The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cloud Security Alliance – Zero Trust Guiding Principles PD
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISSP Study GuideCERTIFICATION TRAINING
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
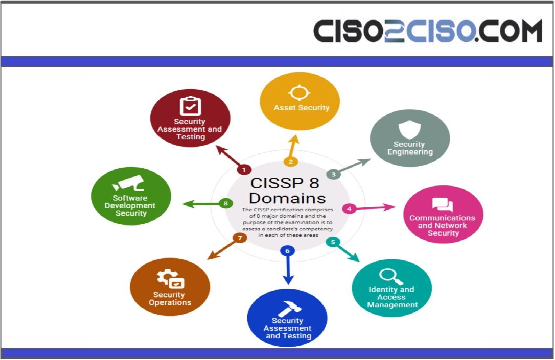
CISSPP 8 Domains
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO PLAYBOOK:F I R S T1 0 0D A Y SSetting the CISO up for success
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CIS Controls Cost of Cyber Defense
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISA Open Source SoftwareSecurity Roadmap
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
North Korea’s BlueNoroff APT Debuts ‘Dumbed Down’ macOS Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading North Korean state hackers have debuted a fresh Mac malware targeting users in the US and...
Programming, Self-Learning Crucial for Autonomous Operations – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Governance & Risk Management , Internet of Things Security Success Hinges on Marrying Programmed Task and Information From...
CONTINUOUS DIAGNOSTICS AND MITIGATION PROGRAM – Identity, Credential, and Access Management (ICAM) Reference Architecture
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Bug Bounty Funshop
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Bloodhound Active Directory Enumeration Tool
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blockchain Security A Framework for Trust and Adoption
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Best Cybersecurity Certifications online
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Azure DevOps Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Cyber Breach Delays Poll Worker Training in Mississippi’s Largest County Before the Statewide Vote – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Election officials in Mississippi’s most populous county had to scramble to complete required poll worker training after an early September...
Awesome Bugbounty Writeups
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Awesome SOC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Awesome Azure Penetration Testing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Defending Azure Active Directory
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
WEEKLYCYBER SECURITY BRIEFING
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Application Container Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Supply Chain Startup Chainguard Scores $61 Million Series B – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Chainguard, a high-flying security startup founded by a team of former Google software engineers, has banked $61 million in new...
API Security Checklist
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
API Security: Threats, Best Practices,Challenges, and Way forward usingAI
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Antes, durantey después de ira la NubeRespuesta ante Incidentes
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware Hostage Rescue Manual
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Anonymous Logins for Pentesters
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
An Introduction to Information Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ISO/IEC 27701Privacy Information Management – Your implementation guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...