The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blue Team Notes
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BEST PRACTICES FOR CYBER CRISIS MANAGEMENT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Automated Threat Modeling with Threat Canvas
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
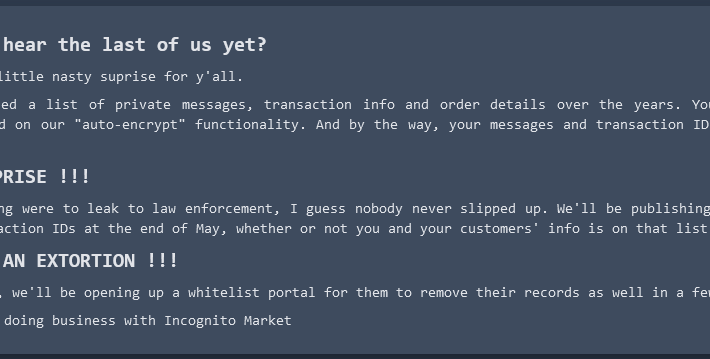
Incognito Darknet Market Mass-Extorts Buyers, Sellers – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Borrowing from the playbook of ransomware purveyors, the darknet narcotics bazaar Incognito Market has begun extorting all of its vendors and...
ANDROID PENTEST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Android Penetration Testing MOBSF FRAMEWORK
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Active Directory PenTesting Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Vulnerability Assessment & Penetration Testing (VAPT)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Sophisticated Vishing Campaigns Take World by Storm – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Mohd Izzuan Roslan via Alamy Stock Photo Voice phishing, or vishing, is having a moment right now,...
The Rise of AI Worms in Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shikha Dhingra The swift advancement of generative AI systems like OpenAI’s ChatGPT and Google’s Gemini has brought about a new era of...
CISA Lacks Staff with Skills Needed to Safeguard OT – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Governance & Risk Management , Information Sharing GAO Report Criticizes CISA’s Info Sharing Programs for Critical Infrastructure Prajeet...
Why Wiz Is Pursuing Its 2nd Massive Funding Round in 2 Years – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Security Operations Cloud Security Vendor Wiz Eyes Unprecedented $800M Funding Round at $10B+ Valuation Michael Novinson (MichaelNovinson) •...
Importance of Resilience in Mitigating Supply Chain Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Business Continuity Management / Disaster Recovery , Cybercrime Nitin Natarajan of CISA on Emerging Lessons From...
Dropbox Used in Latest Exploit for Phishing Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Anti-Phishing, DMARC , Fraud Management & Cybercrime , Social Engineering Darktrace Warns of Malware Hidden in PDF Stored in Dropbox Prajeet...
US Federal Budget Proposes $27.5B for Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybersecurity Spending , Government , Industry Specific Budget Proposes Incremental Increases, Not Leaps, But Small Budget Cut for CISA David Perera...
Tuta Mail adds new quantum-resistant encryption to protect email – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Tuta Mail has announced TutaCrypt, a new post-quantum encryption protocol to secure communications from powerful and anticipated decryption attacks. Tuta...
Microsoft says Windows 10 21H2 support is ending in June – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft announced today that it would end support for Windows 10 21H2 in June when the Enterprise and Education editions...
Okta says data leaked on hacking forum not from its systems – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Okta denies that its company data was leaked after a threat actor shared files allegedly stolen during an October 2023...
Researchers expose Microsoft SCCM misconfigs usable in cyberattacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ionut Ilascu Security researchers have created a knowledge base repository for attack and defense techniques based on improperly setting up Microsoft’s Configuration...
Equilend warns employees their data was stolen by ransomware gang – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan New York-based securities lending platform EquiLend Holdings confirmed in data breach notification letters sent to employees that their data was...
Over 15,000 hacked Roku accounts sold for 50¢ each to buy hardware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Roku has disclosed a data breach impacting over 15,000 customers after hacked accounts were used to make fraudulent purchases of...
Fake Leather wallet app on Apple App Store is a crypto drainer – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The developers of the Leather cryptocurrency wallet are warning of a fake app on the Apple App Store, with users...
Android Penetration Testing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Using LLMs to Unredact Text – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Flerfer • March 11, 2024 9:56 AM I’ve been wondering if this could be used to help decrypt...
OT Security Q&A for Cybersecurity Leaders with Difenda and Microsoft – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary Securing Operational Technology ACCESS THE RECORDING Kick-start your OT security program, wherever you are in your journey. Gain industry-specific insights into...
The Balancing Act for Mid-Market Firms: Navigating Digital Growth and Security Hurdles – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Kevin Beasley, CIO, VAI Increased competition and new regulatory requirements are increasing the tempo of digital transformation among mid-market...
The Ethics And Privacy Concerns Of Employee Monitoring: Insights From Data Privacy Expert Ken Cox – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Ken Cox, President of Hostirian Despite the technological advancements brought by automation and the enhanced capabilities of data analytics...
Phishing Campaign Exploits Open Redirection Vulnerability In ‘Indeed.com’ – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Brett Raybould, EMEA Solutions Architect, Menlo Security Phishing remains one of the most prevalent challenges facing organisations, with more...
Magnet Goblin Exploits Ivanti Vulnerabilities – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have uncovered a trend involving the exploitation of 1-day vulnerabilities, including two in Ivanti Connect Secure VPN. The flaws,...