Source: www.securityweek.com – Author: Eduard Kovacs The number of Ivanti VPN appliances compromised through exploitation of recent flaws increases and another vulnerability is added to exploited...
VMware vCenter Server Vulnerability Exploited in Wild – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs VMware warns customers that CVE-2023-34048, a vCenter Server vulnerability patched in October 2023, is being exploited in the wild. The...
Top Official Says Kansas Courts Need at Least $2.6 Million to Recover From Cyberattack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Kansas Courts needs funding to cover the costs of bringing computer systems back online, pay vendors, improve cybersecurity and hire...
Unpatched Rapid SCADA Vulnerabilities Expose Industrial Organizations to Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Seven vulnerabilities found in Rapid SCADA could be exploited to gain access to sensitive industrial systems, but they remain unpatched....
Software Supply Chain Security Startup Kusari Raises $8 Million – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Kusari has raised $8 million to help organizations gain visibility into and secure their software supply chain. The post Software...
Nigerian Businesses Face Growing Ransomware-as-a-Service Trade – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: Pablo Lagarto via Alamy Stock Photo Ransomware-as-a-service looks set to fuel an increase in attack in Nigeria,...
Google: Russia’s ColdRiver APT Unleashes Custom ‘Spica’ Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: imageBROKER.com GmbH & Co. KG via Alamy Stock Photo The Russia-backed advanced persistent threat...
Threat Actors Team Up for Post-Holiday Phishing Email Surge – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: devilmaya via Alamy Stock Photo Last week, two different threat actors teamed up to send thousands of...
Citrix Discovers 2 Vulnerabilities, Both Exploited in the Wild – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 2 Min Read Source: Monticello via Shutterstock Two vulnerabilities have been found in NetScaler ADC and...
Cybercrooks Target Docker Containers With Novel Pageview Generator – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 2 Min Read Source: Bob Sharples via Alamy Stock Photo Container-focused cyberattackers have a brand-new...
Nigerian Law Enforcement Agency Advised to Retrain African Cybercriminals – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Mykhailo Polenok via Alamy Stock Photo Online scammers and fraudsters should be retrained as information technology specialists, a...
Anti-Ransomware Coalition Bound to Fail Without Key Adjustments – Source: www.darkreading.com
Source: www.darkreading.com – Author: Shmuel Gihon Source: Olekcii Mach via Alamy Stock Photo COMMENTARY Ransomware is a pervasive issue affecting businesses of all sizes and industries,...
Russian Coldriver Hackers Deploy Malware to Target Western Officials – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Russian threat group Coldriver has expanded its targeting of Western officials with the use of malware to steal sensitive data, Google’s...
Experts Urge Clearer Direction in South Africa’s Cyber Strategy – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 South Africa, known to be ‘the world’s most internet-addicted country,’ finds itself plagued by the internet’s dark underbelly: ransomware. It is...
TA866 Resurfaces in Targeted OneDrive Campaign – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity researchers at Proofpoint have identified the resurgence of TA866 in email threat campaigns after a hiatus of nine months. Writing...
New Malware Campaign Exploits 9hits in Docker Assault – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have uncovered a novel cyber-attack campaign targeting vulnerable Docker services. The attacks mark the first documented case of malware...
Npm Trojan Bypasses UAC, Installs AnyDesk with “Oscompatible” Package – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 19, 2024NewsroomSoftware Security / Spyware A malicious package uploaded to the npm registry has been found deploying a sophisticated remote...
U.S. Cybersecurity Agency Warns of Actively Exploited Ivanti EPMM Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 19, 2024NewsroomCyber Theat / Zero-Day The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a now-patched critical flaw...
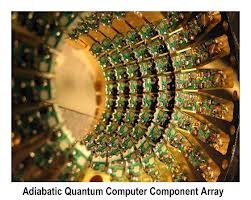
The Quantum Computing Cryptopocalypse – I’ll Know It When I See It – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Quantum Computing Cryptopocalypse – I’ll Know It When I See It Can quantum computing break cryptography? Can it do...
Kansas State University suffered a serious cybersecurity incident – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Kansas State University suffered a serious cybersecurity incident Kansas State University (K-State) suffered a cybersecurity incident that has disrupted part...
CISA adds Chrome and Citrix NetScaler to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA adds Chrome and Citrix NetScaler to its Known Exploited Vulnerabilities catalog U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds...
Google TAG warns that Russian COLDRIVER APT is using a custom backdoor – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Google TAG warns that Russian COLDRIVER APT is using a custom backdoor Google warns that the Russia-linked threat actor COLDRIVER...
PixieFail: Nine flaws in UEFI open-source reference implementation could have severe impacts – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini PixieFail: Nine flaws in UEFI open-source reference implementation could have severe impacts Experts found multiple flaws, collectively named PixieFail, in...
White House Revamps Cybersecurity Hiring Strategy – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici During his initial statements since becoming the National Cyber Director in December, Harry Coker stated that the White House plans...
Akira Ransomware Attacks Surge. Finnish Companies Among Targets – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși The National Cyber Security Centre Finland announced a surge in Akira ransomware attacks. Threat actors used Akira malware in six...
CISA and FBI Reveal Known Androxgh0st Malware IoCs and TTPs – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși CISA and FBI released an advisory on Androxgh0st malware IoCs (Indicators of Compromise) and warned about hackers using this threat...
The Unseen Threats: Anticipating Cybersecurity Risks in 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist Cybersecurity risks increase every year and bludgeon victims who fail to prepare properly. It can feel like crossing a major...
The Benefits of Using DCIM Software for Data Center Cable Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi In the ever-evolving landscape of information technology, the management of data centers has become increasingly complex. The backbone of these...
What Existing Security Threats Do AI and LLMs Amplify? What Can We Do About Them? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maciej Mensfeld In my previous blog post, we saw how the growth of generative AI and Large Language Models has created a...
Defining Good: A Strategic Approach to API Risk Reduction – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nick Rago The cost of not knowing what good is. Could you imagine our interstate highway system without roadway bridges? I don’t...