The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NETCAT FOR PENTESTER COMPREHENSIVE GUIDE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Why Higher Education Is So Vulnerable to Cyber Attacks — And What to Do – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin By Zac Amos, Features Editor, ReHack Cyberattacks are a growing problem worldwide as they can cause significant damage to any organization,...
Why Companies Are Still Investing in Tech During an Economic Slowdown – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin By Luke Wallace, VP of Engineering at Bottle Rocket With rising oil prices, higher interest rates, and an economic downturn plaguing...
Anycubic 3D printers hacked worldwide to expose security flaw – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Image: Midjourney According to a wave of online reports from Anycubic customers, someone hacked their 3D printers to warn that...
Malicious AI models on Hugging Face backdoor users’ machines – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas At least 100 instances of malicious AI ML models were found on the Hugging Face platform, some of which can...
New executive order bans mass sale of personal data to China, Russia – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan U.S. President Joe Biden has signed an executive order that aims to ban the bulk sale and transfer of Americans’...
Rhysida ransomware wants $3.6 million for children’s stolen data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Rhysida ransomware gang has claimed the cyberattack on Lurie Children’s Hospital in Chicago at the start of the month....
Kali Linux 2024.1 released with 4 new tools, UI refresh – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Kali Linux has released version 2024.1, the first version of 2024, with four new tools, a theme refresh, and desktop...
Ransomware gang claims they stole 6TB of Change Healthcare data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Image: Midjourney The BlackCat/ALPHV ransomware gang has officially claimed responsibility for a cyberattack on Optum, a subsidiary of UnitedHealth Group...
LockBit ransomware returns to attacks with new encryptors, servers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The LockBit ransomware gang is once again conducting attacks, using updated encryptors with ransom notes linking to new servers after...
Lazarus hackers exploited Windows zero-day to gain Kernel privileges – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas North Korean threat actors known as the Lazarus Group exploited a flaw in the Windows AppLocker driver (appid.sys) as a...
Epic Games: “Zero evidence” we were hacked by Mogilevich gang – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Epic Games said they found zero evidence of a cyberattack or data theft after the Mogilevich extortion group claimed to...
Japan warns of malicious PyPi packages created by North Korean hackers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Japan’s Computer Security Incident Response Team (JPCERT/CC) is warning that the notorious North Korean hacking group Lazarus has uploaded four...
Meet ‘XHelper,’ the All-in-One Android App for Global Money Laundering – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: ronstik via Alamy Stock Photo Cybercriminals are laundering stolen funds through ordinary people, thanks to a small...
US Government Expands Role in Software Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Pitinan Piyavatin via Alamy Stock Photo The Biden administration continues to push for closer public-private partnerships to...
‘Voltzite’ Zaps African Utilities as Part of Volt Typhoon’s Onslaught – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Jacek Sopotnicki via Alamy Stock Photo “Voltzite,” the operational technology (OT)-focused unit within China’s...
Cyberattackers Lure EU Diplomats With Wine-Tasting Offers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Katerina Solovyeva via Alamy Stock Photo Europeans are known to enjoy fine wine, a cultural characteristic that’s...
Converging State Privacy Laws and the Emerging AI Challenge – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jason Eddinger Source: Skorzewiak via Alamy Stock Photo Eight US states passed data privacy legislation in 2023, and in 2024, laws will...
‘Savvy Seahorse’ Hackers Debut Novel DNS CNAME Trick – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Mark Conlin via Alamy Stock Photo A newly discovered threat actor is running an investment scam through...
GDPR Security Pack – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: One of the key requirements of the General Data Protection Regulation is a demonstrated effort to enforce security measures that safeguard customer...
USENIX Security ’23 – Yu Chen, Yang Yu, Lidong Zhai – InfinityGauntlet: Expose Smartphone Fingerprint Authentication to Brute-force Attack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, February 28, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
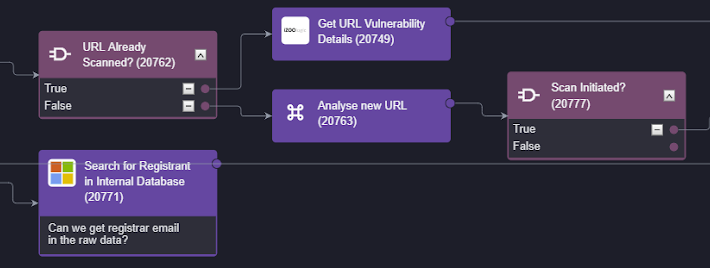
Why Smart SOAR is the Best SOAR for iZOOlogic – Source: securityboulevard.com
Source: securityboulevard.com – Author: Pierre Noujeim The collaboration between Smart SOAR (Security Orchestration, Automation, and Response) and iZOOlogic offers a comprehensive solution to protect your brand...
Navigating the Waters of Generative AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: brianrobertson Part I: The Good and the Bad of AI Few would argue that 2023 was the year AI, specifically generative AI...
FBI Warns: Ubiquiti EdgeRouter is STILL Not Secure – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Fancy Bear still hacking ubiquitous gear, despite patch availability. Ubiquiti’s EdgeRouter ships with its config open to the internet and default...
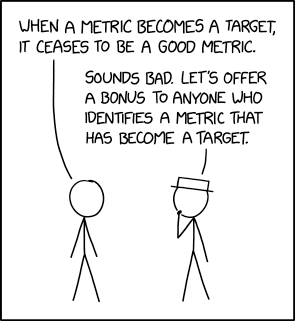
Randall Munroe’s XKCD ‘Goodhart’s Law’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored by Marc Handelman. Read the original post...
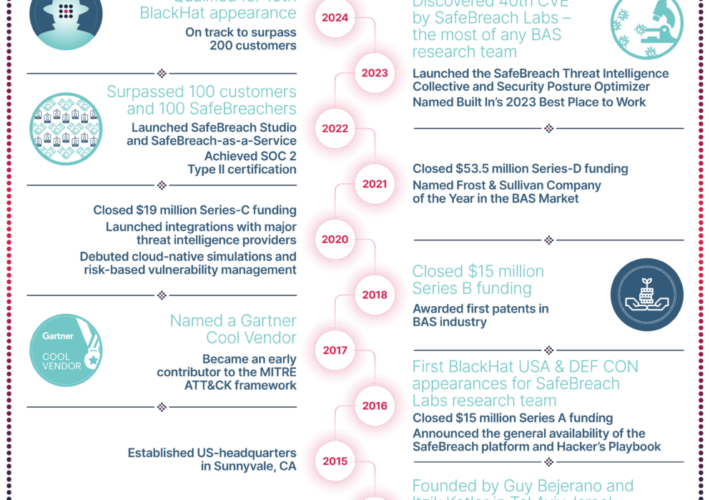
10 Years of SafeBreach – Source: securityboulevard.com
Source: securityboulevard.com – Author: SafeBreach We all know cybersecurity is a team sport—one that is enhanced and optimized by the collective knowledge of a committed community....
Building Cyber Resilience: Insights into NIST CSF 2.0 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maahnoor Siddiqui After several years of deliberation and collaboration with industry experts, NIST has released the newest version of the NIST CSF....
Imperva Customers are Protected Against New SQL Injection Vulnerability in WordPress Plugin – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gabi Stapel A critical security flaw, identified as CVE-2024-1071, was discovered in the Ultimate Member plugin for WordPress, affecting over 200,000 active...
Account Takeover Protection: Risks, Targets and Prevention Strategies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sarah Hunter-Lascoskie When a customer signs up for a loyalty program or otherwise entrusts your organization with their personal and sensitive data,...