Learning on Coursera adds flexibility to the Berkeley Engineering experience. Views: 1
Affinity Group Spotlight: Military & Veterans
Each month throughout the year, we’ll be spotlighting a SWE Affinity Group. We are excited to highlight SWE’s Military & Veterans Affinity Group! Views: 1
SWE Diverse Podcast Ep 286: First-Generation Women Engineers Share Their Stories
In this podcast episode, first-generation engineers reflect on the complexities of navigating two cultures, the importance of building strong networks, and the unique strengths they bring...
Celebrating a Milestone – Over 1.5 Billion Daily Queries on Our IP to ASN Mapping Service – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rob Thomas A special message from Rob Thomas, CEO of Team Cymru, thanking our Community for their efforts and dedication to joining...
DEF CON 32 – Securing CCTV Cameras Against Blind Spots – Jacob Shams – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – Securing CCTV Cameras Against Blind Spots – Jacob Shams Authors/Presenters:...
Tips to Master Cybersecurity AI Prompt Engineering – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Irwin Have you ever wondered how to get the most from generative AI models built into your cybersecurity tools? While there...
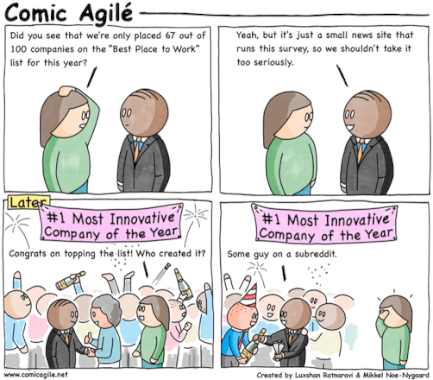
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #312 – Appraisal – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Friday, November 8, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
DEF CON 32 – Smishing Smackdown: Unraveling the Threads of USPS Smishing and Fighting Back – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Home » Security Bloggers Network » DEF CON 32 – Smishing Smackdown: Unraveling the Threads of USPS Smishing and Fighting...
Smart holiday shopping—How to safely secure deals and discounts for the hottest gifts – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog Home » Security Bloggers Network » Smart holiday shopping—How to safely secure deals and discounts for the hottest gifts Oh,...
AI Summit Vancouver 2024: Exploring AI’s Role, Risks, and Transformative Power – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dwayne McDaniel At one point in the not-too-distant past, the most exciting technology being explored throughout the world was steam power. People...
Clearing the Clutter: Simplifying Security Operations with Tool Consolidation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Tool redundancy within organizations presents significant challenges that impede operational efficiency and strategic cybersecurity responsiveness. When multiple tools with overlapping capabilities...
Cybersecurity Snapshot: CISA Warns of Global Spear-Phishing Threat, While OWASP Releases AI Security Resources – Source: securityboulevard.com
Source: securityboulevard.com – Author: Juan Perez CISA is warning about a spear-phishing campaign that spreads malicious RDP files. Plus, OWASP is offering guidance about deepfakes and...
Cybersecurity Insights with Contrast CISO David Lindner | 11/8/24 – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Lindner, Director, Application Security Insight #1: Time for a new SIEM? Make it ADR-compatible When evaluating modern security information and event...
US Gov Agency Urges Employees to Limit Phone Use After China ‘Salt Typhoon’ Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News The US government’s Consumer Financial Protection Bureau (CFPB) is directing employees to minimize the use of cellphones for work-related activities,...
In Other News: China Hacked Singtel, GuLoader Attacks on Industrial Firms, LastPass Phishing Campaign – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s cybersecurity news roundup provides a concise compilation of noteworthy stories that might have slipped under the radar. We provide...
Malwarebytes Acquires VPN Provider AzireVPN – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cybersecurity firm Malwarebytes on Thursday announced the acquisition of AzireVPN, a Swedish company that sells privacy-focused VPN services. Financial terms...
Unpatched Vulnerabilities Allow Hacking of Mazda Cars: ZDI – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Vulnerabilities in the infotainment system of multiple Mazda car models could allow attackers to execute arbitrary code with root privileges,...
Nokia Says Impact of Recent Source Code Leak Is Very Limited – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Nokia says the impact of the recent data leak is very limited, and there is no indication that the cybersecurity...
US Prison Sentences for Nigerian Cybercriminals Surge in Recent Months – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A significant number of Nigerian cybercriminals have been sent to prison in recent months in the United States, and some...
Texas Oilfield Supplier Newpark Hit by Ransomware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Newpark Resources this week announced that access to certain information systems and business applications has been disrupted following a ransomware...
HPE Patches Critical Vulnerabilities in Aruba Access Points – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire HPE this week announced patches for multiple vulnerabilities in its Aruba Networking access points, including two critical-severity command injection bugs....
Innovator Spotlight: Push Security – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin Identity is the new perimeter. Attackers are no longer hacking into your organization—they’re logging in with compromised credentials. Push Security is...
How to maximize cybersecurity ROI – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Cost savings and business benefits were quantified in “The Total Economic Impact of Cynet All-in-One Security,” a commissioned study conducted...
The AT&T Phone Records Stolen – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team In today’s digital age, the importance of cybersecurity must be re-balanced. With increasing cyberattacks and data breaches, organizations must prioritize...
CISA Warns of Active Attacks on Critical Palo Alto Exploit – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: CISA Adds Critical Palo Alto Flaw to Vulnerability Catalog After Attack Discovery Chris Riotta (@chrisriotta) • November 8, 2024 Palo...
Entrust Will Stop Operating As Trusted Certificate Authority – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Encryption & Key Management , Security Operations Google Designates Entrust ‘Untrustworthy’ After Years of ‘Concerning Behaviors’ Mathew J. Schwartz (euroinfosec) • November...
Cyderes’ New CEO Eyes Identity-Cybersecurity Convergence – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Artificial Intelligence & Machine Learning , Identity & Access Management , Next-Generation Technologies & Secure Development CEO Chris Schueler Aims to Combine...
Webinar | Prisma Access Browser: Boosting Security for Browser-Based Work – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: The Future of AI & Cybersecurity Presented by Palo Alto Networks 60 minutes The browser is today’s workspace....
Preparing for DORA Amid Technical Controls Ambiguity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Martin Greenfield Source: Sikov via Adobe Stock Photo COMMENTARY January 2025 is a big month for the finance industry – and the...
How Developers Drive Security Professionals Crazy – Source: www.darkreading.com
Source: www.darkreading.com – Author: Debrup Ghosh Debrup Ghosh, Principal Product Manager, F5 Inc. November 8, 2024 4 Min Read Source: Maskot via Alamy Stock Photo COMMENTARY...