Source: securityaffairs.com – Author: Pierluigi Paganini U.S. Gov imposes visa restrictions on individuals misusing Commercial Spyware Pierluigi Paganini February 06, 2024 The U.S. government imposes visa...
HPE is investigating claims of a new security breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini HPE is investigating claims of a new security breach Pierluigi Paganini February 06, 2024 Hewlett Packard Enterprise (HPE) is investigating...
Teaching LLMs to Be Deceptive – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Interesting research: “Sleeper Agents: Training Deceptive LLMs that Persist Through Safety Training“: Abstract: Humans are capable of strategically deceptive behavior:...
Smashing Security podcast #358: Hong Kong hijinks, pig butchers, and poor ransomware gangs – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Is this the real life? Is this just fantasy? A company in Hong Kong suffers a sophisticated deepfake duping, be...
The toothbrush DDoS attack: How misinformation spreads in the cybersecurity world – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Here are a few headlines from the last 24 hours or so, about a supposed smart toothbrush botnet launching a...
Google Cybersecurity Action Team Threat Horizons Report #9 Is Out! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anton Chuvakin This is my completely informal, uncertified, unreviewed and otherwise completely unofficial blog inspired by my reading of our seventh Threat...
Are You Prepared for FedRAMP Rev. 5? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kade Hennings This year we joined other organizations in going through the FedRAMP Revision 5 transition project. If you’re unfamiliar, the Federal Risk...
Midnight Blizzard and Cloudflare-Atlassian Cybersecurity Incidents – Source: securityboulevard.com
Source: securityboulevard.com – Author: Beverly Nevalga, Sr. Content Marketing Manager @ AppOmni The Midnight Blizzard and Cloudflare-Atlassian cybersecurity incidents raised alarms about the vulnerabilities inherent in...
Product Highlight | Google Docs Phishing Scam Alert – Source: securityboulevard.com
Source: securityboulevard.com – Author: Katie Fritchen Our customer support team is always busy helping customers audit and improve their Google Workspace & Microsoft 365 security settings....
USENIX Security ’23 – Hengkai Ye, Song Liu, Zhechang Zhang, and Hong Hu – VIPER: Spotting Syscall-Guard Variables for Data-Only Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open...
Google Pushes Software Security Via Rust, AI-Based Fuzzing – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Google is making moves to help developers ensure that their code is secure. The IT giant this week said it...
Randall Munroe’s XKCD ‘Relationship Advice’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Credential Stuffing: Who Owns the Risk? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Reece Baldwin Kasada was recently in the news after identifying a credential stuffing campaign targeting Australian retail, fast food, and entertainment outlets....
USENIX Security ’23 – Hengkai Ye, Song Liu, Zhechang Zhang, and Hong Hu – VIPER: Spotting Syscall-Guard Variables for Data-Only Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open...
Lloyd’s of London Announces Investment in Axio – Source: securityboulevard.com
Source: securityboulevard.com – Author: Axio Wednesday, February 7, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features...
China’s Cyberattackers Maneuver to Disrupt US Critical Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The US Cybersecurity and Infrastructure Security Agency (CISA) has issued a report detailing how the...
Linux Distros Hit by RCE Vulnerability in Shim Bootloader – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Fauzi Muda via Shutterstock Linux shim, a small piece of code that many major Linux distros use...
Fulton County Court System Still Hobbled by Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Gregg Vignal via Alamy Stock Photo After Fulton County, Georgia, suffered a cyberattack and subsequent power outage at...
New Report From Flare Highlights Pervasive Threat of Initial Access Brokers in NATO Countries – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Montreal, Quebec, Canada – February 6, 2024 – Flare, the leading Continuous Threat Exposure Management (CTEM) solution provider, has released a new report...
Patch Now: Critical TeamCity Bug Allows for Server Takeovers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Andre Boukreev via Shutterstock JetBrains has patched a critical security vulnerability in its TeamCity On-Premises server that...
Q&A: Tel Aviv Railway Project Bakes In Cyber Defenses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Oleg Zaslavsky via Alamy Stock Photo Railway networks are suffering an increase in cyberattacks, most...
UAE Banks Conduct Cyber War Games Exercise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Aleksandar Tomic via Alamy Stock Photo Banks in the United Arab Emirates (UAE) recently participated in a simulated...
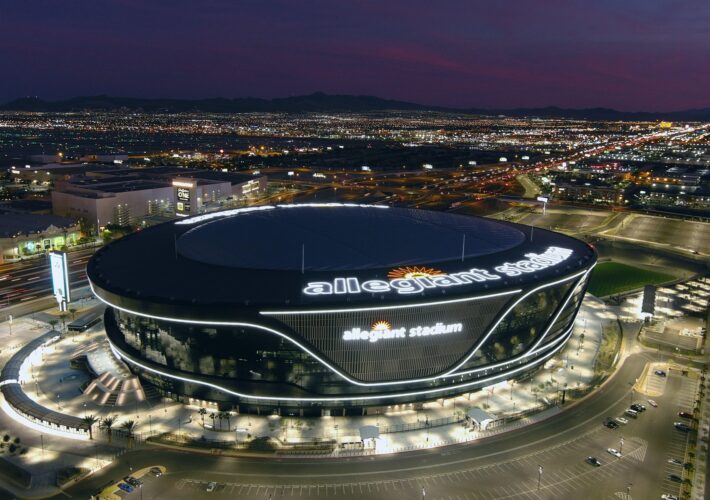
How to Prepare for Elevated Cybersecurity Risk at the Super Bowl – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kris Philipsen Allegiant StadiumSource: Kirby Lee via Alamy Stock Photo COMMENTARY Major sporting events such as the Super Bowl are fertile ground...
As Smart Cities Expand, So Do the Threats – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: jamesteohart via Shutterstock For technologists, building smart cities is not an aspirational goal but a matter of...
Cisco Adds New Security and AI Capabilities in Next Step Toward Cisco Networking Cloud Vision – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE AMSTERDAM, Feb. 6, 2024 /PRNewswire/ — CISCO LIVE EMEA — Cisco (NASDAQ: CSCO), the leader in networking and security, today introduced new capabilities and technologies...
4 Threat Hunting Techniques to Prevent Bad Actors in 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Nicole Rennolds Today’s cybersecurity threats are highly sophisticated; bad actors are using technology like no-code malware and AI-generated phishing campaigns to breach...
Securden Password Vault Review 2024: Security, Pricing, Pros & Cons – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Securden fast facts Our rating: 3.7 stars out of 5 Pricing: Ask for a quote. Key features Strong activity tracking....
How to Use Enpass: A Step-by-Step Guide for Beginners – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Enpass is an offline password manager that can integrate with third-party cloud services like Google Drive and Dropbox. In this...
To BEC or Not to BEC: How to Approach New Email Authentication Requirements – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 OnDemand | The Tools & Technology You Need to Meet Google/Yahoo Email Authentication Requirements Proofpoint • February 7, 2024 ...
Powering ANZ Grids: Navigating Cyber Threats in the Energy Sector – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Mark Cooper President and Founder, PKI Solutions Mark B. Cooper, president and founder of PKI Solutions, has been known as “The...