Source: www.cyberdefensemagazine.com – Author: News team Cybersecurity: how to involve people in risk mitigation Cefriel presented the white paper “Cyber Security and the Human Element”, an...
SWARM: Pioneering The Future of Autonomous Drone Operations and Electronic Warfare – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Modern unmanned technologies are experiencing rapid growth, encompassing both civilian and military applications. Autonomous vehicles, delivery drones, and unmanned aerial...
CVE-2024-55591 Detection: Critical Zero-Day Vulnerability in Fortinet FortiOS and FortiProxy Actively Exploited in the Wild – Source: socprime.com
Source: socprime.com – Author: Daryna Olyniychuk This week, over 700 new vulnerabilities have been identified, continuing the trend of rising security risks for organizations worldwide. Among...
Watch WE24’s Keynote Presentations and Q&A
At this year’s WE24 conference, we sat down with all three of the keynote speakers after their presentations for a quick Q&A. Source Views: 0
Smashing Security podcast #400: Hacker games, AI travel surveillance, and 25 years of IoT – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content The video game Path of Exile 2 suffers a security breach, we explore the issues of using...
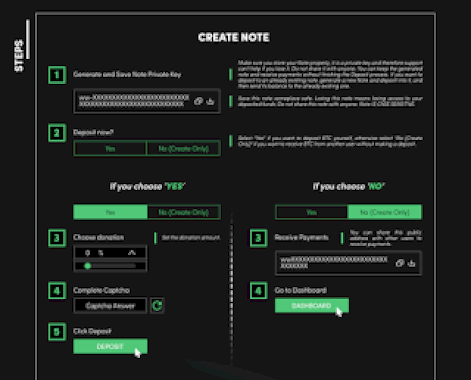
A Peek Inside the Current State of BitCoin Mixers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dancho Danchev Dear blog readers, In this post I’ll provide some actionable intelligence on the current state of active BitCoin Mixers landscape...
A Peek Inside the Current State of BitCoin Exchanges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dancho Danchev Dear blog readers, In this post I’ll provide some actionable intelligence on the current state of active BitCoin Exchanges landscape...
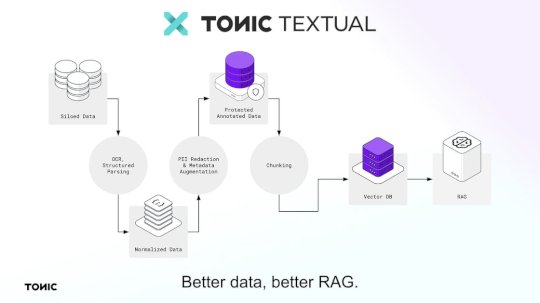
Test your apps with high-fidelity, production-like data with Release and Tonic – Source: securityboulevard.com
Source: securityboulevard.com – Author: Expert Insights on Synthetic Data from the Tonic.ai Blog Guest post: the following article was written by Release CTO and co-founder Erik Landerholm....
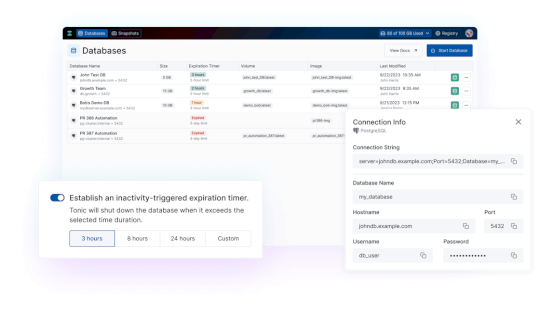
Tonic.ai product updates: July 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to share the latest updates and announcements designed to improve your...
Tonic.ai product updates: March 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to share the latest product updates and announcements designed to improve...
Tonic.ai product updates: February 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to share the latest product updates and announcements designed to improve...
Tonic.ai product updates: April 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Expert Insights on Synthetic Data from the Tonic.ai Blog We’re excited to share the latest updates and announcements designed to improve your...
DEF CON 32 – Signature-Based Detection Using Network Timing – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Thursday, January 16, 2025 Home » Security Bloggers Network » DEF CON 32 – Signature-Based Detection Using Network Timing Author/Presenter:...
Profiling a Currently Active Portfolio of High-Profile Cybercriminal Jabber and XMPP Accounts Including Email Address Accounts – Part Six – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dancho Danchev Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2025/01/profiling-a-currently-active-portfolio-of-high-profile-cybercriminal-jabber-and-xmpp-accounts-including-email-address-accounts-part-six/ Category & Tags: Security Bloggers Network –...
Dancho Danchev’s Testimony on “How Facebook Today’s Meta Failed To Protect Its Users and React To The Koobface Botnet And What We Should Do About It?” – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dancho Danchev Dear blog readers, This is Dancho. How to use this manual testimony? – Reference me Dancho Danchev – My web...
FBI Deletes PlugX Malware from Thousands of Computers – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier According to a DOJ press release, the FBI was able to delete the Chinese-used PlugX malware from “approximately 4,258 U.S.-based...
Biden’s Cybersecurity EO Leaves Trump a Comprehensive Blueprint for Defense – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: UPI via Alamy Stock Photo As President Biden prepares to hand over the government to...
183M Patient Records Exposed: Fortified Health Security Releases 2025 Healthcare Cybersecurity Report – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE BRENTWOOD, Tenn., Jan. 14, 2025 /PRNewswire/ — Fortified Health Security (Fortified), a Best in KLAS managed security services provider (MSSP) specializing in healthcare cybersecurity,...
Karl Triebes Joins Ivanti as Chief Product Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SALT LAKE CITY — January 13, 2025 — Ivanti, the software company that breaks down barriers between IT and security so...
CISA and US and International Partners Publish Guidance for OT Owners and Operators – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Today, CISA — along with U.S. and international partners — released joint guidance Secure by Demand: Priority Considerations for Operational Technology...
SEALSQ in Cooperation With WISeKey Expands Post-Quantum Footprint in Saudi Arabia – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Riyadh, Saudi Arabia, Jan. 13, 2025 (GLOBE NEWSWIRE) — SEALSQ Corp (NASDAQ: LAES) (“SEALSQ” or “Company”), a company specializing in...
FTC Orders GoDaddy to Fix Inadequate Security Practices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: M4OS Photos via Alamy Stock Photo NEWS BRIEF Having found GoDaddy’s security policies inadequate, the...
Strategic Approaches to Threat Detection, Investigation & Response – Source: www.darkreading.com
Source: www.darkreading.com – Author: Sameer Bhanushali The digital era has revolutionized how businesses operate, bringing unprecedented opportunities and challenges. Among the most pressing challenges are the...
Risk, Reputational Scores Enjoy Mixed Success as Security Tools – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: MMD Creative via Shutterstock As companies seek to improve their cybersecurity postures, they are increasingly using a...
Trusted Apps Sneak a Bug Into the UEFI Boot Process – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Ognyan Yosifov via Alamy Stock Photo A vulnerability in trusted system recovery programs could allow privileged attackers...
CISA’s AI Playbook Pushes For More Information Sharing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Edge Editors Source: Aleksey Funtap via Alamy Stock Photo NEWS BRIEF The U.S. Cybersecurity and Infrastructure Security Agency has released a new...
News alert: Aembit announces speakers for NHIcon event, highlighting non-human identity security – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire Silver Spring, MD, Jan. 15, 2025, CyberNewswire — Aembit, the non-human identity and access management (IAM) company, unveiled the full agenda...
News alert: Sweet Security’s LLM-powered detection engine reduces cloud noise to 0.04% – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire Tel Aviv, Israel, Jan. 15, 2025, CyberNewswire — Sweet Security, a leader in cloud runtime detection and response, today announced the...
News alert: Wultra secures €3M funding to help financial firms mitigate coming quantum threats – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cybernewswire Prague, Czech Republic, Jan. 15, 2025, CyberNewswire — Quantum computing is set to revolutionize technology, but it also presents a significant...