The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations Center Guidebook – A Practical Guide for a Successful SOC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ENISA THREAT LANDSCAPE FOR RANSOMWARE ATTACK REPORT JULY 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Kubernetes Security Report 2022 by RedHat
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Advancing Supply Chain Security in Oil and Gas an Industry Analysis by World Economic Forum
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TELECOM SECURITY INCIDENTS REPORT 2021 BY ENISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NSA’S Top Ten Cybersecurity Mitigation Strategies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cloud Security Technical Reference Architecture
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NSA Network Infrastructure Security Guidance V1.0 March 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybercrime Investigators Handbook by WILEY
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How Much 10 Companies Paid Their Virtual CISO Service in 2022 Benchmark by Nathaniel Cole
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Undestanding Networks Hacks – Attack and Defense with Python 2nd Edition by Bastian Ballman – Springer
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
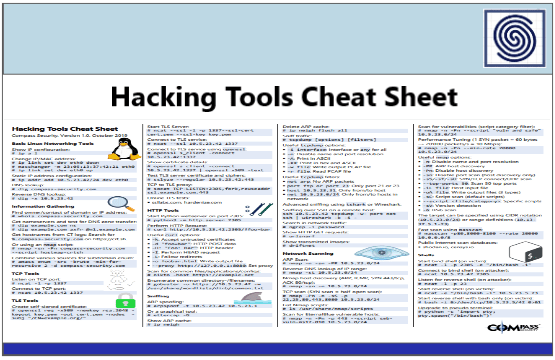
Hacking Tools Cheat Sheet by Compass Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Using MITRE ATT&CK IN THREAT HUNTING AND DETECTION BY LogRhythm
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
List Of Top Penetration Testing Tools by Hacker Combat.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
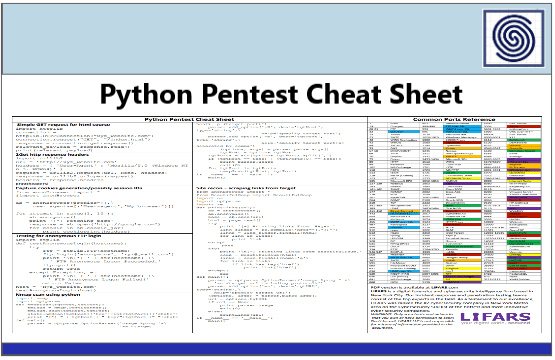
Phyton Pentest Cheat Sheet by LIFARS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Microsoft Zero Trust Maturity Model
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Microsoft 365 and the NIST Cybersecurity Framework
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Hunting Introduction by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The “Sand Clock” Model of Cybersecurity by Javier Stransky
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Evolution of Cyber Hunt Processes From IOCs to TTPs by HHS OIS Organization
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SIEM FOR BEGINNERS PREPARED FOR SOC TEAMS BY LETSDEFEND
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A SANS 2021 Survey for Security Operations Centers (SOCs)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Jump-start Your SOC Analyst Career – A Roadmap to Cybersecurity Success by Apress
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
45 SIEM Use Cases for Security Monitoring by Paladion Cyber Defense.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
6 Cloud Security Basics that every CISO, CIO AND CTO should know by InstaSafe.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Linux Basics for Hackers by Occupytheweb
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
RED TEAMING 101 Security Posture Assesment with Hackers-Eye View
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISA 5G Security Evaluation Process Investigation v1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO Responsibilities by Hacker Combat Community – The Changing Role of the CISO
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...