Source: grahamcluley.com – Author: Graham Cluley The iPhone security setting that you should enable right now, the worrying way that AI is predicting what criminals look...
Hackers push USB malware payloads via news, media hosting sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A financially motivated threat actor using USB devices for initial infection has been found abusing legitimate online platforms, including GitHub,...
Police seize record 50,000 Bitcoin from now-defunct piracy site – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The police in Saxony, eastern Germany, have seized 50,000 Bitcoin from the former operator of the pirate site movie2k.to through...
Europcar denies data breach of 50 million users, says data is fake – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Car rental company Europcar says it has not suffered a data breach and that shared customer data is fake after...
Exploit released for Android local elevation flaw impacting 7 OEMs – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A proof-of-concept (PoC) exploit for a local privilege elevation flaw impacting at least seven Android original equipment manufacturers (OEMs) is...
CISA warns of patched iPhone kernel bug now exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA warned today that a patched kernel security flaw affecting Apple iPhones, Macs, TVs, and watches is now being actively...
10 Best Privileged Identity Management Tools (2024) – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu The Importance of Choosing the Right Privilege Identity Management Solution The essence of effective Privileged Identity Management (PIM) lies not...
Cactus Ransomware behind Schneider Electric Data Breach – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Cactus Ransomware claims responsibility for the January 17th Schneider Electric data breach. Schneider Electric confirms hackers got access to their...
HeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 01, 2024NewsroomCryptocurrency / Botnet Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis...
Why the Right Metrics Matter When it Comes to Vulnerability Management – Source:thehackernews.com
Source: thehackernews.com – Author: . How’s your vulnerability management program doing? Is it effective? A success? Let’s be honest, without the right metrics or analytics, how...
Warning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 01, 2024NewsroomNetwork Security / Malware Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known...
CISA Warns of Active Exploitation of Critical Flaws in Apple iOS and macOS – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 01, 2024NewsroomVulnerability / Software Update The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a high-severity flaw impacting...
CFPB’s Proposed Data Rules – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier In October, the Consumer Financial Protection Bureau (CFPB) proposed a set of rules that if implemented would transform how financial...
Aim Security Raises $10M to Secure Generative AI Enterprise Adoption – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE TEL AVIV, Israel–(BUSINESS WIRE)–Aim Security, an Israeli cybersecurity startup offering enterprises a holistic, one-stop shop GenAI security platform, today announced...
Kasperskys ICS CERT Predictions for 2024: Ransomware Rampage, Cosmopolitical Hacktivism, and Beyond – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Woburn, MA – January 31, 2024 — Kaspersky today releases its Industrial Control Systems Cyber Emergency Response Team (ICS CERT) predictions...
Incognia Secures $31M to Meet Demand for Proactive Approach to Fraud Prevention – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE San Jose, CA – Jan 31, 2024, at 10:00 am ET – Today, Incognia, the innovator in location identity solutions, is announcing...
Ransomware Groups Gain Clout With False Attack Claims – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Source: Mykola Lytvynenko via Alamy Stock Photo The cybersecurity community is getting duped by fake breach claims...
Fulton County Suffers Power Outages as Cyberattack Continues – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Allen Creative / Steve Allen via Alamy Stock Photo As Fulton County...
‘Leaky Vessels’ Cloud Bugs Allow Container Escapes Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Jack Sullivan via Alamy Stock Photo Researchers have uncovered a set of four vulnerabilities in container engine...
Johnson Controls Ransomware Cleanup Costs Top $27M and Counting – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 1 Min Read Source: Chroma Craft Media Group via Alamy Stock Photo Johnson Controls International...
More Ivanti VPN Zero-Days Fuel Attack Frenzy as Patches Finally Roll – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: imageBROKER via Alamy Stock Photo Ivanti has finally begun patching a pair of zero-day...
Looted RIPE Credentials for Sale on the Dark Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: Alicia Buller, Contributing Writer Source: Brian Jackson via Alamy Stock Photo Hundreds of network operator credentials stolen via compromised RIPE accounts were...
Dubai Cyber Force Names First Accredited Companies – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Andriy Popov via Alamy Stock Photo Eight companies have become the first accredited cybersecurity service providers to be...
AppOmni Harnesses Google Data Center in Australia to Address Regional Demand for Specialised SaaS Security Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tamara Bailey, Content Marketing Specialist @ AppOmni San Francisco, CA – [January 31, 2024] – AppOmni, the pioneer of SaaS security posture...
News alert: Reken raises $10M from Greycroft to protect against generative AI-enabled fraud – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido San Francisco, Calif., Jan. 31, 2024 – Reken, an AI & cybersecurity company, today announced the close of its $10M oversubscribed...
Daniel Stori’s ‘Help’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the webcomic talent of the inimitable Daniel Stori at Turnoff.US. Permalink *** This is a Security Bloggers Network syndicated...
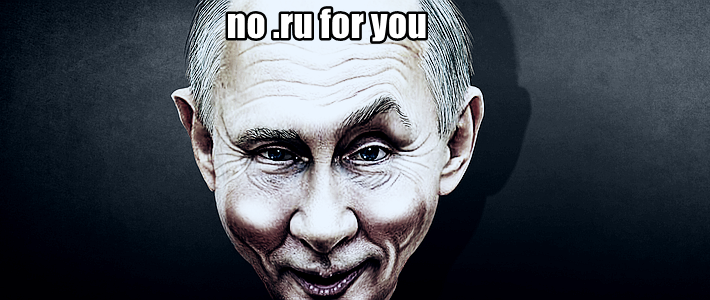
Russian Internet Outage: DNSSEC Oops or Ukraine Hack? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Government ministry denies hackers hacked its network infrastructure. The Russian internet was down for hours yesterday: Everything under the .ru and...
Tax Season is Upon Us, and So Are the Scammers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt It’s still relatively early in the year, but bad actors are already targeting accounting and finance organizations as well as...
Guardians of IoT: Addressing IoT security vulnerabilities in electric vehicles and charging stations – Source: securityboulevard.com
Source: securityboulevard.com – Author: The Coalfire Blog The surge in electric vehicles (EVs) and expanding EV charging infrastructure represents a significant stride toward sustainable and environmentally...
Supply Chain Security and NIS2: What You Need to Know – Source: securityboulevard.com
Source: securityboulevard.com – Author: Flare The Network Information Systems Directive (NIS2) and its predecessor NIS focus on risk management for organizations. The EU states that the...