Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft has released the KB5034122 cumulative update for Windows 10 21H2 and Windows 10 22H2, which includes only a small...
CISA warns agencies of fourth flaw used in Triangulation spyware attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The U.S. Cybersecurity and Infrastructure Security Agency has added to its to the Known Exploited Vulnerabilities catalog six vulnerabilities that...
Microsoft January 2024 Patch Tuesday fixes 49 flaws, 12 RCE bugs – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Today is Microsoft’s January 2024 Patch Tuesday, which includes security updates for a total of 49 flaws and 12 remote...
Windows 11 KB5034123 update released with security and Wi-Fi fixes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft has released the Windows 11 KB5034123 cumulative update for versions 23H2 and 22H2 to fix a variety of issues, including...
Hackers target Microsoft SQL servers in Mimic ransomware attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan A group of financially motivated Turkish hackers targets Microsoft SQL (MSSQL) servers worldwide to encrypt the victims’ files with Mimic...
Android Shim Attack Surface
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Anatomy of 100 Cybersecurity Incidents in Industrial Op
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Top 25 Cybersecurity Frameworks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
All About Phishing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
AGI (ARTIFICIAL GENERAL INTELLIGENCE) UNLEASHED: CYBERSECURITY’S NEW FRONTIER
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Hold Account Takeover Attempts at Bay with New Integrated Password Strength Evaluator | Impart Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Impart Security Blog We’re excited to announce our newest Integrated Password Strength Evaluator feature. The Integrated Password Strength Evaluator uses Impart Security’s...
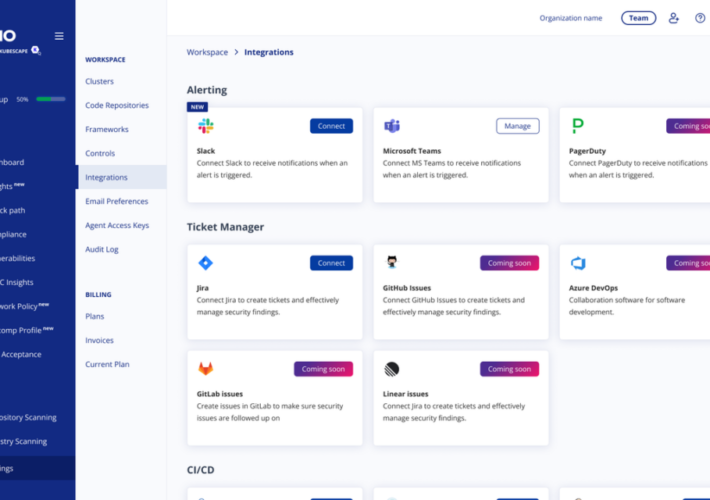
ARMO announces new Slack integration – Source: securityboulevard.com
Source: securityboulevard.com – Author: Yossi Ben Naim We’re thrilled to introduce a fresh ARMO app designed exclusively for Slack, delivering notifications directly to the channels where...
USENIX Security ‘An Input-Agnostic Hierarchical Deep Learning Framework For Traffic Fingerprinting’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Jian Qu, Xiaobo Ma, Jianfeng Li, Xiapu Luo, Lei Xue, Junjie Zhang, Zhenhua Li, Li Feng, Xiaohong Guan Many...
Survey: Election Workers Feel Unprepared for Upcoming Cyberthreats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The issues of outside interference in U.S. elections and the security of the systems behind them have been talked and...
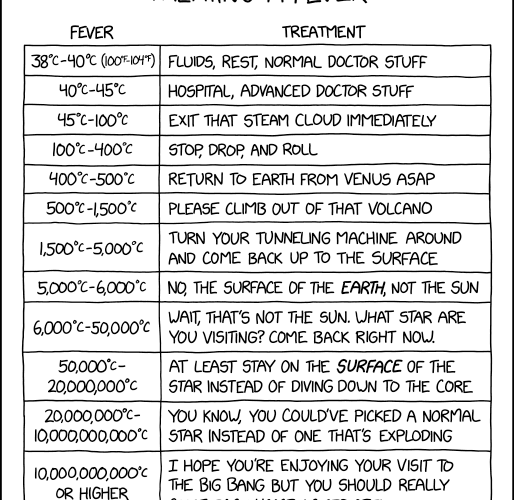
Randall Munroe’s XKCD ‘Fever’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Infographic: A History of Network Device Threats and What Lies Ahead – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland In 2023, the industry experienced a significant uptick in attacks against network devices such as VPNs, firewalls, load balancers, switches,...
2024 Cybersecurity Predictions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kelsey Gast Entering a new year, the cybersecurity landscape is poised for significant shifts, driven by the dynamic interplay between technological advancements...
Zoom joins the vulnerability fray: Will VISS move the needle on AppSec? – Source: securityboulevard.com
Source: securityboulevard.com – Author: John P. Mello Jr. Zoom, best known for its online videoconferencing and collaboration platform, is getting into vulnerability management. The company has...
Infostealers Abuse Google OAuth Endpoint to ‘Revive’ Cookies, Hijack Accounts – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire The exploitation of an undocumented Google OAuth endpoint, MultiLogin, by various information-stealing malware strains has raised significant concerns within the...
TrustCloud Named Security Innovation of the Year (SMB) by the Cloud Awards – Source: securityboulevard.com
Source: securityboulevard.com – Author: Erin Crapser Boston MA—January 9, 2024—TrustCloud, the Trust Assurance platform using AI to upgrade GRC into a profit center, announced today it...
Active Directory Pentest Course
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Detailed Guide on AMSI Bypass
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Türkiye Email Security Landscape Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Authentication Report Enzoic final
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
200 IT Security Job Interview QuestionsThe Questions IT Leaders Ask
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Great Cybersecurity Frameworks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How the definition of digital transformation continues to evolve… – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau From 2003-2004, Aman served as the Chief Technology Officer for AGF Technologies, during which time he also co-founded a company called...
OpenAI: Gen AI ‘Impossible’ Without Copyrighted Material – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Copyright Probes Continue to Trouble AI Developers Akshaya Asokan (asokan_akshaya)...
Live Webinar | Evolution of Legacy Shadow IT: How Does AI Change the Landscape in 2024? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Nate Smolenski Head of Cyber Intelligence Strategy, Netskope Nate Smolenski is an experienced CISO, Advisor, and technology leader with over two...
Live Webinar | Cybersecurity Compliance Essentials for Resource-Constrained State and Local Governments – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Jamie Tomasello Managing Director, Superbloom Jamie Tomasello (she/her and he/him) is a technology and policy leader with a strategic focus on...