The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Attack Against Google Cloud Native App
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ARP Spoofing: Protegiendo-se contra interseptaçã de datos sensíveis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Process Ghosting Attack
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Physical Security Performance Goals for Faith-Based Communities
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Argo CD End User Threat Model
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
APT Report 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
PCI DSS v4.x: Targeted Risk Analysis Guidance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OWASP API Security Top 10 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Aproximación a laInteligencia Artificialy la ciberseguridadINFORME DE BUENAS PRÁCTICAS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Anti-Reverse – The “Ultimate”Anti-Debugging Reference
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OSINT Tools for diving deep in to the Dark Web
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Here’s Some Bitcoin: Oh, and You’ve Been Served! – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs A California man who lost $100,000 in a 2021 SIM-swapping attack is suing the unknown holder of a cryptocurrency wallet that...
Annual Payment Fraud Intelligence Report 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Patch Now: Critical Windows Kerberos Bug Bypasses Microsoft Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Soure: Andrii Yalanskyi via Shutterstock Microsoft eased enterprise security teams into 2024 with a relatively light January security...
Ukraine Claims Revenge Hack Against Moscow Internet Provider – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 1 Min Read Source: Imaginechina Limited via Alamy Stock Photo Sources reportedly tipped off Ukraine media to...
Hospitality Hackers Target Hotels’ Booking.com Logins – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Aleksey Zotov via Alamy Stock Photo Cyberattackers are hitting the digital road, looking to...
Path Traversal Bug Besets Popular Kyocera Office Printers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer 3 Min Read Source: Piotr Adamowicz via Alamy Stock Photo A newly published path traversal vulnerability could enable...
Ransomware Gang Gives Toronto Zoo the Monkey Business – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Francesco Puntiroli via Alamy Stock Photo The Toronto Zoo has experienced a ransomware attack that’s driving its admins...
Turkish Cyber Threat Targets MSSQL Servers With Mimic Ransomware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: cryptoFX via Alamy Stock Photo A sophisticated attack campaign codenamed RE#TURGENCE by researchers has been discovered infiltrating...
Delinea Acquires Authomize to Strengthen Extended PAM – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO, Jan. 9, 2024 /PRNewswire/ — Delinea, a leading provider of solutions that seamlessly extend Privileged Access Management (PAM), today announced it...
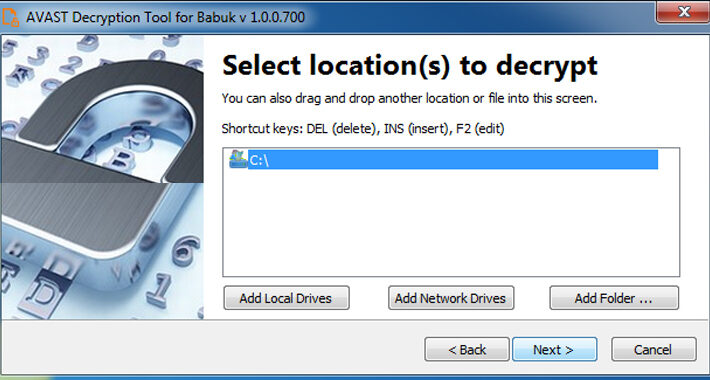
Free Decryptor Released for Black Basta and Babuk’s Tortilla Ransomware Victims – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomRansomware / Data Security A decryptor for the Tortilla variant of the Babuk ransomware has been released by Cisco...
FTC Bans Outlogic (X-Mode) From Selling Sensitive Location Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomPrivacy / Regulatory Compliance The U.S. Federal Trade Commission (FTC) on Tuesday prohibited data broker Outlogic, which was previously...
Microsoft’s January 2024 Windows Update Patches 48 New Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomVulnerability / Windows Security Microsoft has addressed a total of 48 security flaws spanning its software as part of...
CISA Flags 6 Vulnerabilities – Apple, Apache, Adobe , D-Link, Joomla Under Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomPatch Management / Threat Intelligence The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added six security flaws to...
Nigerian gets 10 years for laundering millions stolen from elderly – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Nigerian man Olugbenga Lawal (also known as Razak Aolugbengela) was sentenced on Monday to 10 years and one month in...
US SEC’s X account hacked to announce fake Bitcoin ETF approval – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Addition SEC statement added below. The X account for the U.S. Securities and Exchange Commission was hacked today to issue...
China claims it cracked Apple’s AirDrop to find numbers, email addresses – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams A Chinese state-backed research institute claims to have discovered how to decrypt device logs for Apple’s AirDrop feature, allowing the...
Ransomware victims targeted by fake hack-back offers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Some organizations victimized by the Royal and Akira ransomware gangs have been targeted by a threat actor posing as a...
FTC bans data broker from selling Americans’ location data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Today, the U.S. Federal Trade Commission (FTC) banned data broker Outlogic, formerly X-Mode Social, from selling Americans’ raw location data...