Source: www.csoonline.com – Author: Feature 14 Nov 20247 mins CyberattacksData and Information SecuritySecurity Practices Preventing, investigating, and cleaning up after potentially dangerous AiTM attacks requires a...
Citrix admins advised to install hotfixes to block vulnerabilities – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 13 Nov 20246 mins Threat and Vulnerability ManagementVulnerabilities The holes could allow an authenticated hacker to use HTTP to get into...
November 2024 Patch Tuesday patches four zero days and three critical flaws – Source: www.csoonline.com
Source: www.csoonline.com – Author: News 13 Nov 20244 mins VulnerabilitiesZero-day vulnerability And a stream of NTLM vulnerabilities continues to bite admins. After hitting users with five...
Amazon bestätigt Datenklau – Source: www.csoonline.com
Source: www.csoonline.com – Author: Amazon ist von einem Datenleck betroffen. Hintergrund ist eine Sicherheitslücke bei einem Drittanbieter. bluestork – Shutterstock.com Anfang November meldete ein Cyberkrimineller unter...
Volt Typhoon returns with fresh botnet attacks on critical US infrastructure – Source: www.csoonline.com
Source: www.csoonline.com – Author: Researchers reveal the resurgence of Volt Typhoon, exploiting outdated edge devices to infiltrate essential networks in government and industry. Volt Typhoon, a...
BSI-Lagebericht: Hacker werden immer professioneller und aggressiver – Source: www.csoonline.com
Source: www.csoonline.com – Author: Editor in Chief B2B COMPUTERWOCHE, CIO, CSO in Germany News 13 November 20244 Minuten Artificial Intelligence Hundertausende neue Schadcode-Varianten sind in den...
The Weight of Responsibility: The Obligation of a First-Generation College Graduate to Uplift Others
Each month throughout the year, we spotlight a different SWE Affinity Group. In this post from the First-Generation Students and Professionals AG, Mariel Cisneros reflects on...
Top Bot Attack Predictions for Holiday Sales 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maddy Lewis Kasada’s 2023 Holiday Bot Report offered a clear view of how bots disrupted eCommerce and online sales last season. Looking...
DEF CON 32 – Splitting The Email Atom Exploiting Parsers To Bypass Access Controls – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, November 13, 2024 Home » Security Bloggers Network » DEF CON 32 – Splitting The Email Atom Exploiting Parsers...
Sonatype recognized as a leader in SCA software in Forrester Wave – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens We are thrilled to announce that The Forrester Wave™: Software Composition Analysis Software, Q4 2024 recently named Sonatype a leader...
Response to CISA Advisory (AA24-317A): 2023 Top Routinely Exploited Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Francis Guibernau On November 12, 2024, the U.S. Cybersecurity & Infrastructure Security Agency (CISA) released a Cybersecurity Advisory (CSA) providing details on...
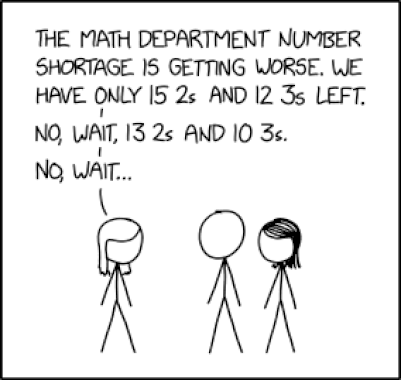
Randall Munroe’s XKCD ‘Number Shortage’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD *** This is a Security Bloggers Network...
Mend.io is a Strong Performer in the Forrester Wave™ Software Composition Analysis, Q4 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Haas It should be no surprise that the world runs on open source software. According to the latest Forrester Wave Software...
These 20 D-Link Devices Have Critical RCE Bug — but NO Patch NEVER – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Company doesn’t make storage devices now; has zero interest in fixing catastrophic vulnerability. D-Link NAS boxes are obsolete. Even the youngest...
PlatformEngineering.com: Strengthening Security in the Software Development Lifecycle – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alan Shimel The Techstrong Group is thrilled to announce the launch of PlatformEngineering.com, a new platform dedicated to advancing the platform engineering...
PKI and CLM Insights from 2024: Preparing for a Cyber Resilient 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Krupa Patil As the year winds down, it’s the perfect time to pause for retrospection. 2024 has been both exciting and challenging...
Toolkit Vastly Expands APT41’s Surveillance Powers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: u3d via Shutterstock China’s APT41 threat group is using a sophisticated Windows-based surveillance toolkit in a cyber-espionage...
Lacoste First to Use AI-Powered Anti-counterfeiting Solution – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE (Paris, France) – October 31, 2024 – As counterfeiting represents a global issue for brands and societies alike, Cypheme, a pioneering...
Zero-Days Win the Prize for Most Exploited Vulns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: JUN LI via Alamy Stock Photo The Cybersecurity and Infrastructure Security Agency is warning that the most routinely...
CISA Releases Its First Ever International Strategic Plan – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WASHINGTON – Today, the Cybersecurity and Infrastructure Security Agency (CISA) released its 2025–2026 International Strategic Plan, the agency’s first, which supports the...
20% of Industrial Manufacturers Are Using Network Security as a First Line of Defense – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK, Oct. 30, 2024 /PRNewswire/ — Industrial manufacturers ranked network security as their top cybersecurity investment to guard against adverse cyber...
5 Ways to Save Your Organization From Cloud Security Threats – Source: www.darkreading.com
Source: www.darkreading.com – Author: Manikandan Thangaraj Source: Zoonar GmbH via Alamy Stock Photo COMMENTARY The network structure of organizations has drastically changed post-pandemic with the adoption...
Iranian Cybercriminals Target Aerospace Workers via LinkedIn – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Iain Masterton via Alamy Stock Photo A phishing campaign, active since last September, is targeting users on LinkedIn...
Google AI Platform Bugs Leak Proprietary Enterprise LLMs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Krot Studio via Alamy Stock Photo Google has fixed two flaws in Vertex AI, its platform for...
How CISOs Can Lead the Responsible AI Charge – Source: www.darkreading.com
Source: www.darkreading.com – Author: Lucas Moody Lucas Moody, Chief Information Security Officer, Alteryx November 13, 2024 4 Min Read Source: Andreas Prott via Alamy Stock Photo...
New Essay Competition Explores AI’s Role in Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Edge Editors Source: Deco via Alamy Stock Photo The Munich Security Conference is partnering with the European Cyber Conflict Research Initiative’s Binding...
Smashing Security podcast #393: Who needs a laptop to hack when you have a Firestick? – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content Arion Kurtaj, a teenager from the UK, amassed a fortune through audacious cybercrimes. From stealing Grand Theft...
Citrix Patches Zero-Day Recording Manager Bugs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: JHVEPhoto via Shutterstock Very swiftly after disclosing them, Citrix has issued patches for two vulnerabilities in its...
Patch Tuesday: Four Critical Vulnerabilities Paved Over – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse On Patch Tuesday, Windows systems will be updated with a flood of security fixes. In November, Windows patched four zero-day...
Google Cloud to Assign CVEs to Critical Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Google Cloud announced on Tuesday that moving forward it will assign CVE identifiers to critical vulnerabilities found in its products,...