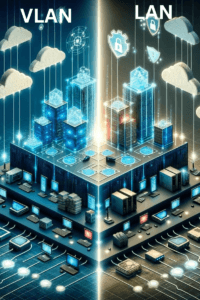
Source: securityboulevard.com – Author: Michael Toback Understanding the Basic Concept of VLANs Virtual Local Area Networks, or VLANs, serve as a critical computing technology designed for...
Why a Zero Trust Security Policy Matters and Steps to Implementation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michelle Ofir Geveye Understanding Zero Trust Traditionally, cybersecurity operated on a simple principle: trust what’s inside, be wary of what’s outside. This...
Yahoo “Strongly” Recommends DMARC RUA Tag for Bulk Senders – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra Developers at Yahoo have been busy formulating guidelines for bulk senders and the DMARC RUA tag has been mentioned as...
Ubuntu Security Updates Fixed Vim Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina Vim, a powerful and widely used text editor, has recently come under scrutiny due to several vulnerabilities that could potentially...
The Intersection of IoT and Financial Security: Expert Tips for Protection – Source: securityboulevard.com
Source: securityboulevard.com – Author: TuxCare Team Sophisticated Internet of Things (IoT) technologies transformed the cybersecurity systems in financial services. They’re continuously evolving and improving. Take credit...
Merry Little Christmas – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
GambleForce Attacks: APAC Firms Targeted With SQL Injections – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wajahat Raja In light of recent GambleForce attacks, a new threat actor has emerged, targeting more than 20 organizations across the Asia-Pacific...
The Year in Review and 2024 Predictions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston In our last episode of the year, we replay our predictions for 2023 reviewing what we got right and what...
Learn Cybersecurity Skills From Scratch for Just $30 Through January 1 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Good things are coming your way! In order for us to complete site maintenance, TechRepublic is read-only from December 22...
Domain Name Security Challenges – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Protecting domain name systems finally has the attention of cybersecurity professionals -because every recent large data breach has involved a DNS...
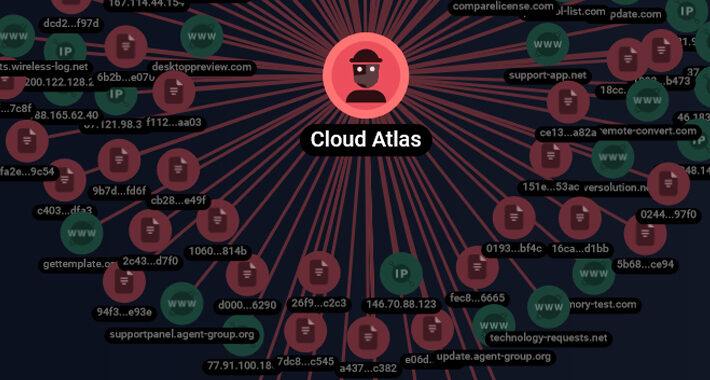
Cloud Atlas’ Spear-Phishing Attacks Target Russian Agro and Research Companies – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 25, 2023NewsroomCyber Espionage / Malware The threat actor referred to as Cloud Atlas has been linked to a set of...
Security Affairs newsletter Round 451 by Pierluigi Paganini – INTERNATIONAL EDITION – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Security Affairs newsletter Round 451 by Pierluigi Paganini – INTERNATIONAL EDITION | Europol and ENISA spotted 443 e-stores compromised with...
Europol and ENISA spotted 443 e-stores compromised with digital skimming – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Europol and ENISA spotted 443 e-stores compromised with digital skimming Pierluigi Paganini December 24, 2023 A joint law enforcement operation...
Video game giant Ubisoft investigates reports of a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Video game giant Ubisoft investigates reports of a data breach Pierluigi Paganini December 24, 2023 Video game publisher Ubisoft is...
Weekly Update 379 – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt It’s that time of the year again, time to head from the heat to the cold as we jump on...
USENIX Security ’23 – ‘Sneaky Spy Devices And Defective Detectors: The Ecosystem Of Intimate Partner Surveillance With Covert Devices’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Full Presenters List: Rose Ceccio, Sophie Stephenson, Varun Chadha, Danny Yuxing Huang, Rahul Chatterjee Many thanks to USENIX for publishing...
Democracy 2024: Pro-Hunger ≠ “Pro-Life” – Source: securityboulevard.com
Source: securityboulevard.com – Author: hrbrmstr Ref AP News: https://apnews.com/article/iowa-summer-ebt-food-assistance-0e878c5c0fc9dd0dd55622cb22a82561. Iowa has decided not to participate in the 2024 Summer Electronic Benefits Transfer for Children (Summer EBT)...
British LAPSUS$ Teen Members Sentenced for High-Profile Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 24, 2023NewsroomCyber Crime / Data Breach Two British teens part of the LAPSUS$ cyber crime and extortion gang have been...
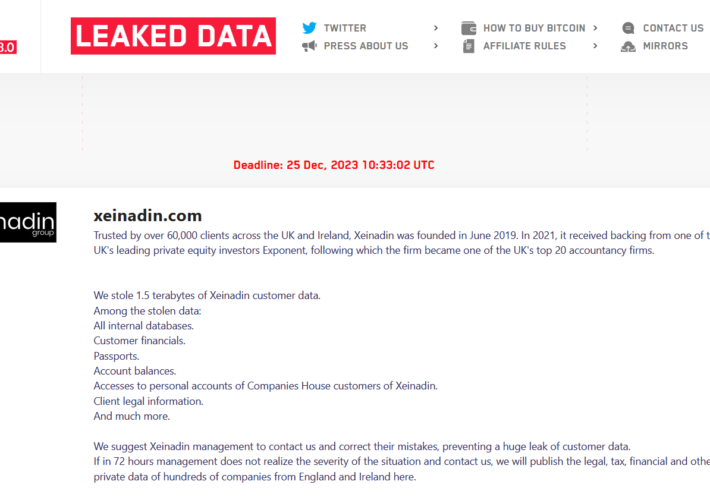
LockBit ransomware gang claims to have breached accountancy firm Xeinadin – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini LockBit ransomware gang claims to have breached accountancy firm Xeinadin Pierluigi Paganini December 23, 2023 The LockBit ransomware claims to...
Mobile virtual network operator Mint Mobile discloses a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Mobile virtual network operator Mint Mobile discloses a data breach Pierluigi Paganini December 23, 2023 Mobile virtual network operator Mint...
Group Therapy – security and privacy in Facebook groups – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Harley Having found myself roped into assisting as co-administrator a couple of Facebook groups with security/privacy issues, I thought I should,...
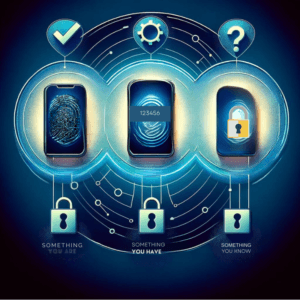
Best Practices in Multi-Factor Authentication for Enhanced Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Imagine standing at the entrance to a vault where your most valuable possessions are stored. The door doesn’t open with...
USENIX Security ’23 – ‘“It’s The Equivalent of Feeling Like You’re In Jail”: Lessons From Firsthand & Secondhand Accounts Of IoT-Enabled Intimate Partner Abuse’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Full Presenter List: Sophie Stephenson, Majed Almansoori, Pardis Emami-Naeini, Rahul Chatterjee Many thanks to USENIX for publishing their outstanding USENIX...
Impact of Apache Struts2 Code Execution Vulnerability – Source: securityboulevard.com
Source: securityboulevard.com – Author: Riddika Grover Recent attacks have demonstrated a significant growth in Zero Days and Remote Code Execution. Kratikal has observed that threat actors...
Kansas City Hospital Ransomware Attack Consequences – Source: securityboulevard.com
Source: securityboulevard.com – Author: Axio Cloud Security, Governance and Skills in 2024 Step 1 of 6 16% Who in your organization is responsible for cloud security?...
Establish Security Outcomes With Data Discovery and Classification – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cavelo Blog And the real-life challenges midsized enterprises are juggling as they scale to achieve them The practice of data discovery and...
Friday Squid Blogging: Squid Parts into Fertilizer – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments &ers • December 22, 2023 5:30 PM @ALL Common sense won. hxxps://news.err.ee/1609202272/interior-abandons-plan-to-ban-non-personalized-prepaid-sim-cards How is this at your side?...
‘Wall of Flippers’ detects Flipper Zero Bluetooth spam attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new Python project called ‘Wall of Flippers’ detects Bluetooth spam attacks launched by Flipper Zero and Android devices. By...
Chameleon Android Malware Can Bypass Biometric Security – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A variant of the Chameleon Android banking trojan features new bypass capabilities and has expanded its targeting area. The post...
Ransomware Attackers Abuse Multiple Windows CLFS Driver Zero-Days – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: cryptoFX via Alamy Stock Photo In the last year and a half, attackers have exploited at least...