Source: securityboulevard.com – Author: Corey Sinclair On 22 January, Fortra issued an advisory stating that versions of its GoAnywhere Managed File Transfer (MFT) product suffer from...
USENIX Security ’23 – Mazharul Islam, Marina Sanusi Bohuk, Paul Chung, Thomas Ristenpart, Rahul Chatterjee – Araña: Discovering And Characterizing Password Guessing Attacks In Practice – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Mazharul Islam, Marina Sanusi Bohuk, Paul Chung,...
Five Ways Your CI/CD Pipeline Can Be Exploited – Source: securityboulevard.com
Source: securityboulevard.com – Author: Greg Bulmash We’ve talked about how Continuous Integration and Continuous Delivery (CI/CD) tools can be a source of secrets sprawl. While it’s...
Daniel Stori’s ‘influencer’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2024/01/daniel-storis-influencer/ Category & Tags: Humor,Security Bloggers Network,Daniel Stori,DevOps...
‘Mother of all Breaches’ Leaks — 26 BILLION Records from 12TB Open Bucket – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Researchers discover unsecured database of stolen personal information. And you thought last week’s Naz.API leak was massive? You ain’t seen nothin’...
ADCS Attack Paths in BloodHound — Part 1 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jonas Bülow Knudsen ADCS Attack Paths in BloodHound — Part 1 Since Will Schroeder and Lee Christensen published the Certified Pre-Owned whitepaper, the BloodHound Enterprise...
USENIX Security ’23 – Ming Xu, Jitao Yu, Chuanwang Wang, Shenghao Zhang, Haoqi Wu, Weili Han – Improving Real-World Password Guessing Attacks Via Bi-Directional Transformers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Ming Xu, Jitao Yu, Chuanwang Wang, Shenghao...
Smashing Security podcast #356: Big dumpers, AI defamation, and the slug that slurped – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley This week the podcast is more lavatorial than usual, as we explore how privacy may have gone to sh*t on...
SEC Twitter hack blamed on SIM swap attack – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley The US Securities & Exchange Comission (SEC) has confirmed that hackers managed to seize control of a phone number associated...
North Korean Hackers Using AI in Advanced Cyberattacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 AI-Based Attacks , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime U.S.-Led Sanctions Do Little to Curtail North Korea’s Development...
Watching the Watchdog: Learning from HHS’ Grant Payment Mess – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Anti-Phishing, DMARC , Business Email Compromise (BEC) , Fraud Management & Cybercrime Tight-Lipped Agency’s Next Move in Wake of $7.5M Scam...
Webinar | Future Proof Your Organisation with an Integrated Approach to Decision Making – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Terisa Roberts Global Director, Risk Modelling & Decisioning , SAS Terisa Roberts is a director, and Global Solution lead for Risk...
HPE Fingers Russian State Hackers for Email Hack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime ‘Midnight Blizzard’ Was Inside Company Network for 7 Months...
GSA Sparks Security Fears After Buying Risky Chinese Cameras – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Government , Industry Specific Experts Warn Against Increasing Federal Reliance on Chinese Technology Chris Riotta (@chrisriotta)...
UK Mulls Rollout of New Software Vulnerability Rules – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Geo Focus: The United Kingdom , Geo-Specific , Governance & Risk Management Voluntary Rules Will Set Baseline Security Requirement for Software...
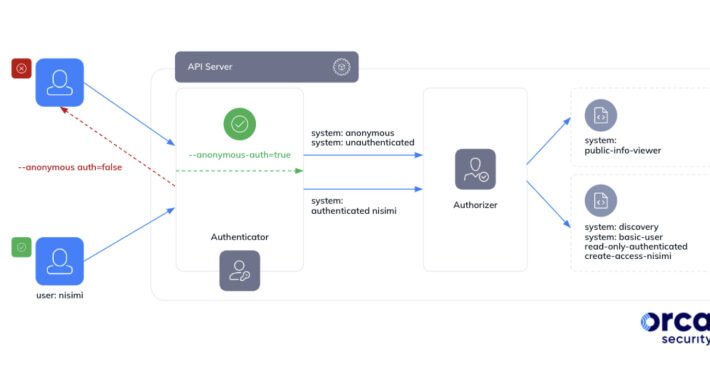
Google Kubernetes Misconfig Lets Any Gmail Account Control Your Clusters – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 24, 2024NewsroomCloud Security / Kubernetes Cybersecurity researchers have discovered a loophole impacting Google Kubernetes Engine (GKE) that could be potentially...
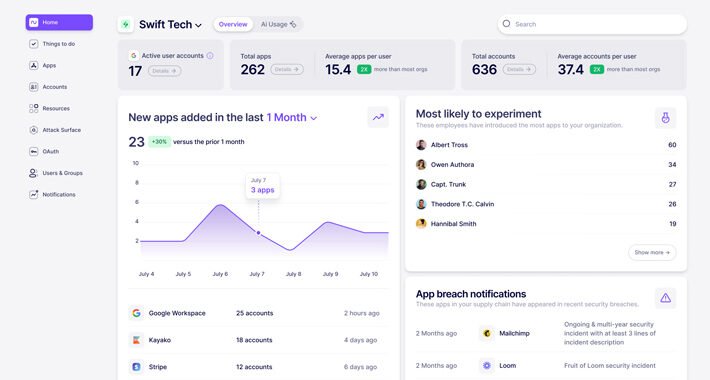
What is Nudge Security and How Does it Work? – Source:thehackernews.com
Source: thehackernews.com – Author: . In today’s highly distributed workplace, every employee has the ability to act as their own CIO, adopting new cloud and SaaS...
Kasseika Ransomware Using BYOVD Trick to Disarms Security Pre-Encryption – Source:thehackernews.com
Source: thehackernews.com – Author: . The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to...
AI Learning Initiative Launches for UAE Women – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: sleepyfellow via Alamy Stock Photo The United Arab Emirates (UAE) National Program for Coders has announced an initiative...
Kasseika Ransomware Linked to BlackMatter in BYOVD Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Marcos Alvarado via Alamy Stock Photo A ransomware group potentially linked to the defunct BlackMatter gang has...
Prompt Security Launches With AI Protection for the Enterprise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: ArtemisDiana via Alamy Stock Photo Prompt Security launched out of stealth today with a solution that uses artificial...
Filling the Cybersecurity Talent Gap – Source: www.darkreading.com
Source: www.darkreading.com – Author: Chip Daniels Source: Christian Horz via Alamy Stock Photo COMMENTARY Our nation is facing some of its greatest challenges ever. Amid rising...
Researchers Map AI Threat Landscape, Risks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Krot Studio via Shutterstock Many of the security problems of large language models (LLMs) boil down to...
Time to Secure Cloud-Native Apps Is Now – Source: www.darkreading.com
Source: www.darkreading.com – Author: George V. Hulme, Contributing Writer 2 Min Read The news headlines are full of breaches and data exposures that are the result...
Learning From Ukraine’s Pioneering Approaches to Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dr. Sean Costigan Source: Mykhailo Polenok via Alamy Stock Photo COMMENTARY Overshadowed by geopolitical tumult and an escalation in sophisticated cyberattacks, a...
Move Fast and Break the Enterprise With AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Michael Bargury Source: Michael Turner via Alamy Stock Photo Working for a large enterprise for many years often leaves you with a...
‘VexTrio’ TDS: The Biggest Cybercrime Operation on the Web? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Amanda Ahn via Alamy Stock Photo A single traffic distribution system (TDS) operator in possession of more...
Why Bulletproof Hosting is Key to Cybercrime-as-a-Service – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The emergence of cybercrime-as-a-service (RaaS) has lowered the entry barrier into cybercrime by allowing cybercriminals to specialize in only one aspect...
X Makes Passkeys Available for US-Based Users – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Social media giant X (formerly Twitter) has made passkeys available as a login option for US-based users on iOS. A post...
Exploit Code Released For Critical Fortra GoAnywhere Bug – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Threat actors could soon strike after a proof-of-concept exploit was published for a critical vulnerability in managed file transfer (MFT) software...