Source: www.darkreading.com – Author: Stephen Lawton Source: ArtemisDiana via Alamy Stock Photo Shortening the life cycle of Transport Layer Security (TLS) certificates can significantly reduce the...
Analyzing Tokenizer Part 2: Omen + Tokenizer – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Weir “I have not failed. I’ve just found 10,000 ways that won’t work” – Thomas Edison Introduction: This is a continuation of...
Why Robust API Security is a Must for Your Business – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn How Does API Security Influence Cybersecurity? As a seasoned data management expert and cybersecurity specialist, I’ve witnessed firsthand the significant...
Preventing Data Breaches with Advanced IAM Strategies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why Are IAM Strategies Strategic to Data Breach Prevention? IAM strategies, or Identity Access Management strategies, prioritize the control and...
National Public Data Shuts Down Months After Massive Breach – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt National Public Data, the data broker that filed for bankruptcy protection after a breach of its systems exposed 2.9 billion...
DEF CON 32 – The Way To Android Root: Exploiting Smartphone GPU – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Thursday, December 5, 2024 Home » Security Bloggers Network » DEF CON 32 – The Way To Android Root: Exploiting...
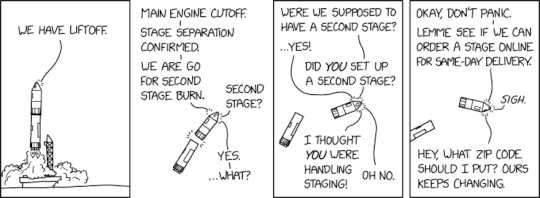
Randall Munroe’s XKCD ‘Second Stage’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
SaaS Security Outlook for 2025 | Grip Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Grip Security Blog The SaaS security landscape is shifting faster than ever, and with it comes a cascade of challenges. Shadow SaaS,...
China is Still Inside US Networks — It’s Been SIX Months – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings FBI and NSA recommend you use strong encryption. Chinese APT actors breached several large telcos in the spring (possibly earlier). And...
SonarQube Server 10.8 Release Announcement – Source: securityboulevard.com
Source: securityboulevard.com – Author: Robert Curlee In the 10.8 release of SonarQube Server, you’ll find these new and exciting capabilities: Use your own quality gate for...
DEF CON 32 – Atomic Honeypot – A MySQL Honeypot That Drops Shells – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, December 4, 2024 Home » Security Bloggers Network » DEF CON 32 – Atomic Honeypot – A MySQL Honeypot...
Are Long-Lived Credentials the New Achilles’ Heel for Cloud Security? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ben Abbott The head of security advocacy at Datadog, a cloud-based monitoring and analytics platform, has urged enterprises in Australia and the...
CISA, FBI Issue Guidance for Securing Communications Infrastructure – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse On Dec. 3, the Federal Bureau of Investigation, the Cybersecurity and Infrastructure Security Agency, and international partners issued guidance on...
Veeam Warns of Critical Vulnerability in Service Provider Console – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Backup, recovery, and data protection firm Veeam has released patches for two vulnerabilities in Veeam Service Provider Console, including a...
Spy v Spy: Russian APT Turla Caught Stealing From Pakistani APT – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine In an extraordinary case of digital espionage, Russian hackers spent nearly two years secretly controlling the computer systems of Pakistani...
Largest German Crime Marketplace Taken Down, Administrator Arrested – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Authorities in Germany on Tuesday announced the takedown of Crimenetwork, which they describe as the largest German-speaking online marketplace for...
Tuskira Scores $28.5M for AI-Powered Security Mesh – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Tuskira, a cybersecurity startup with ambitious plans to use artificial intelligence to unify and enhance threat defense systems, has launched...
CISA Warns of Zyxel Firewall Vulnerability Exploited in Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US cybersecurity agency CISA on Tuesday warned that a path traversal vulnerability in multiple Zyxel firewall appliances has been...
Government Guidance on Chinese Telco Hacking Highlights Threat to Cisco Devices – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Government agencies in the US, Canada, Australia and New Zealand have issued joint guidance for improving the security of communications...
Virtual Event Today: Cyber AI & Automation Summit – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s Cyber AI & Automation Summit will take place today, December 4th, as a fully immersive online experience. Sessions will...
Spotting the Charlatans: Red Flags for Enterprise Security Teams – Source: www.securityweek.com
Source: www.securityweek.com – Author: Joshua Goldfarb Most of the security professionals I’ve worked with over the course of my career have been sincere, talented, constructive players....
U.S. Offered $10M for Hacker Just Arrested by Russia – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs In January 2022, KrebsOnSecurity identified a Russian man named Mikhail Matveev as “Wazawaka,” a cybercriminal who was deeply involved in the...
H1-702 Las Vegas Day 0: Setup – Source:www.hackerone.com
Source: www.hackerone.com – Author: jesse@hackerone.com. Let’s take a glimpse of what we see before our hackers show for Live Hacking Events! Hackers! We have made it...
Police Shutter Largest German-Speaking Criminal Marketplace – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Cybercrime , Fraud Management & Cybercrime Crimenetwork Served as a Platform for Illegal Goods and Services Akshaya Asokan (asokan_akshaya) • December 4,...
Bug Bounties: Bringing Hackers and Manufacturers Together – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Endpoint Security , Governance & Risk Management , Internet of Things Security Researcher Lennert Wouters on Benefits of Device Hacking Contests, Collaboration...
Regulator Accuses AI Video Firm of Deceptive Marketing – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Artificial Intelligence & Machine Learning , Government , Industry Specific IntelliVision Settles With Federal Trade Commission Over Facial Recognition Claims Mathew J....
‘Horns&Hooves’ Malware Campaign Hits Over 1,000 Victims – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Cybercrime , Fraud Management & Cybercrime Russian Threat Actor Delivers NetSupport RAT, BurnsRAT via Fake Requests Prajeet Nair (@prajeetspeaks) • December 3,...
OnDemand | How to Build Cyber Resilience with Proactive Incident Response Strategies – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: Our website uses cookies. Cookies enable us to provide the best experience possible and help us understand how visitors use our website....
Ransomware-hit vodka maker Stoli files for bankruptcy in the United States – Source: www.exponential-e.com
Source: www.exponential-e.com – Author: Graham Cluley Stoli Group USA, the US subsidiary of vodka maker Stoli, has filed for bankruptcy – and a ransomware attack is...
Tech support scams leverage Google ads again and again, fleecing unsuspecting internet users – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley It’s not a new technique, but that doesn’t mean that cybercriminals cannot make rich rewards from SEO poisoning. SEO poisoning...