Source: www.govinfosecurity.com – Author: 3rd Party Risk Management , Finance & Banking , Governance & Risk Management Presented by Bitsight 60 Minutes ...
Unforeseen Risks to Medical Devices in Ransomware Attacks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: While ransomware attacks against medical devices don’t happen often, disruptive cyber incidents that affect the availability of the IT systems that medical...
The 3 Questions at the Core of Every Cybersecurity Compliance Mandate – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Cybersecurity compliance is undergoing a massive shift, with regulatory frameworks rapidly introducing more complex rules, stricter enforcement, and tougher penalties...
5 Security Considerations for Managing AI Agents and Their Identities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Apurva Dave The explosion of AI agents and large language models (LLMs) is reshaping how we think about automation, decision-making, and technology...
White House Memo Puts the Focus of AI on National Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The Biden Administration today is issuing broad orders for leveraging AI for U.S. national security, directing the government to ensure...
How is AI Used in Cybersecurity? 7 AI Use Cases – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Irwin What are AI Use Cases? AI use cases refer to specific applications of artificial intelligence designed to solve cybersecurity challenges...
DEF CON 32 – AppSec Village – Defeating Secure Code Review GPT Hallucinations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Thursday, October 24, 2024 Home » Security Bloggers Network » DEF CON 32 – AppSec Village – Defeating Secure Code...
How we managed Aurora Serverless V2 Idle connections in RDS Proxy and saved RDS costs by 50% – Source: securityboulevard.com
Source: securityboulevard.com – Author: strobes Introduction In a recent migration from a standard RDS DB instance to Aurora RDS PostgreSQL Serverless V2, we encountered an unexpected...
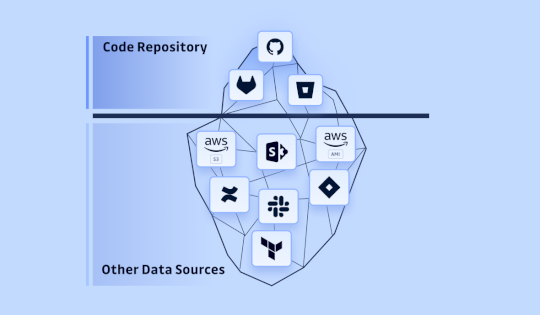
The extent of Hardcoded Secrets: From Development to Production – Source: securityboulevard.com
Source: securityboulevard.com – Author: Guillaume Valadon Secrets leaks aren’t confined to the developer’s domain; they seep into infrastructure like Terraform files, build automation tools through logs...
Blackwire Labs AI Cybersecurity Platform Incorporates Blockchain to Validate Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Blackwire Labs launched a platform that combines generative artificial intelligence (AI) with blockchain technologies to provide cybersecurity teams with recommendations...
Randall Munroe’s XKCD ‘RNAWorld’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
DEF CON 32 – AppSec Village – Securing Frontends at Scale;Paving our Way to Post XSS World – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – AppSec Village – Securing Frontends at Scale;Paving our Way to...
Embracing Innovation: Seceon’s Journey at GITEX 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kriti Tripathi As businesses navigate an increasingly digital landscape, leveraging advanced technologies has become essential. At GITEX 2024, Seceon proudly showcased its...
Announcing the SWENext 2024 Annual Award Recipients
Congratulations to the SWENexters who received a 2024 SWENext Annual Award! Views: 1
CISOs have to get on top of AI technologies, warns Microsoft – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 24 Oct 20249 mins CSO and CISOGenerative AI Digital Defense Report notes the depth at which threat actors are already using...
Sophos to acquire rival Secureworks in $859 million deal – Source: www.csoonline.com
Source: www.csoonline.com – Author: Editor in Chief B2B COMPUTERWOCHE, CIO, CSO in Germany News 24 Oct 20243 mins Mergers and AcquisitionsSecurityTechnology Industry The companies’ executives position...
Globale und regionale Unterschiede in Cyber-Strategien – Source: www.csoonline.com
Source: www.csoonline.com – Author: Eine aktuelle Studie zeigt, dass Cyber Security weltweit zunehmend als werttreibender Faktor betrachtet wird, der die technologische und geschäftliche Transformation maßgeblich beeinflusst....
Ransomware-Attacke auf Medienhaus IDEA – Source: www.csoonline.com
Source: www.csoonline.com – Author: Hacker haben sich Zugriff auf die IT-Systeme des Medienunternehmens IDEA verschafft. NicoElNino – Shutterstock.com Nach eigenen Angaben stellte das Medienunternehmen IDEA am...
Critical Fortinet vulnerability finds zero-day RCE exploits – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 24 Oct 20243 mins Security SoftwareZero-day vulnerability Threat actors exploited buggy FortiManager instances to extract the credentials of managed devices. Hackers...
Iranian hackers ramp up influence operations ahead of 2024 US election – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 24 Oct 20246 mins CyberattacksHacker GroupsSecurity Microsoft has warned about escalating cyber influence operations by Iran’s IRGC as election day approaches,...
The ransomware negotiation playbook adds new chapters – Source: www.csoonline.com
Source: www.csoonline.com – Author: Regulatory tangle has further complicated the fraught ransomware negotiation process, while new threats from increasingly unreliable attackers tactics leave organizations confronting difficult...
Diese Unternehmen hat’s schon erwischt – Source: www.csoonline.com
Source: www.csoonline.com – Author: Ransomware, Brute Force, DDoS und Co: Diese deutschen Unternehmen wurden in diesem Jahr bereits von Cyberkriminellen attackiert. Hier finden Sie aktuelle Cyberangriffe...
HackerOne Joins AWS Marketplace as Cloud Vulnerabilities Rise – Source:www.hackerone.com
Source: www.hackerone.com – Author: HackerOne. Addressing security risks at scale is more important than ever. With a global pandemic accelerating digital transformations, organizations are shipping new...
Cisco ASA, FTD Software Under Active VPN Exploitation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Palamarchuk via Shutterstock Cisco has rushed a patch for a brute-force denial-of-service (DoS) vulnerability in its VPN that’s...
AI Chatbots Ditch Guardrails After ‘Deceptive Delight’ Cocktail – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Brent Hofacker via Alamy Stock Photo An artificial intelligence (AI) jailbreak method that mixes...
Why Cybersecurity Acumen Matters in the C-Suite – Source: www.darkreading.com
Source: www.darkreading.com – Author: Erik Gaston Erik Gaston, CIO & Vice President of Global Executive Engagement, Tanium October 24, 2024 6 Min Read Source: Stephen Barnes/Business...
‘Prometei’ Botnet Spreads Its Cryptojacker Worldwide – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Artimages via Alamy Stock Photo An 8-year-old modular botnet is still kicking, spreading a cryptojacker and Web...
Codasip Donates Tools to Develop Memory-Safe Chips – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Mentor58 via Alamy Stock Photo German processor design company Codasip has donated its latest RISC-V software development kit...
What Is PCI Compliance? A Simple Guide for Businesses – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ian Agar You likely accept credit and debit card payments every day. But with so much sensitive data, you need robust protection...
Get Advanced Ad Blocking and Superior Data Privacy Tools for Just $11 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy Published October 24, 2024 We may earn from vendors via affiliate links or sponsorships. This might affect product placement on...