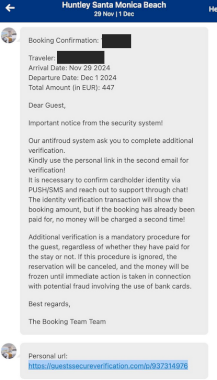
Source: krebsonsecurity.com – Author: BrianKrebs A number of cybercriminal innovations are making it easier for scammers to cash in on your upcoming travel plans. This story...
IoT Security Failures Can Be Sh*tty – Source: securityboulevard.com
Source: securityboulevard.com – Author: John Gallagher It’s hard not to see IoT security failures in the news because they can be dramatic, and this week was...
DEF CON 32 – Welcome to DEF CON 32 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » DEF CON 32 – Welcome to DEF CON 32 by Marc...
GreyNoise: AI’s Central Role in Detecting Security Flaws in IoT Devices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Threat researchers at cybersecurity firm GreyNoise Intelligence discovered two security vulnerabilities in live-streaming cameras used in such sectors as industrial...
October Recap: New AWS Sensitive Permissions and Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Karen Levy As AWS continues to evolve, new services and permissions are frequently introduced to enhance functionality and security. This blog provides...
Cybersecurity Vulnerability News: October 2024 CVE Roundup – Source: securityboulevard.com
Source: securityboulevard.com – Author: Security Insights Team Keep Your Organization Safe with Up-to-Date CVE Information Cybersecurity vulnerability warnings from the National Institute of Standards and Technology...
Stop Supply Chain Invaders – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland The post Stop Supply Chain Invaders appeared first on Eclypsium | Supply Chain Security for the Modern Enterprise. *** This...
Getting the Gist of CJIS – 5.9.5 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland What’s New in CJIS 5.9.5 as it Relates to Firmware Security? n the latest CJIS Security Policy, the FBI is...
Why Supply Chain Security Demands Focus on Hardware – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Supply chain security for servers, PCs, laptops, and devices has correctly focused on protecting these systems from vulnerabilities introduced through...
ATT&CK v16: Worry-Free Updates in Tidal Cyber – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tidal Cyber We are thrilled to share that we have migrated Tidal Cyber’s Community & Enterprise platforms to v16 of MITRE ATT&CK®...
Microsoft’s Controversial Recall Feature Release Delayed Again – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt It’s going to be at least another month or more before Microsoft’s much-debated Recall feature for new Copilot+ PCs is...
Chinese Hackers Use Quad7 Botnet for Credential Theft – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Security Operations Hackers Using Password Spraying to Steal User Microsoft Account Credentials Akshaya Asokan (asokan_akshaya) • November 1, 2024 Image:...
Everfox Deepens Cyber Case Management Expertise with Yakabod – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Governance & Risk Management , Incident & Breach Response , Insider Threat Yakabod Deal to Strengthen Everfox’s Insider Risk, Cyber Incident Response...
Doctor Hit With $500K HIPAA Fine: Feds Worse Than Hacker – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Fraud Management & Cybercrime , Healthcare , HIPAA/HITECH Plastic Surgeon Paid $53K Ransom But Says ‘the Real Criminal’ Is HHS Marianne Kolbasuk...
Unfolding the Complexity of the AI Supply Chain: Securing the Pipeline – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: AI-Driven Security Operations , The Future of AI & Cybersecurity Presented by Palo Alto Networks 60 minutes The...
Verizon’s Trusted Connection Boosts Mid-Market Cybersecurity – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Making the Case for Stronger Mid-Market Cybersecurity Beth Cohen • November 1, 2024 Image: Shutterstock In a small Northeastern U.S....
EmeraldWhale’s Massive Git Breach Highlights Config Gaps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Tithi Luadthong via Alamy Stock Photo Earlier this week, researchers uncovered a major cybercriminal operation,...
AU10TIX Q3 2024 Global Identity Fraud Report Detects Skyrocketing Social Media Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE LAS VEGAS, Oct. 30, 2024 /PRNewswire/ — MONEY 20/20 — AU10TIX, a global technology leader in identity verification and management, today released its Q3 2024...
SOFTSWISS Expands Bug Bounty Program – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE GZIRA, Malta, Oct. 30, 2024 /PRNewswire/ — SOFTSWISS, a leading software supplier in the iGaming industry, joins Cybersecurity Awareness Month. The company is enhancing...
Privacy Anxiety Pushes Microsoft Recall AI Release Again – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: GK Images via Alamy Stock Photo Microsoft has made the decision to once again delay...
Chinese APTs Cash In on Years of Edge Device Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Cinematic via Alamy Stock Photo Chinese threat actors are operating at a higher level today than ever...
Critical Auth Bugs Expose Smart Factory Gear to Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: frans lemmens via Alamy Stock Photo Critical security vulnerabilities affecting factory automation software from...
IT Security Centralization Makes the Use of Industrial Spies More Profitable – Source: www.darkreading.com
Source: www.darkreading.com – Author: Aybars Tuncdogan, Fulya Acikgoz Source: Cagkan Sayin via Alamy Stock Photo COMMENTARY In recent years, large-scale financial and reputational damages have taught organizations...
Taiwanese Facebook Biz Pages Fall to Infostealer Phishing Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Andrea Danti via Alamy Stock Photo An unknown threat actor is targeting Facebook businesses and advertising account users...
TechRepublic Premium Editorial Calendar: Policies, Hiring Kits, and Glossaries for Download – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Staff Payment Information Address Line 1 Address Line 2 (Optional) Country Your total Single Purchase Charges Select USD $99.00 USD $99.00...
‘CrossBarking’ Attack Targeted Secret APIs, Exposing Opera Browser Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Tierfotoagentur via Alamy Stock Photo Researchers have uncovered a fresh browser attack that compromises “private” application programming...
Hacktivity Disclosure for Private Programs – Source:www.hackerone.com
Source: www.hackerone.com – Author: Martijn Russchen. Disclosure is in the DNA of HackerOne. We call it Hacktivity and have supported public disclosure workflows of vulnerability reports...
Sophos Warns Chinese Hackers Are Becoming Stealthier – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Cybersecurity firm Sophos has detailed evolving tactics by Chinese advanced persistent threat (APT) groups following five years of collecting telemetry on campaigns...
CISA Warns of Critical Software Vulnerabilities in Industrial Devices – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: The US Cybersecurity and Infrastructure Security Agency (CISA) has urged manufacturing companies to apply mitigations after one Rockwell Automation and several Mitsubishi...
US and Israel Warn of Iranian Threat Actor’s New Tradecraft – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: The US and Israel have warned that the Iranian state-sponsored threat actor Cotton Sandstorm is deploying new tradecraft to target networks, including...