Each month throughout the year, we spotlight a SWE Affinity Group. We are excited to highlight the Technical Career Path AG. Source Views: 3
Say It Like a Civilian
The SWE Military and Veterans Affinity Group (MAVAG) shares five tips to help you communicate with your peers in a civilian workplace. Source Views: 1
SWE Diverse Podcast Ep 269: Building Legacies, Changing Lives: Donor Perspectives on SWE’s Endowed Scholarship Program
Hear the stories of how endowed scholarships leave a legacy for generations to come on this episode of Diverse: a SWE podcast. Source Views: 0
SWE Diverse Podcast Ep 267: Where STEM Meets Film: Bringing Engineering to the Screen
Hear from two women engineers who were featured in the IMAX film “Cities of the Future” in this episode of Diverse: a SWE podcast. Source Views:...
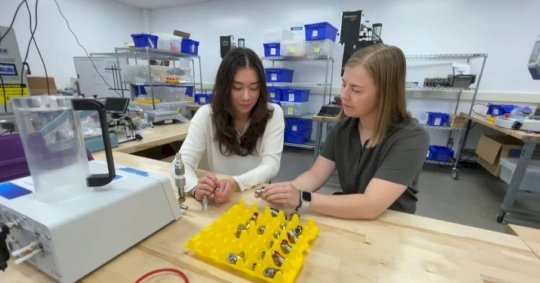
Empowering Innovation: How Dover Cultivates an Inclusive Culture and Champions Women Engineers
Two women engineers share what they enjoy about working at Dover, including the company’s emphasis on career growth and support for diversity, equity, and inclusion initiatives....
2024 WE Local Collegiate Competition Achievements
Congratulations to the recipients of the 2024 WE Local Collegiate Competition awards! Find their names and learn more about their research in this article. Source Views:...
SWE Global Ambassador Series: Meet Vandana Pandey
Hear from Vandana about her eight year journey as a SWE global ambassador, including her immense passion for getting involved and her innate desire to lead...
SWE@UCLA’s Passion for Public Policy
As part of the Public Policy Affinity Group’s spotlight, learn more about this collegiate section’s civic engagement events and SWE’s Lobbying Committee. Source Views: 1
US Military, Defense Contractors Infected with Infostealers: Hudson Rock – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Hundreds of computers in the U.S. Army and Navy and high-profile defense are infected with information-stealing malware that can lead...
PCI DSS 4: 6.4.3/11.6.1 – A Guide to SAQ A-EP Compliance using Feroot PaymentGuard AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: mykola myroniuk In this article Introduction: Payment Security Made Simple For SAQ A-EP merchants, securing payment pages requires sophisticated monitoring and compliance...
Randall Munroe’s XKCD ‘Hardwood’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic humor & dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Leveraging AI to Stay Ahead in Cybersecurity: A Conversation with Chandra Pandey and Joshua Skeens, CEO of Logically – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maggie MacAlpine At Seceon’s 2025 Q1 Innovation and Certification Days, Seceon CEO Chandra Pandey and Joshua Skeens, CEO of Seceon’s partner Logically...
DEF CON 32 – Manufacturing Lessons Learned, Lessons Taught – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Tuesday, February 18, 2025 Home » Security Bloggers Network » DEF CON 32 – Manufacturing Lessons Learned, Lessons Taught Authors/Presenters:...
Learn & Avoid Social Engineering Scams in 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kayla Kinney In the past decade, social engineering attacks have become more sophisticated and prevalent than ever. From AI voice impersonation to...
Intruder Enhances Free Vulnerability Intelligence Platform ‘Intel’ with AI-Generated CVE Descriptions – Source: securityboulevard.com
Source: securityboulevard.com – Author: cybernewswire Intel by Intruder now uses AI to contextualize NVD descriptions, helping security teams assess risk faster. Intruder, a leader in attack...
Cybersecurity in 2025: AI, Attack Surfaces and the Shift to Cyber Resilience – Source: securityboulevard.com
Source: securityboulevard.com – Author: Krista Case Hello, I’m Krista Case, research director on the team here at The Futurum Group. I’m here today to walk you...
Cybersecurity Predictions for 2025: Platforms, Convergence and the Future of Risk Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Fernando Montenegro Hello, I’m Fernando Montenegro and I recently joined Futurum Research as Vice President and Practice Lead for Cybersecurity Research. You...
Pangea Launches AI Guard and Prompt Guard to Combat Gen-AI Security Risks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend AI security specialist Pangea has added to its existing suite of corporate gen-AI security products with AI Guard and Prompt...
MirrorTab Raises $8.5M Seed Round to Take on Browser-Based Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine MirrorTab, a San Francisco startup building technology to neutralize malicious attacks at the browser layer, has secured $8.5 million in...
Finastra Starts Notifying People Impacted by Recent Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire British fintech giant Finastra last week started sending written notifications to individuals who had their personal information stolen in a...
Critical Vulnerability Patched in Juniper Session Smart Router – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Juniper Networks last week published an out-of-cycle security bulletin to inform customers about the availability of patches for a critical...
Singulr Launches With $10M in Funding for AI Security and Governance Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Singulr AI launched on Tuesday, announcing the general availability of its enterprise AI security and governance platform. With offices in...
Golang Backdoor Abuses Telegram for C&C Communication – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A recently discovered backdoor written in the Go programming language is abusing Telegram for command-and-control (C&C) communication, cybersecurity firm Netskope...
Microsoft Warns of Improved XCSSET macOS Malware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A new variant of the sophisticated XCSSET malware has been observed in recent, limited attacks against macOS users, Microsoft reports....
Palo Alto Networks Confirms Exploitation of Firewall Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Palo Alto Networks has confirmed for SecurityWeek that a recently patched firewall vulnerability tracked as CVE-2025-0108 is being actively exploited....
Xerox Printer Vulnerabilities Enable Credential Capture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Soure: T. Schneider via Shutterstock A popular small to midrange Xerox business printer contains two now-patched vulnerabilities in...
China-Linked Threat Group Targets Japanese Orgs’ Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: KB Photodesign via Shutterstock NEWS BRIEF Winnti, a China-affiliated threat actor, has been linked to...
Thrive Acquires Secured Network Services – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE BOSTON, Feb. 13, 2025 (GLOBE NEWSWIRE) — Thrive, a global technology outsourcing provider for cybersecurity, Cloud, and IT managed services, today...
SANS Institute Launches AI Cybersecurity Hackathon – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE As AI adoption accelerates, organizations lack the tools to secure these rapidly evolving technologies. While AI’s potential in cybersecurity is...
Microsoft: New Variant of macOS Threat XCSSET Spotted in the Wild – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Africa Studio via Alamy Stock Photo Attackers are wielding a new variant of one of the biggest...