Source: securityboulevard.com – Author: Sift Trust and Safety Team Business is booming for online food delivery services and apps, meal kit providers, and grocery options. The...
USENIX Security ’23 – Black-box Adversarial Example Attack Towards FCG Based Android Malware Detection Under Incomplete Feature Information – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Author/Presenters: Heng Li, Zhang Cheng, Bang Wu, Liheng Yuan, Cuiying Gao, Wei Yuan, Xiapu Luo Many thanks to USENIX for...
A Recap of Cybersecurity in 2023 and What’s Ahead for 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Ratner With high-profile breaches in the news across the world and increasingly sophisticated threats, cybersecurity professionals face more challenges than ever...
Water Sector Leaders Urge Congress to Fund Cyber Mandates – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security The Water and Wastewater Sector Faces Growing Cybersecurity Risks, Officials Warn Chris Riotta (@chrisriotta) • January 31, 2024...
Top Tips to Avoid Corporate Social Media Account Hijacking – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Social Media Not a Good Look: Hijacked @SECgov Social Media Account Spews Bitcoin Rumors Mathew J....
Pushing the Healthcare Sector to Improve Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Getting the health sector to vastly improve the state of its cybersecurity will take much more than the recent issuance of...
Protecting Your Cloud Assets with CIS Benchmarks & CIS Controls – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Ivanti Discloses Additional Zero-Day That Is Being Exploited – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management Company Starts Patch Rollout for Flaws Exploited...
Webinar | Navigating the Perils and the Promise of AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Sandra Joyce VP, Mandiant Intelligence Sandra Joyce is a cybersecurity leader, leading Mandiant Intelligence since 2017. She oversees threat research activities...
Proof of Concept: How Do We Ensure Ethical AI Systems? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 AI-Based Attacks , Artificial Intelligence & Machine Learning , Fraud Management & Cybercrime Also: Safeguarding AI Vulnerabilities From Cyber Adversaries Anna...
Here’s How the FBI Stopped a Major Chinese Hacking Campaign – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security FBI and CISA Detail Operation to Prevent China’s Attacks on Critical Infrastructure Chris Riotta (@chrisriotta) • January 31,...
Pawn Storm’s Stealthy Net-NTLMv2 Assault Revealed – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Pawn Storm, an advanced persistent threat (APT) actor also known as APT28, has been targeting high-value entities globally, employing a range...
EU Launches First Cybersecurity Certification for Digital Products – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The EU has adopted its first Cybersecurity Certification scheme as part of efforts to boost cybersecurity of IT products and services...
US Senators Propose Cybersecurity Agriculture Bill – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new bipartisan bill proposed by two US Senators looks to bolster the cybersecurity of the food and agriculture sector. If...
Sysdig Report Exposes 91% Failure in Runtime Scans – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A substantial 91% of runtime scans are failing within organizations, signaling a significant reliance on identifying issues rather than preventing them,...
US Sanctions Egyptian IT Experts Aiding ISIS in Cybersecurity – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US government has announced sanctions against two Egyptian IT experts for providing cybersecurity support and training to the terrorist organization...
Citibank Sued For Failing to Protect Fraud Victims – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New York’s attorney general, Letitia James, yesterday launched legal action against one of America’s biggest banks for allegedly failing to adequately protect...
City Cyber Taskforce Launches to Secure Corporate Finance – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Two of the UK’s leading accounting and security bodies are teaming up with others to launch a new taskforce today designed...
RunC Flaws Enable Container Escapes, Granting Attackers Host Access – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 31, 2024NewsroomSoftware Security / Linux Multiple security vulnerabilities have been disclosed in the runC command line tool that could be...
Alert: Ivanti Discloses 2 New Zero-Day Flaws, One Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 31, 2024NewsroomVulnerability / Zero Day Ivanti is alerting of two new high-severity flaws in its Connect Secure and Policy Secure...
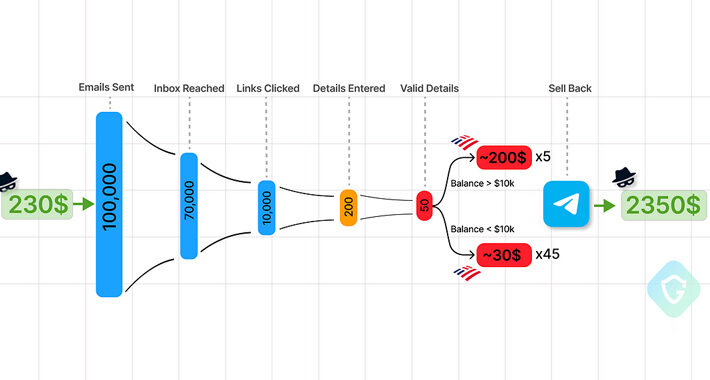
Telegram Marketplaces Fuel Phishing Attacks with Easy-to-Use Kits and Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 31, 2024NewsroomCyber Crime / Hacking News Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to...
CISA adds Apple improper authentication bug to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA adds Apple improper authentication bug to its Known Exploited Vulnerabilities catalog U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds...
Ivanti warns of a new actively exploited zero-day – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ivanti warns of a new actively exploited zero-day Ivanti warns of two new vulnerabilities in its Connect Secure and Policy...
Threat actors exploit Ivanti VPN bugs to deploy KrustyLoader Malware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors exploit Ivanti VPN bugs to deploy KrustyLoader Malware Threat actors are exploiting recently disclosed zero-day flaws in Ivanti...
Data leak at fintech giant Direct Trading Technologies – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Data leak at fintech giant Direct Trading Technologies Sensitive data and trading activity of over 300K traders leaked online by...
Root access vulnerability in GNU Library C (glibc) impacts many Linux distros – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Root access vulnerability in GNU Library C (glibc) impacts many Linux distros Qualys researchers discovered a root access flaw, tracked...
Italian data protection authority said that ChatGPT violated EU privacy laws – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Italian data protection authority said that ChatGPT violated EU privacy laws Italian data protection authority regulator authority Garante said that...
FBI disrupts Chinese botnet by wiping malware from infected routers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The FBI has disrupted the KV Botnet used by Chinese Volt Typhoon state hackers to evade detection during attacks targeting...
CISA: Vendors must secure SOHO routers against Volt Typhoon attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA has urged manufacturers of small office/home office (SOHO) routers to ensure their devices’ security against ongoing attacks attempting to hijack...
Johnson Controls says ransomware attack cost $27 million, data stolen – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Johnson Controls International has confirmed that a September 2023 ransomware attack cost the company $27 million in expenses and led...