Source: securityboulevard.com – Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security » USENIX Security ’23 – Xingman Chen, Yinghao Shi, Zheyu...
API security risks, testing, protection best practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Adam Cheriki, Co-founder & CTO, Entro As per the State of Developer Experience report released in 2023, 98% of developers perceive APIs...
Stopping Alert Fatigue in 3 Simple Steps – Source: securityboulevard.com
Source: securityboulevard.com – Author: Julie Peterson We live in a world filled with constant notifications. From medical devices to severe weather warnings on your phone to...
PixieFail Bugs in UEFI Open Source Implementation Threaten Computers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A collection of security vulnerabilities found within the de facto open source implementation of the UEFI specification could expose systems...
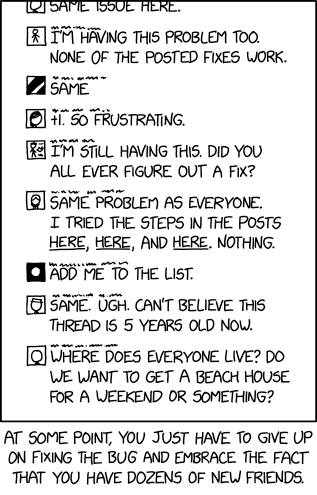
Randall Munroe’s XKCD ‘Bug Thread’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2024/01/randall-munroes-xkcd-bug-thread/ Category & Tags: Humor,Security Bloggers Network,Randall Munroe,Sarcasm,satire,XKCD...
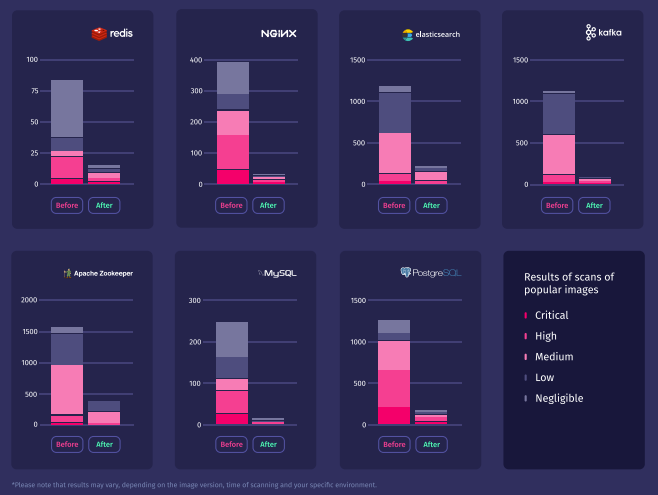
Are you looking for vulnerabilities in the right places? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ben Hirschberg With the rapid pace of technological evolution, ensuring security within the systems we operate and the software we deploy has...
TeamViewer abused to breach networks in new ransomware attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Ransomware actors are again using TeamViewer to gain initial access to organization endpoints and attempt to deploy encryptors based on...
CISA: Critical Ivanti auth bypass bug now actively exploited – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA warns that a critical authentication bypass vulnerability in Ivanti’s Endpoint Manager Mobile (EPMM) and MobileIron Core device management software...
Microsoft tests instant access to Android photos in Windows 11 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft plans to provide Windows 11 users with almost instant access to photos and screenshots they’ve taken on their Android smartphones....
Kansas State University cyberattack disrupts IT network and services – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Kansas State University (K-State) announced it is managing a cybersecurity incident that has disrupted certain network systems, including VPN, K-State...
Haier hits Home Assistant plugin dev with takedown notice – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Appliances giant Haier issued a takedown notice to a software developer for creating Home Assistant integration plugins for the company’s...
US govt wants BreachForums admin sentenced to 15 years in prison – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The United States government has recommended that Conor Brian Fitzpatrick, the creator and lead administrator of the now-defunct BreachForums hacking...
Credentials are Still King: Leaked Credentials, Data Breaches and Dark Web Markets – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Flare Infostealer malware is one of the most substantial and underappreciated risk vectors for corporate information security teams. Infostealers infect...
Google: Russian FSB hackers deploy new Spica backdoor malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google says the ColdRiver Russian-backed hacking group is pushing previously unknown backdoor malware using payloads masquerading as a PDF decryption tool....
Docker hosts hacked in ongoing website traffic theft scheme – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new campaign targeting vulnerable Docker services deploys an XMRig miner and the 9hits viewer app on compromised hosts, allowing...
Jira down: Atlassian outage affecting multiple cloud services – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Multiple Atlassian Jira products are experiencing an ongoing outage as of this morning. Users of Jira Work management, Jira Software,...
Popular GPUs Used AI Systems Vulnerable to Memory Leak Flaw – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development LeftoverLocals Affects Apple, AMD and Qualcomm Devices Akshaya Asokan (asokan_akshaya)...
Swiss Government Reports Nuisance-Level DDoS Disruptions – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Self-Proclaimed Russian Hacktivists Continue Putin-Aligned Information Operations Mathew...
White House Official Warns of AI Risks in 2024 Elections – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific No ‘Magic Solution’ to Prevent Malicious Use of AI in Elections,...
PHMSA Launches Initiatives to Bolster Pipeline Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Agency Tasked With Pipeline Security Takes New Steps to Combat Rise in Cyberattacks Chris Riotta (@chrisriotta) • January 18, 2024 ...
AHA: Rise in Scams Targeting IT Help Desks for Payment Fraud – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific American Hospital Association Warns of Social Engineering Schemes Marianne Kolbasuk McGee (HealthInfoSec)...
New Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024NewsroomServer Security / Cryptocurrency Vulnerable Docker services are being targeted by a novel campaign in which the threat actors...
Russian COLDRIVER Hackers Expand Beyond Phishing with Custom Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . The Russia-linked threat actor known as COLDRIVER has been observed evolving its tradecraft to go beyond credential harvesting to deliver its...
TensorFlow CI/CD Flaw Exposed Supply Chain to Poisoning Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024NewsroomSupply Chain Attacks / AI Security Continuous integration and continuous delivery (CI/CD) misconfigurations discovered in the open-source TensorFlow machine...
MFA Spamming and Fatigue: When Security Measures Go Wrong – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024The Hacker NewsAuthentication Security / Passwords In today’s digital landscape, traditional password-only authentication systems have proven to be vulnerable...
Attackers Could Eavesdrop on AI Conversations on Apple, AMD, Imagination and Qualcomm GPUs – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Researchers at cybersecurity research and consulting firm Trail of Bits have discovered a vulnerability that could allow attackers to read...
Androxgh0st Malware Botnet Steals AWS, Microsoft Credentials and More – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cedric Pernet The Federal Bureau of Investigation and Cybersecurity & Infrastructure Security Agency warned in a joint advisory about a threat actor...
Canadian Citizen Gets Phone Back from Police – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Canadian Citizen Gets Phone Back from Police After 175 million failed password guesses, a judge rules that the Canadian...
E-Crime Rapper ‘Punchmade Dev’ Debuts Card Shop – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The rapper and social media personality Punchmade Dev is perhaps best known for his flashy videos singing the praises of a...
Bangladeshi Elections Come into DDoS Crosshairs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Muhammad Toqeer via Alamy Stock Photo The end of 2023 saw an uptick in distributed denial-of-service (DDoS)...