Source: securityboulevard.com – Author: Richi Jennings Chinese citizens using peer-to-peer wireless comms “must be identified.” The Beijing Bureau of Justice claims it can trace senders of...
In the News | How To Measure Cybersecurity ROI for Schools – Source: securityboulevard.com
Source: securityboulevard.com – Author: Katie Fritchen This article was originally published in Hackernoon on 12.13.23 by Charlie Sander, CEO at ManagedMethods. With the surge in cyber...
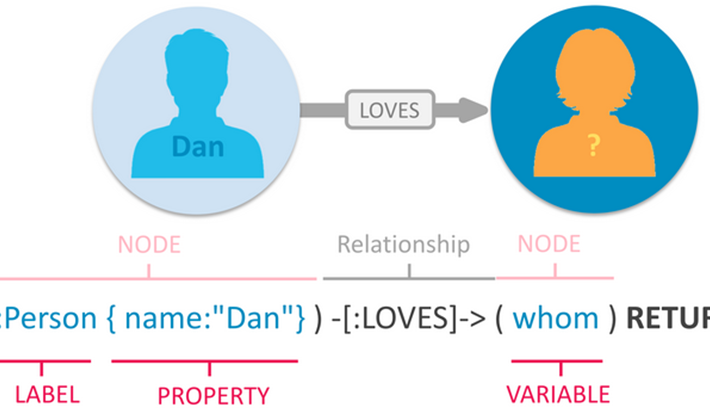
Cypher Queries in BloodHound Enterprise – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan D. BloodHound Enterprise (BHE) recently saw the addition of a new, game-changing feature: open-ended Cypher searches. For those unfamiliar, Cypher is...
EU Enhances Cybersecurity Requirements for Agencies – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , IT Risk Management Cyber Regulation Requires EU Agencies to Assess Risks and Report Incidents Akshaya Asokan...
Cybercriminals Bully Cancer Patients With Swatting Threat – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Ransomware Extortion Demands, Lawsuits Pile Up After Fred Hutchinson Cancer Center Hack Marianne Kolbasuk...
How Our Own Insecurity Fuels Global Threats – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Leadership & Executive Communication Professor John Walker on Need for Organizational Introspection, Global Perspective...
EU Commission Examines OpenAI, Microsoft Relationship – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Commission Says Close Company Connections Make Conditions Ripe for Merger...
Facial Scanning by Burger King in Brazil – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier In 2000, I wrote: “If McDonald’s offered three free Big Macs for a DNA sample, there would be lines around...
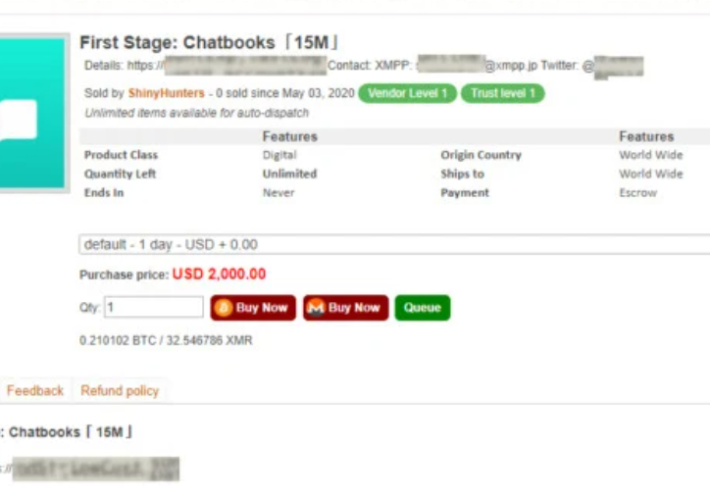
ShinyHunters member sentenced to three years in prison – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini ShinyHunters member sentenced to three years in prison A U.S. District Court sentenced ShinyHunters hacker Sebastien Raoult to three years...
HMG Healthcare disclosed a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini HMG Healthcare disclosed a data breach The Healthcare services provider HMG Healthcare has disclosed a data breach that impacted 40...
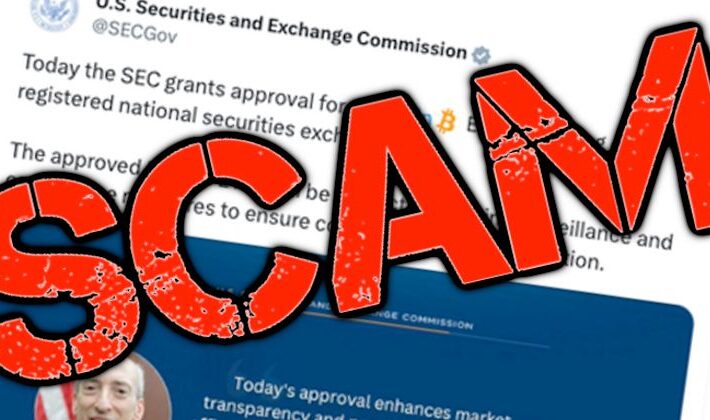
Threat actors hacked the X account of the Securities and Exchange Commission (SEC) and announced fake Bitcoin ETF approval – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors hacked the X account of the Securities and Exchange Commission (SEC) and announced fake Bitcoin ETF approval Threat...
Entire population of Brazil possibly exposed in massive data leak – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Entire population of Brazil possibly exposed in massive data leak The private data of hundreds of millions of Brazilian individuals...
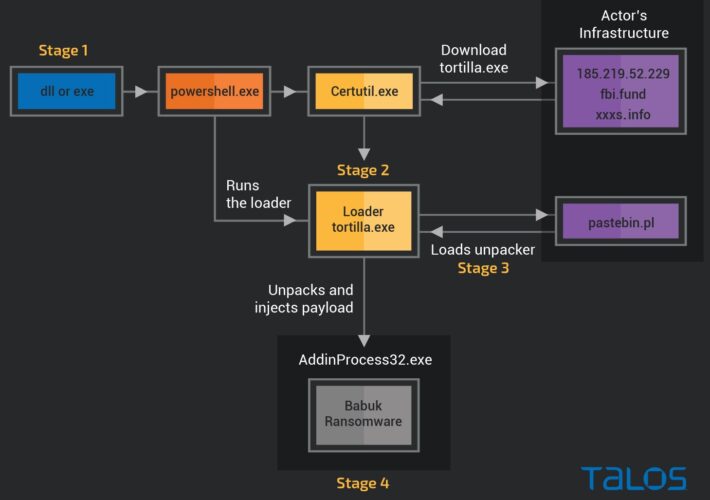
Decryptor for Tortilla variant of Babuk ransomware released – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Decryptor for Tortilla variant of Babuk ransomware released Researchers and the Dutch Police released a decryptor for the Tortilla variant...
SEC’s Twitter account hacked to say Bitcoin ETFs approved. Politicians and lawyers demand investigation into security breach – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley The official Twitter account of the US Securities and Exchange Commission (SEC) was hacked yesterday, with scammers posting an unauthorised...
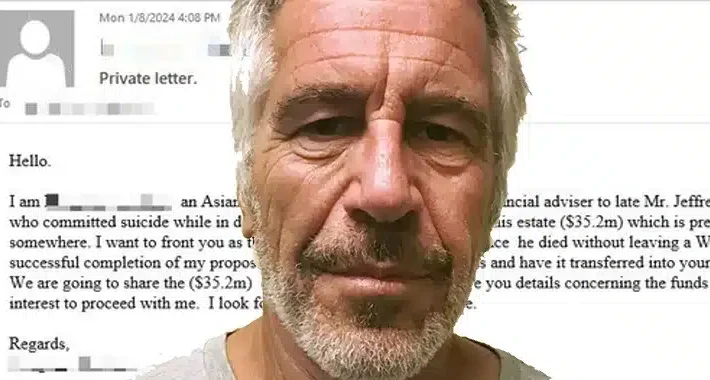
Jeffrey Epstein email scams rear their ugly head – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley The security boffins at Bitdefender have detected what they describe as a “resurgence” in email scams related to notorious sex...
Believing they would be paid a fortune for having sex with women, hundreds of Indian men scammed out of cash – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Geeta Pandey at BBC News reports: In early December Mangesh Kumar (name changed) was scrolling on Facebook when he came...
NoaBot: Latest Mirai-Based Botnet Targeting SSH Servers for Crypto Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 10, 2024NewsroomServer Security / Cryptocurrency A new Mirai-based botnet called NoaBot is being used by threat actors as part of...
Getting off the Attack Surface Hamster Wheel: Identity Can Help – Source:thehackernews.com
Source: thehackernews.com – Author: . IT professionals have developed a sophisticated understanding of the enterprise attack surface – what it is, how to quantify it and...
Volexity Catches Chinese Hackers Exploiting Ivanti VPN Zero-Days – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Ivanti confirms active zero-day exploits, ships pre-patch mitigations, but says comprehensive fixes won’t be available until January 22. The post...
ExtraHop Banks $100M in Growth Funding, Adds New Execs – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News Seattle network detection and response firm secures $100 million in growth funding and adds to its executive team. The post...
HMG Healthcare Says Data Breach Impacts 40 Facilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The compromised information includes names, contact information, dates of birth, health information, medical treatment details, Social Security numbers, and employee...
French Computer Hacker Jailed in US – Source: www.securityweek.com
Source: www.securityweek.com – Author: AFP A computer hacker who was part of a criminal gang that stole data from hundreds of millions of people and sold...
Anecdotes Raises $25 Million for Enterprise GRC Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Anecdotes has raised $25 million in Series B funding, which brings the total investment to $55 million, for its compliance...
Kyocera Device Manager Vulnerability Exposes Enterprise Credentials – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire An improper input validation flaw in Kyocera Device Manager allows attackers to capture credentials, compromise accounts. The post Kyocera Device...
SAP’s First Patches of 2024 Resolve Critical Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire SAP has released patches for critical vulnerabilities in Business Application Studio, Web IDE, and Edge Integration Cell. The post SAP’s...
Dutch Engineer Used Water Pump to Get Billion-Dollar Stuxnet Malware Into Iranian Nuclear Facility: Report – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs An engineer recruited by intelligence services used a water pump to deliver Stuxnet, which reportedly cost $1-2 billion to develop....
China Says State-Backed Experts Crack Apple’s AirDrop – Source: www.securityweek.com
Source: www.securityweek.com – Author: AFP Chinese state-backed experts have found a way to identify people who use Apple’s encrypted AirDrop messaging service, according to the Beijing...
Android’s January 2024 Security Update Patches 58 Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Android’s first security update of 2024 resolves high-severity elevation of privilege and information disclosure vulnerabilities. The post Android’s January 2024...
Best Practices for Implementing a IS Awareness Program
Establishing and maintaining information-security awareness through a security awareness program is vital to an organization’s progress and success. A robust and properly implemented security awareness program...
Azure Penetration Testing Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...