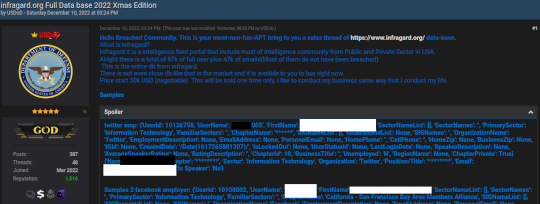
Source: krebsonsecurity.com – Author: BrianKrebs Brazilian authorities reportedly have arrested a 33-year-old man on suspicion of being “USDoD,” a prolific cybercriminal who rose to infamy in...
Get an Untrusted Security Advisor! Have Fun, Reduce Fail! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anton Chuvakin Many organizations are looking for trusted advisors, and this applies to our beloved domain of cyber/information security. If you look...
Is End-User Cybersecurity Training Useless? Spoiler Alert: It’s Not! – Source: securityboulevard.com
Source: securityboulevard.com – Author: hmeyers Chris Clements, VP of Solutions Architecture October 18, 2024 Because of the frequency of phishing attacks landing in user mailboxes and...
USENIX NSDI ’24 – MESSI: Behavioral Testing of BGP Implementations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Rathin Singha, Rajdeep Mondal, Ryan Beckett, Siva Kesava Reddy Kakarla, Todd Millstein, George Varghese Our sincere thanks to USENIX, and...
AI-Generated Personas: Trust and Deception – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Michael Berry And the Ethical Dilemma of Using AI to Create Fake Online Personalities In recent years, advancements in artificial intelligence...
Daniel Stori’s Turnoff.US: ‘bash-gptl’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored...
USENIX NSDI ’24 – Netcastle: Network Infrastructure Testing At Scale – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters:Rob Sherwood, Jinghao Shi, Ying Zhang, Neil Spring, Srikanth Sundaresan, Jasmeet Bagga, Prathyusha Peddi, Vineela Kukkadapu, Rashmi Shrivastava, Manikantan KR,...
The transformation of open source: Lessons from the past decade – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens Over the past decade, the world of open source software has undergone a seismic transformation, both in terms of its...
Celebrating Excellence in Financial Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Thomas Stoesser Like most businesses, banks are facing a highly competitive future built on digital services. To succeed, they must modernize their...
Army Cloud Program to Help SMBs Meet DoD Cyber Requirements – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The U.S. Army is building a secure cloud environment that small businesses can use to meet increasingly stringent military cybersecurity...
Cybersecurity Snapshot: Tenable Report Warns About Toxic Cloud Exposures, as PwC Study Urges C-Suite Collaboration for Stronger Cyber Resilience – Source: securityboulevard.com
Source: securityboulevard.com – Author: Juan Perez Check out invaluable cloud security insights and recommendations from the “Tenable Cloud Risk Report 2024.” Plus, a PwC study says...
AI-Powered Fraud Detection Systems for Enhanced Cybersecurity – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Artificial intelligence (AI) has many applications in cybersecurity. Automated fraud detection is one of the most impactful of these use...
From Raw Data to Rough Drafts: The Entrepreneurial Journey of Two Engineers-Turned-Bestselling Authors
As part of the Entrepreneurs AG’s spotlight month, read more about the intersection of engineering and authorship. Views: 1
Friday Squid Blogging: Squid Scarf – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Justice Department Indicts Tech CEO for Falsifying Security Certifications – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog The Wall Street Journal is reporting that the CEO of a still unnamed company has been indicted for creating...
MEDUZASTEALER Detection: Hackers Distribute Malware Masquerading the Sender as Reserve+ Technical Support via Telegram Messaging Service – Source: socprime.com
Source: socprime.com – Author: Veronika Telychko Hard on the heels of a new wave of cyber-attacks by UAC-0050 involving cyber espionage and financial thefts and relying...
Microsoft: macOS Vulnerability Potentially Exploited in Adware Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Microsoft on Thursday warned of a recently patched macOS vulnerability potentially being exploited in adware attacks. The issue, tracked as...
In Other News: China Making Big Claims, ConfusedPilot AI Attack, Microsoft Security Log Issues – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s cybersecurity news roundup provides a concise compilation of noteworthy stories that might have slipped under the radar. We provide...
North Korean APT Exploited IE Zero-Day in Supply Chain Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A North Korean threat actor has exploited a recent Internet Explorer zero-day vulnerability in a supply chain attack, threat intelligence...
Rising Tides: Christien “DilDog” Rioux on Building Privacy and What Makes Hackers Unique – Source: www.securityweek.com
Source: www.securityweek.com – Author: Jennifer Leggio Few things bring me more joy than this ongoing Rising Tides column, because I get to dig into the minds...
North Korean Fake IT Workers Extort Employers After Stealing Data – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Hundreds of companies in the US, UK, and Australia have fallen victim to the North Korean fake IT worker schemes,...
Organizations Faster at Detecting OT Incidents, but Response Still Lacking: Report – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Organizations have been getting faster at detecting incidents in industrial control system (ICS) and other operational technology (OT) environments, but...
Alabama Man Arrested in SEC Social Media Account Hack That Led the Price of Bitcoin to Spike – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press An Alabama man was arrested Thursday for his alleged role in the January hack of a U.S. Securities and Exchange...
Omni Family Health Data Breach Impacts 470,000 Individuals – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire California network of health centers Omni Family Health is notifying close to 470,000 individuals that their personal information was stolen...
Time to Get Strict With DMARC – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: TierneyMJ via Shutterstock The state of DMARC email authentication and security standard looked so promising at the...
ESET-Branded Wiper Attack Targets Israel; Firm Denies Compromise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: David R. Frazier Photolibrary via Alamy Stock Photo Security firm ESET is refuting reports...
CISOs: Throwing Cash at Tools Isn’t Helping Detect Breaches – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Kjetil Kolbjørnsrud via Alamy Stock Photo Global information security spend is projected to reach $215...
Vulnerabilities, AI Compete for Software Developers’ Attention – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Gorodenkoff via Shutterstock Less than two years after the general release of ChatGPT, most software developers have...
Supply Chain Cybersecurity Beyond Traditional Vendor Risk Management – Source: www.darkreading.com
Source: www.darkreading.com – Author: Malleswar Reddy Yerabolu Malleswar Reddy Yerabolu, Senior Security Engineer, North Carolina Department of Health and Human Services October 18, 2024 5 Min...
Anonymous Sudan Unmasked as Leader Faces Life in Prison – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Firoze Edassery via Alamy Stock Photo A federal grand jury has indicted two Sudanese nationals for their...