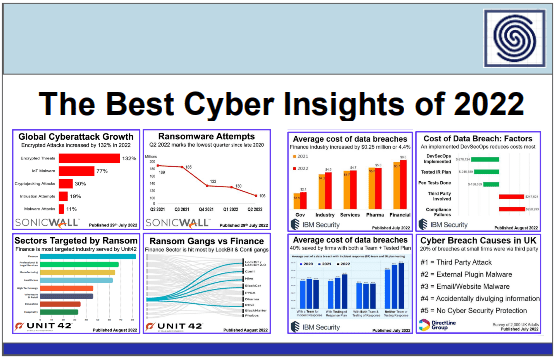
The Best Cyber Insights of 2022 by The Cyber Rescue Alliance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Professional Red Teaming – Conducting Successful Cybersecurity Engagements by Jacob G Oakley – Apress
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Phyton for Red Teams & Hackers by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Open Source Forensic Tools by eForensics Magazine
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Anatomy of an Industrial espionage operation by Bitdefender
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Guide to Cyber Threat Modelling by CSA Singapure
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Talent Crisis Today and Tomorrow by Codrut Andrei
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Incident Response Plan – Guidance and Template by Australian Cyber Security Centre
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Microsoft Azure Resiliency – Business Continuity and Disaster Recovery
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Protecting critical Infrastructure against cyber threats – An analysis of relevant regulation, good practices, international law and norms.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Guide for Multi-Cloud Read Team AWS – GCP – AZURE by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
History of Supply Chain Attacks in the News by SentinelOne
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware in a Global Context Report 2021 by Virustotal
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
40 Methods for Privilege Escalation P1 by Hadess
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Chemical Sector Cybersecurity – Framework Implementation Guidance by CISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Checkpoint Cyber Attack Trend 2022 Mid Year Report by Check Point Research
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of ICS Security in the Age of Cloud by CSA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BOMA Canada 2022 Cyber Incidents Response Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CROWDSTRIKE 2022 Global Threat Report by George Kurtz
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Allianz 2022 Risk Barometer – The most important business risks for the next 12 months and beyond, based on the insight of 2,650 risk management experts from 89 countries and territories.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
COBIT ISACA 5 – A Business Framework for the Governance and Management of Enterprise IT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...