Source: www.darkreading.com – Author: DJ Singh, Mark Trump Source: ElenaBs via Alamy Stock Vector COMMENTARY The era of intelligent operations is already here, but some operational...
Cloudflare Falls Victim to Okta Breach, Atlassian Systems Cracked – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Cloudflare was a victim of the wide-ranging Okta supply-chain campaign last fall, with a data...
Saudi Arabia Debuts ‘Generative AI for All’ Program – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: sleepyfellow via Alamy Stock Photo Saudi Arabia has rolled out a generative artificial intelligence (GenAI)...
CMMC Is the Starting Line, Not the Finish – Source: www.darkreading.com
Source: www.darkreading.com – Author: Chris Petersen Source: Cultura Creative RF via Alamy Stock Photo COMMENTARY Over the past few years, it has become painfully clear that...
3 ISIS Members Slapped With Sanctions From US Treasury – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer 2 Min Read Source: Songquan Deng via Alamy Stock Photo The US Department of the Treasury’s Office of...
Recognizing Security as a Strategic Component of Business – Source: www.darkreading.com
Source: www.darkreading.com – Author: Michael Armer Source: Anna Berkut via Alamy Stock Photo COMMENTARY Amid an onslaught of ransomware, supply chain, and other cyberattacks against business...
FTC slams Blackbaud for “shoddy security” after hacker stole data belonging to thousands of non-profits and millions of people – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Data and software services firm Blackbaud’s cybersecurity was criticised as “lax” and “shoddy” by the United States Federal Trade Commission...
China is hacking Wi-Fi routers for attack on US electrical grid and water supplies, FBI warns – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Got two-and-a-half hours to spare? Maybe instead of settling down to watch “Mission: Impossible – Dead Reckoning Part One”, you...
A Self-Enforcing Protocol to Solve Gerrymandering – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier In 2009, I wrote: There are several ways two people can divide a piece of cake in half. One way...
Facebook’s Extensive Surveillance Network – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Consumer Reports is reporting that Facebook has built a massive surveillance network: Using a panel of 709 volunteers who shared...
Former CIA Engineer Sentenced to 40 Years for Leaking Classified Documents – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 02, 2024NewsroomNational Security / Data Breach A former software engineer with the U.S. Central Intelligence Agency (CIA) has been sentenced...
Cloudzy Elevates Cybersecurity: Integrating Insights from Recorded Future to Revolutionize Cloud Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 02, 2024The Hacker NewsThreat Intelligence / Cloud Security Cloudzy, a prominent cloud infrastructure provider, proudly announces a significant enhancement in...
INTERPOL Arrests 31 in Global Operation, Identifies 1,900+ Ransomware-Linked IPs – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 02, 2024NewsroomCyber Crime / Malware An INTERPOL-led collaborative operation targeting phishing, banking malware, and ransomware attacks has led to the...
Cloudflare Breach: Nation-State Hackers Access Source Code and Internal Docs – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 02, 2024NewsroomData Breach / Cloud Security Cloudflare has revealed that it was the target of a likely nation-state attack in...
FTC orders Blackbaud to boost security after massive data breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Blackbaud has settled with the Federal Trade Commission after being charged with poor security and reckless data retention practices, leading...
Cloudflare hacked using auth tokens stolen in Okta attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Cloudflare disclosed today that its internal Atlassian server was breached by a suspected ‘nation state attacker’ who accessed its Confluence...
Microsoft fixes connection issue affecting Outlook email apps – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has fixed a known issue causing desktop and mobile email clients to fail to connect when using Outlook.com accounts....
More Android apps riddled with malware spotted on Google Play – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas An Android remote access trojan (RAT) known as VajraSpy was found in 12 malicious applications, six of which were available...
PurpleFox malware infects thousands of computers in Ukraine – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Computer Emergency Response Team in Ukraine (CERT-UA) is warning about a PurpleFox malware campaign that has infected at least...
Google shares fix for Pixel phones hit by bad system update – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Google has shared a temporary fix for owners of Google Pixel devices that were rendered unusable after installing the January...
New Windows Event Log zero-day flaw gets unofficial patches – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Free unofficial patches are available for a new Windows zero-day flaw dubbed EventLogCrasher that lets attackers remotely crash the Event Log...
CISA orders federal agencies to disconnect Ivanti VPN appliances by Saturday – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA has ordered U.S. federal agencies to disconnect all Ivanti Connect Secure and Policy Secure VPN appliances vulnerable to multiple...
Heimdal Partners with Jupiter Technology to Distribute Cybersecurity Solutions in Japan – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici We have partnered with Jupiter Technology Corporation, who will distribute our cybersecurity products across Japan as part of a long-term...
USENIX Security ’23 – Cas Cremers, Charlie Jacomme, Aurora Naska – Formal Analysis of Session-Handling in Secure Messaging: Lifting Security from Sessions to Conversations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Thursday, February 1, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Diving into the 2024 Security Megatrends – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Cybersecurity is a fast-paced and constantly changing industry. Ongoing technological advancements, new paradigms and evolving threat actor techniques make the...
Telegram is a Wide-Open Marketplace for Phishing Tools – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The encrypted messaging app Telegram has become a veritable marketplace for bad actors who want to launch effective phishing campaigns...
The SOC 2 Effect: Elevating Security and Trust in Netography Fusion – Source: securityboulevard.com
Source: securityboulevard.com – Author: Raymond Kirk The SOC 2 Effect: Elevating Security and Trust in Netography Fusion Raymond Kirk, Product Manager Satisfying the System and Organization...
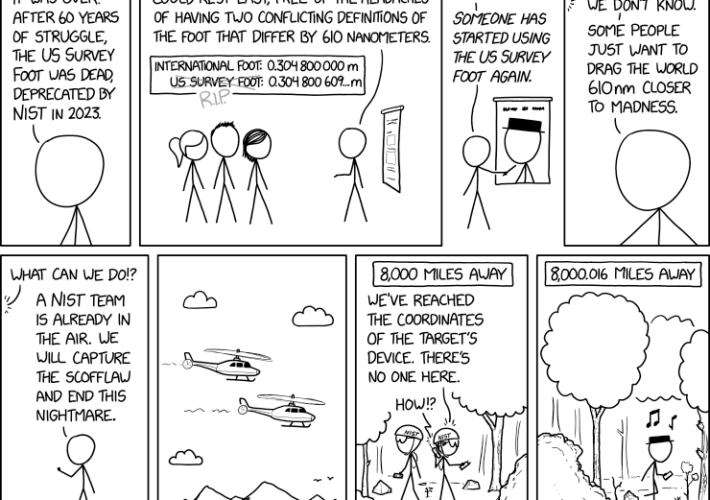
Randall Munroe’s XKCD ‘US Survey Foot’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Improved Security Agility and Adaptability with Dynamic Runtime Lists | Impart Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Impart Security Blog We’re proud to announce Impart Security’s newest release, Dynamic Runtime Lists, which are purpose-built to enable security teams...
Optimize Control Health Management Across Business Levels: Introducing Scopes – Source: securityboulevard.com
Source: securityboulevard.com – Author: Hyperproof Team Managing controls across multiple business units becomes increasingly challenging and costly as operational requirements evolve. To help compliance leaders efficiently...