Source: www.bleepingcomputer.com – Author: Lawrence Abrams Attacks on hospitals continued this week, with ransomware operations disrupting patient care as they force organization to respond to cyberattacks....
AnyDesk says hackers breached its production servers, reset passwords – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams AnyDesk confirmed today that it suffered a recent cyberattack that allowed hackers to gain access to the company’s production systems....
Lurie Children’s Hospital took systems offline after cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Lurie Children’s Hospital in Chicago was forced to take IT systems offline after a cyberattack, disrupting normal operations and delaying...
BTC-e server admin indicted for laundering ransom payments, stolen crypto – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Aliaksandr Klimenka, a Belarusian and Cypriot national, has been indicted in the U.S. for his involvement in an international cybercrime...
Interpol operation Synergia takes down 1,300 servers used for cybercrime – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas An international law enforcement operation code-named ‘Synergia’ has taken down over 1,300 command and control servers used in ransomware, phishing,...
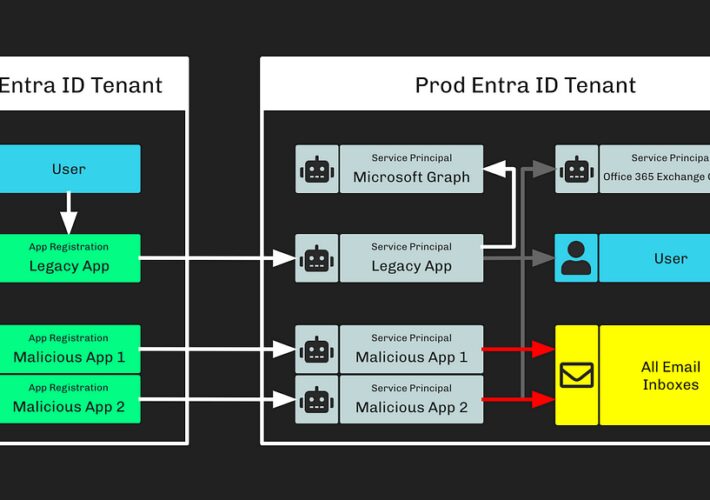
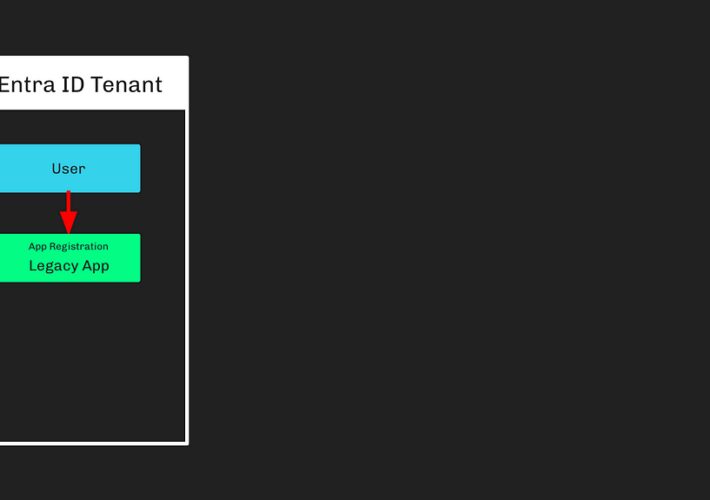
Microsoft Breach — How Can I See This In BloodHound? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Stephen Hinck Microsoft Breach — How Can I See This In BloodHound? Summary On January 25, 2024, Microsoft announced Russia’s foreign intelligence service (i.e.,...
Microsoft Breach — What Happened? What Should Azure Admins Do? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Andy Robbins Microsoft Breach — What Happened? What Should Azure Admins Do? On January 25, 2024, Microsoft published a blog post that detailed their recent...
MSP DMARC Journey For Effective Lead Generation: Watchdog Cyber’s Sucess Story – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anush Yolyan ABOUT THE CLIENT Headquarters: Spring Lake, Michigan Website: www.watchdogcyber.com Founded: 2022 Industry: Managed Service Provider Watchdog Cyber delivers proactive cybersecurity...
USENIX Security ’23 – Anrin Chakraborti, Duke University; Darius Suciu, Radu Sion – Wink: Deniable Secure Messaging – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Anrin Chakraborti, Duke University; Darius Suciu, Radu...
Survey Surfaces Raft of Cloud Security Challenges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard A global survey of 414 IT practitioners published this week found 40% of respondents are relying on legacy platforms and...
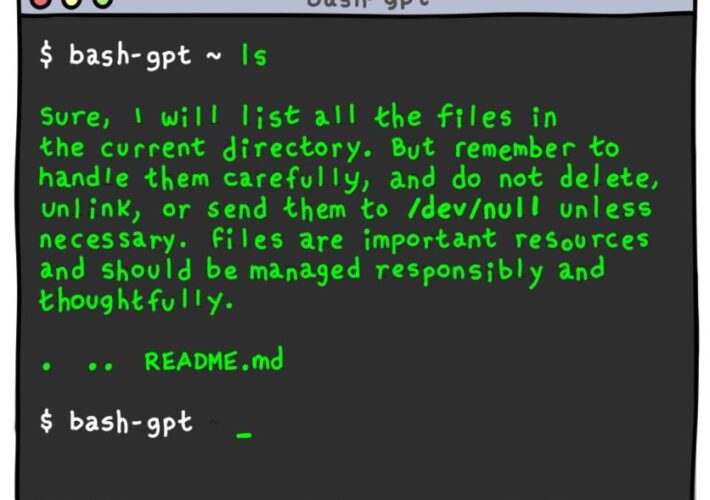
Daniel Stori’s ‘bash-gpt’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the webcomic talent of the inimitable Daniel Stori at Turnoff.US. Permalink *** This is a Security Bloggers Network syndicated...
The Secret’s Out: How Stolen Okta Auth Tokens Led to Cloudflare Breach – Source: securityboulevard.com
Source: securityboulevard.com – Author: Thomas Segura What Happened? Cloudflare’s internal Atlassian systems were breached using tokens and service accounts compromised from a previous Okta breach. The...
USENIX Security ’23 – David Balbás, Daniel Collins, Serge Vaudenay – Cryptographic Administration for Secure Group Messaging – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – David Balbás, Daniel Collins, Serge Vaudenay –...
Microsoft Ditches C# for Rust: M365 Core Gets Safety and Perf Boosts – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Microsoft 365 “Core Platform Substrate” gets rewrite in Rust language. A job ad seems to say Microsoft is going all in...
Understanding the Connection Between IoT Vulnerabilities and Home Network Intrusions – Source: securityboulevard.com
Source: securityboulevard.com – Author: daniel.floyd@blackcloak.io Our homes are increasingly becoming a web of interconnected devices. From smart thermostats to connected refrigerators, the Internet of Things (IoT)...
Cyber Fail: When Ransomware Gangs Get Careless – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyber Fail , Fraud Management & Cybercrime , Ransomware Also: Rampant App Vulnerabilities, Cloud Misconfiguration and Why CISOs Matter Anna Delaney...
More Ransomware Victims Are Declining to Pay Extortionists – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware While Average Falls Below 30%, We’re Still Far From Seeing Criminal Profits Dry Up Mathew...
ISMG Editors: Why Are Microsoft’s Systems So Vulnerable? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management Also: AI in Cloud Security, Integrating Zero...
FritzFrog Botnet Exploits Log4Shell – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management Botnet Looks for Vulnerable Internal Network Machines Prajeet Nair (@prajeetspeaks) • February 2, 2024...
UK Lawmakers Push Ahead With Revised Snoopers’ Charter – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Privacy The Investigatory Powers Bill Will Allow Police to Collect More Data Akshaya Asokan (asokan_akshaya) •...
Operation Synergia led to the arrest of 31 individuals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Operation Synergia led to the arrest of 31 individuals Pierluigi Paganini February 02, 2024 An international law enforcement operation, named...
Ex CIA employee Joshua Adam Schulte sentenced to 40 years in prison – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ex CIA employee Joshua Adam Schulte sentenced to 40 years in prison Pierluigi Paganini February 02, 2024 A former software...
Cloudflare breached on Thanksgiving Day, but the attack was promptly contained – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cloudflare breached on Thanksgiving Day, but the attack was promptly contained Pierluigi Paganini February 02, 2024 Cloudflare revealed that a...
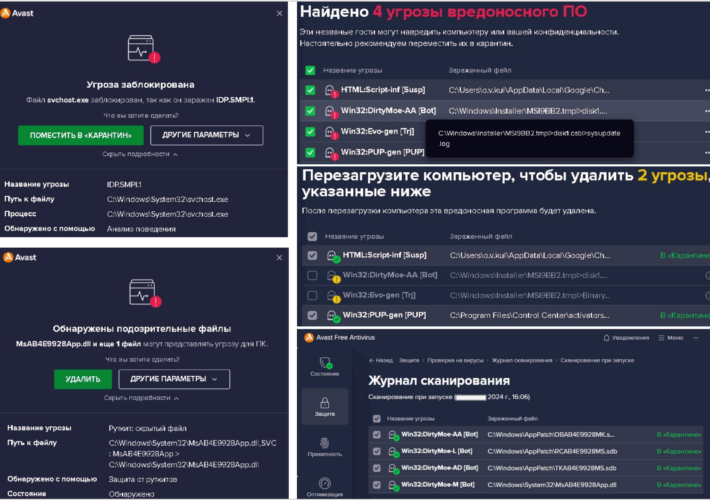
PurpleFox malware infected at least 2,000 computers in Ukraine – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini PurpleFox malware infected at least 2,000 computers in Ukraine Pierluigi Paganini February 02, 2024 The Computer Emergency Response Team in...
Man sentenced to six years in prison for stealing millions in cryptocurrency via SIM swapping – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Man sentenced to six years in prison for stealing millions in cryptocurrency via SIM swapping Pierluigi Paganini February 01, 2024...
Russian APT28 Hackers Targeting High-Value Orgs with NTLM Relay Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Russian state-sponsored actors have staged NT LAN Manager (NTLM) v2 hash relay attacks through various methods from April 2022 to November...
DirtyMoe Malware Infects 2,000+ Ukrainian Computers for DDoS and Cryptojacking – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 02, 2024NewsroomCryptojacking / Malware The Computer Emergency Response Team of Ukraine (CERT-UA) has warned that more than 2,000 computers in...
Interpol’s ‘Synergia’ Op Nabs Dozens of Cybercriminals, Zaps Global C2s – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Bruno Haver via Alamy Stock Photo An operation to combat the surge of phishing, banking malware, and ransomware attacks worldwide saw command-and-control (C2)...
South African Railways Lost Over $1M in Phishing Scam – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: Graham Montanari via Alamy Stock Photo South Africa’s railway agency lost some 30.6 million rand (US$1.6 million)...
Google Play Used to Spread ‘Patchwork’ APT’s Espionage Apps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Art of Food via Alamy Stock Photo The Indian APT group Patchwork, known...