Source: www.techrepublic.com – Author: Guest Contributor The cybersecurity landscape in 2024 was marked by unprecedented challenges, significant breaches, and evolving regulatory requirements that fundamentally reshaped how...
Best Patch Management Software (2025): Compare Features & Pricing – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Nicole Rennolds We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Beware Of Shadow AI – Shadow IT’s Less Well-Known Brother – Source: www.securityweek.com
Source: www.securityweek.com – Author: Etay Maor Shadow IT is a fairly well-known problem in the cybersecurity industry. It’s where employees use unsanctioned systems and software as...
5.6 Million Impacted by Ransomware Attack on Healthcare Giant Ascension – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Ascension Health is notifying roughly 5.6 million individuals that their personal, medical, and payment information was compromised in a ransomware...
Sophos Patches Critical Firewall Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Sophos has announced patches for a critical-severity vulnerability in its firewall products that could allow remote attackers to execute arbitrary...
LockBit Ransomware Developer Arrested in Israel at Request of US – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Department of Justice has unsealed charges against a man with dual Russian and Israeli nationality accused of being...
Italy’s Privacy Watchdog Fines OpenAI for ChatGPT’s Violations in Collecting Users Personal Data – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Italy’s data protection watchdog said Friday it has fined OpenAI 15 million euros ($15.6 million) after wrapping up a probe...
Apple Complains Meta Requests Risk Privacy in Spat Over EU Efforts to Widen Access to iPhone Tech – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Apple complained that requests from Meta Platforms for access to its operating software threaten user privacy, in a spat fueled...
How SLED Organizations Can Enhance Cybersecurity Compliance Before Year-End – Source: securityboulevard.com
Source: securityboulevard.com – Author: Assura Team As the year comes to a close, State, Local, and Education (SLED) organizations must resharpen their focus on strengthening their...
Achieving Stability with Enhanced Secret Detection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Is the Quest for Stability an Uphill Battle in Cybersecurity? In the vast landscape of data management and cybersecurity, professionals...
DEF CON 32 – Disenshittify Or Die! How Hackers Can Seize The Means Of Computation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Monday, December 23, 2024 Home » Security Bloggers Network » DEF CON 32 – Disenshittify Or Die! How Hackers Can...
The Hidden Cost of Web Pixels – A Privacy and Security Nightmare – Source: securityboulevard.com
Source: securityboulevard.com – Author: mykola myroniuk Hey everyone, let’s talk about something we all encounter every day on the internet: web pixels. You might know them...
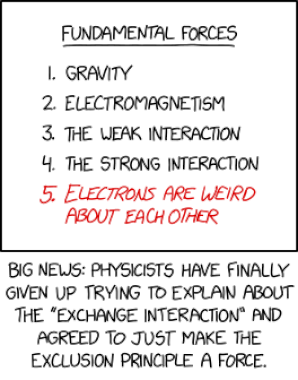
Randall Munroe’s XKCD ‘Exclusion Principle’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored by Marc Handelman. Read the original post...
DEF CON 32 – Hacker Jeopardy – Night 2 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Our sincere appreciation to DEF CON, and the Authors/Presenters for publishing their erudite DEF CON 32 content. Originating from the...
The Top 5 Kubernetes CVEs of 2024: Have You Patched Them Yet? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Stevie Caldwell Keeping up to date with critical vulnerabilities related to Kubernetes can be challenging for a variety of reasons. The biggest...
The Future of Growth: Getting Back to Basics in an AI-Powered World – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Remember the days when getting a sales call meant talking to an actual person who...
Peter Shor Broke PKI with Ancient Math, and Futuristic Quantum Computing – Source: securityboulevard.com
Source: securityboulevard.com – Author: Satyam Tyagi Peter Shor revolutionized public-key infrastructure (PKI) using concepts that trace back to 4,000-year-old Babylonian mathematics and culminated in futuristic quantum...
Health Care Data of Almost 1 Million ConnectOnCall User Exposed – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt A telehealth platform company used by health care firms to improve such operations as after-hours services is notifying more than...
Riot Games Surpasses 1,000 Valid Reports: Q&A – Source:www.hackerone.com
Source: www.hackerone.com – Author: johnk. At the end of 2018, Riot Games surpassed one of the biggest milestones of its bug bounty program to-date: 1,000 valid...
Non-Human Identities Gain Momentum, Requires Both Management, Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Don Tait Don Tait, Senior Analyst, Omdia December 23, 2024 4 Min Read COMMENTARY The growth in systems communicating over the internet...
How CISOs Can Communicate With Their Boards Effectively – Source: www.darkreading.com
Source: www.darkreading.com – Author: Harold Rivas Source: Stephen Barnes via Alamy Stock Photo COMMENTARY The role of the chief information security officer (CISO) today is not the...
Middle East Cyberwar Rages On, With No End in Sight – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: Skorzewiak via Alamy Stock Photo It’s been more than a year since the conflict between...
Name That Toon: Sneaking Around – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner Every person in this scene is just so joyful that we can’t help by wonder, what are they so happy...
Securing the OT Stage: NIS2, CRA, and IEC62443 Take Center Spotlight – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team In the dynamic landscape of Operational Technology (OT), robust cybersecurity measures are paramount. As the digital transformation accelerates, protecting critical...
Using Kafka as a Fast Correlation Engine – Source: socprime.com
Source: socprime.com – Author: Alex Verbniak In this article, we explore how Kafka Streams can be utilized for filtering and correlating events in real time, effectively...
Fluentd: How to Use a Parser With Regular Expression (regexp) – Source: socprime.com
Source: socprime.com – Author: Oleh P. WRITTEN BY Oleh P. SOC Engineer [post-views] December 23, 2024 · 3 min read This guide explains configuring Fluentd to...
Creating a Regex Pattern Set in AWS WAF – Source: socprime.com
Source: socprime.com – Author: Comrade H. WRITTEN BY Comrade H. WAF Engineer [post-views] December 23, 2024 · 3 min read AWS Web Application Firewall (WAF) is...
OpenSearch Flush, Translog, and Refresh – Source: socprime.com
Source: socprime.com – Author: Oleksii K. WRITTEN BY Oleksii K. DevOps Engineer [post-views] December 23, 2024 · 2 min read What Is OpenSearch Flush? In OpenSearch,...
Additional Settings for Optimizing Elasticsearch Cluster Performance – Source: socprime.com
Source: socprime.com – Author: Oleksandr L [post-views] December 23, 2024 · 2 min read When managing an Elasticsearch cluster, fine-tuning certain settings can enhance stability and...
Top 7 zero-day exploitation trends of 2024 – Source: www.csoonline.com
Source: www.csoonline.com – Author: Unpatched vulnerabilities are always critical means for compromising enterprise systems, but attacker activity around certain zero-day flaws indicate key trends cyber teams...