Source: securityboulevard.com – Author: Michael Vizard An analysis of high-severity threats in 2023 detected by Barracuda Networks found that 66,000 incidents needed to be escalated to...
HHS: Health Care IT Helpdesks Under Attack in Voice Scams – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A beleaguered healthcare industry, already a top target of cybercriminals, is under attack again. Bad actors recently have been using...
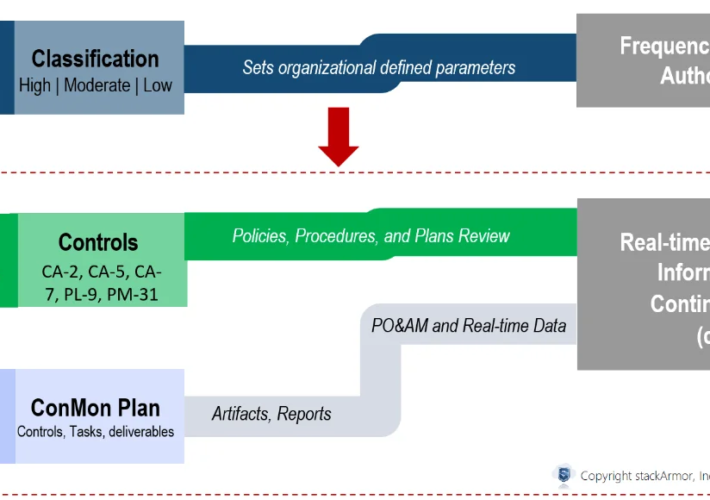
Continuous ATO: Going from Authority to Operate (ATO) to Ability to Respond – Source: securityboulevard.com
Source: securityboulevard.com – Author: stackArmor As agencies modernize and increasingly move critical business processes and data online especially using cloud computing services, Federal agencies and their...
Meta Will Label AI-Generated Content Starting In May – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Tech Giant Asks Creators to Declare Content with ‘Made with...
Hugging Face Vulnerabilities Highlight AI-as-a-Service Risks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Researchers Say Illegal Access to Private AI models Can Enable...
Live Webinar | The CISO’s Handbook: Blueprint for Navigating Identity Security & SAP Transformations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Jody Paterson Senior Director of Product, SailPoint The co-founder, CEO and Chairman of ERP Maestro, inc (The first cloud based SAP...
Open-Source Foundations Join Forces on Digital Supply Chain – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Governance & Risk Management Europe’s Cyber Resilience Act Pressures Open-Source Foundations and Manufacturers Akshaya Asokan (asokan_akshaya) , David...
US EPA Investigates Alleged Data Breach by Government Hacker – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Government , Incident & Breach Response , Industry Specific Hacker Claims to Leak Trove of Records Belonging to Environmental Protection Agency...
Vietnamese Cybercrime Group CoralRaider Nets Financial Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: incamerastock via Alamy Stock Photo A newcomer cybercrime group linked to Vietnam has targeted individuals and organizations...
Home Depot Hammered by Supply Chain Data Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading 1 Min Read Source: Ian Dagnall via Alamy Stock Photo A hacking forum leak has led...
Round 2: Change Healthcare Targeted in Second Ransomware Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 2 Min Read Source: Lenetstan via Shutterstock Change Healthcare reportedly is facing another attack, this time by ransomware gang...
Wyden Releases Draft Legislation to End Federal Dependence on Insecure, Proprietary Software – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Washington, D.C. – Following a new report about how shambolic cybersecurity practices by a federal technology contractor enabled a massive hack of the...
Software-Defined Vehicle Fleets Face a Twisty Road on Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Open Studio via Shutterstock When Israel-based REE Automotive designed its P7 electric vehicle chassis, it worked from...
The Fight for Cybersecurity Awareness – Source: www.darkreading.com
Source: www.darkreading.com – Author: Erik Gross 3 Min Read Source: Mopic via Alamy Stock Photo COMMENTARY The recent movie The Beekeeper begins with a cyberattack against a victim...
Scams exposed! The most deceptive tax season traps (2024) – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Cyber scammers love tax season. Emotions run high and it’s easy for scammers to prey on FUD (fear, uncertainty...
Best Practices Q&A: Guidance about what directors need to hear from CISOs — from a board member – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido CISOs can sometimes be their own worst enemy, especially when it comes to communicating with the board...
Critical RCE bug in 92,000 D-Link NAS devices now exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Image: Midjourney Attackers are now actively targeting over 92,000 end-of-life D-Link Network Attached Storage (NAS) devices exposed online and unpatched...
Google rolls out new Find My Device network to Android devices – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Image: Midjourney Google is rolling out an upgraded Find My Device network to Android devices in the United States and...
Hackers deploy crypto drainers on thousands of WordPress sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Almost 2,000 hacked WordPress sites now display fake NFT and discount pop-ups to trick visitors into connecting their wallets to...
Cyberattack on UK’s CVS Group disrupts veterinary operations – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas UK veterinary services provider CVS Group has announced that it suffered a cyberattack that disrupted IT services at its practices...
Notepad++ wants your help in “parasite website” shutdown – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma The Notepad++ project is seeking the public’s help in taking down a copycat website that closely impersonates Notepad++ but is not...
Security Vulnerability of HTML Emails – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier This is a newly discovered email vulnerability: The email your manager received and forwarded to you was something completely innocent,...
XZ Utils Supply Chain Attack: A Threat Actor Spent Two Years to Implement a Linux Backdoor – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cedric Pernet A threat actor quietly spent the last two years integrating themself in the core team of maintainers of XZ Utils,...
Australian IT Skills Shortage: 2024 Is The Year To Self-Upskill – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Matthew Sainsbury A recent series of reports and data point to one consistent theme: The skills crisis in the Australian IT industry...
What Is a VPN Kill Switch and Why Do You Need One? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Nicole Rennolds We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Zero Trust Access: The Transformative Blueprint for Achieving Regulatory Compliance – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Ironclad compliance through the Zero Trust innovation mindset By Roy Kikuchi, Director of Strategic Alliances at Safous, Internet Initiative Japan...
The Quantum Shift – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Preparing Cybersecurity for a New Era By Sercan Okur, VP of Technology, NextRay In contrast to my previous pieces, I...
CISO Life: the Good, the Bad, the Ugly – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary What type of things can go wrong with Senior Leadership, the Org, Legal, HR, etc. by Dan K. Anderson In today’s...
The Pitfalls of Periodic Penetration Testing & What to Do Instead – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Periodic penetration testing approaches can be likened to regular tire inspections for vehicles. While they provide valuable insights into the...
US Federal Data Privacy Law Introduced by Legislators – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A bipartisan US federal data protection law has been drafted by two US lawmakers, aiming to codify and enforce privacy rights...