Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Quality Stock via Alamy Stock Photo Researchers have developed a simple exploit capable of unlocking all of...
Patchless Apple M-Chip Vulnerability Allows Cryptography Bypass – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Ralf Liebhold via Shutterstock Apple last week quietly posted a workaround for a vulnerability in its M-series...
Threat Report: Examining the Use of AI in Attack Techniques – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security 4 Min Read Source: Tanapong Sungkaew via Alamy Stock Photo We are entering a new era of cybersecurity, driven in...
DHS Proposes Critical Infrastructure Reporting Rules – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: GK Images via Alamy Stock Photo The Department of Homeland Security today previewed a set...
Vietnam Securities Broker Suffers Cyberattack That Suspended Trading – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Janusz Pieńkowski via Alamy Stock Photo VNDirect, one of Vietnam’s largest brokerages, over the past...
‘Tycoon’ Malware Kit Bypasses Microsoft, Google MFA – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: hayaletsek via Alamy Stock Photo Threat actors are widely adopting an emerging adversary-in-the-middle (AitM) phishing kit sold...
Zero-Day Bonanza Drives More Exploits Against Enterprises – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Sondem via Alamy Stock Photo The escalating cybersecurity arms race between adversaries and enterprises is...
Organizations Are Shifting Ransomware Defense Tactics, But Malware Is Still the Problem – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Trevor Hilligoss, Senior Director of Security Research at SpyCloud Ransomware attacks are a fact of life – over 72% of global...
Open AI Exec Warns AI is “Extremely Addictive,” Humanity Could Become “Enslaved” – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Sai Mattapalli and Rohan Kalahasty, Co-Founders — Vytal.ai The idea of technology going wrong and turning on its creators...
World Backup Day 2024: safeguarding your digital ecosystem – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Data loss is a difficult business reality. Depending on the circumstances, data loss can even force businesses to shut...
Activision: Enable 2FA to secure accounts recently stolen by malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas An infostealer malware campaign has collected millions of logins from users of various gaming websites, including players that use cheats,...
Are You Affected by the Backdoor in XZ Utils? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 2 Min Read Source: MSRF via Alamy Stock Photo Red Hat is warning that a vulnerability in XZ Utils,...
CISO Corner: Cyber-Pro Swindle; New Faces of Risk; Cyber Boosts Valuation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Universal Images Group North America LLC via Alamy Stock Photo Welcome to CISO Corner,...
UN Peace Operations Under Fire From State-Sponsored Hackers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading 1 Min Read Source: Photonic via Alamy Stock Photo United Nations peacekeeping missions, especially in Africa,...
Lessons From the LockBit Takedown – Source: www.darkreading.com
Source: www.darkreading.com – Author: Aaron Walton 4 Min Read Source: Aleksei Gorodenkov via Alamy Stock Photo Like most operators out there, we really enjoyed last month’s...
Cloud Email Filtering Bypass Attack Works 80% of the Time – Source: www.darkreading.com
Source: www.darkreading.com – Author: David Strom 5 Min Read Source: Cultura Creative RF via Alamy Stock Photo Computer scientists have uncovered a shockingly prevalent misconfiguration in...
TheMoon Malware Rises Again with Malicious Botnet for Hire – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Design Pics Inc via Alamy Stock Photo After disappearing for several years, TheMoon has returned...
Checkmarx Announces Partnership With Wiz – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE PARAMUS, N.J.–(BUSINESS WIRE)– Checkmarx, the leader in cloud-native application security, has integrated its enterprise application security platform, Checkmarx One, with...
WiCyS and ISC2 Launch Spring Camp for Cybersecurity Certification – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE COOKEVILLE, Tenn., March 26, 2024/PRNewswire-PRWeb/ — In partnership with ISC2, the world’s leading nonprofit member organization for cybersecurity professionals, Women...
New Cyber Threats to Challenge Financial Services Sector in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE RESTON, Va., March 27, 2024 /PRNewswire/ — FS-ISAC, the member-driven, not-for-profit organization that advances cybersecurity and resilience in the global...
Getting rid of a 20+ year old known vulnerability: It’s like a PSA for Runtime Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Vaas, Senior Content Marketing Manager, Contrast Security On Wednesday, March 27, CISA and the FBI issued a cry for help: We...
‘Darcula’ PhaaS Campaign Sinks Fangs into Victims – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A sprawling phishing-as-a-service (PhaaS) campaign that has been running since at least last summer is using more than 20,000 fake...
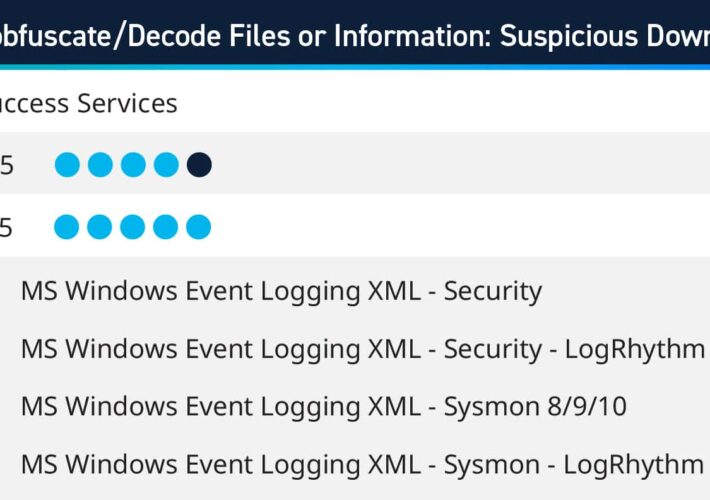
Q1 2024 Success Services Use Cases – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kelsey Gast As part of the Subscription Services team, LogRhythm consultants work with customers to help bolster their defenses against cyberthreats and...
Strengthening Security in Distributed Payment Systems: Exploring Innovative Solutions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nak Koh Building on our previous discussion about the pivotal role of Trusted Platform Modules (TPMs) in securing distributed ID and payment...
Market Forces vs. Regulation: How to Drive IT Product Safety – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Over the past 50 years, traveling in automobiles has become much safer. Part of this is due to government regulations...
Implications of AI for Corporate Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ontic Contributor Article By: Ontic Contributor | March 29, 2024 On February 29, I was honored to serve as the moderator for...
Guarding Education: The Impact of Compromised Credentials – Source: securityboulevard.com
Source: securityboulevard.com – Author: Enzoic In recent years, the education sector has increasingly become a target for cybercriminals seeking to exploit vulnerabilities and gain unauthorized access...
PyPI Goes Quiet After Huge Malware Attack: 500+ Typosquat Fakes Found – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings The Python Package Index was drowning in malicious code again, so they had to shut down registration for cleanup. More software supply-chain...
A(nother) Ransomware Saga with a Twist – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joao Correia The healthcare sector has once again found itself at the center of a storm. On February 21, Change Healthcare, a...
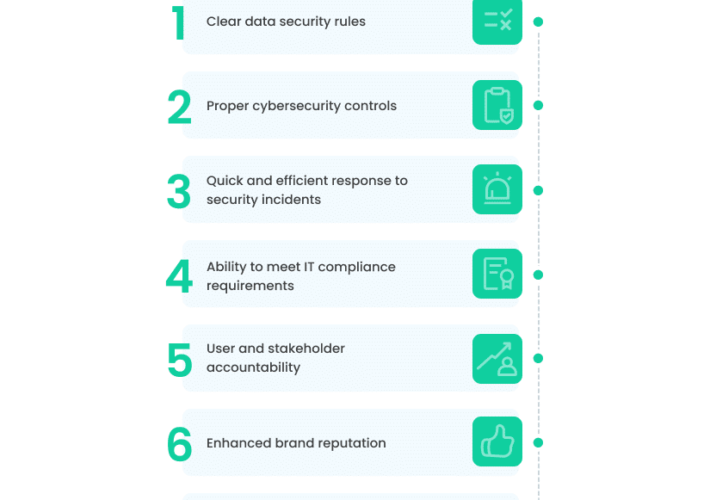
10 Must-Have Elements for an Air-Tight IT Security Policy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rom Carmel In 2023, data security faced an uphill battle against cyberattacks, and the risks of becoming a victim grew stronger. There...