New phishing campaign posing as Spain’s Tax Agency There’s a brand new phishing campaign on the run in Spain that poses as the Spanish Tax Agency,...
#IRISSCON: Police Officer Urges More Reporting and Engagement to Tackle Cybercrime
#IRISSCON: Police Officer Urges More Reporting and Engagement to Tackle CybercrimeIreland's National Cyber Crime Bureau outlines cybercrime trends being observed in law enforcementLeer másIreland's National Cyber...
Lacework releases cloud-native application security service
Lacework releases cloud-native application security serviceCloud security vendor Lacework this week announced the availability of a cloud-native application protection platform (CNAPP) for its broader Polygraph Data...
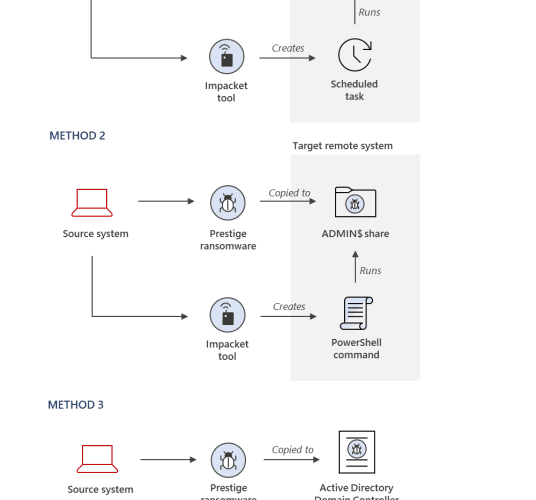
Russian military hackers linked to ransomware attacks in Ukraine
Russian military hackers linked to ransomware attacks in UkraineA series of attacks targeting transportation and logistics organizations in Ukraine and Poland with Prestige ransomware since October have...
Toward the cutting edge: SMBs contemplating enterprise security
Toward the cutting edge: SMBs contemplating enterprise securitySurvey finds SMBs, weary of security failures, curious about detection and response The post Toward the cutting edge: SMBs...
New Lenovo Notebook Models Affected By UEFI Firmware Vulnerabilities
New Lenovo Notebook Models Affected By UEFI Firmware VulnerabilitiesThe flaws affect various Lenovo Yoga, IdeaPad and ThinkBook devicesLeer másThe flaws affect various Lenovo Yoga, IdeaPad and...
Privileged Access Management (PAM) Best Practices
Privileged Access Management (PAM) Best PracticesPrivileged access management, PAM in short, is a crucial set of tools and technologies allowing organizations to maintain steadfast control and monitorization...
Russia-linked IRIDIUM APT linked to Prestige ransomware attacks against Ukraine
Russia-linked IRIDIUM APT linked to Prestige ransomware attacks against UkraineMicrosoft linked Prestige ransomware attacks against organizations in Ukraine and Poland to Russia-linked threat actors. In Mid-October,...
The Cost of a Siloed Response: How a Lack of Collaboration is Becoming Security’s Biggest Vulnerability
The Cost of a Siloed Response: How a Lack of Collaboration is Becoming Security’s Biggest VulnerabilityBy Neil Ellis, CIO and CISO at CafeX Communications Disparate Solutions...
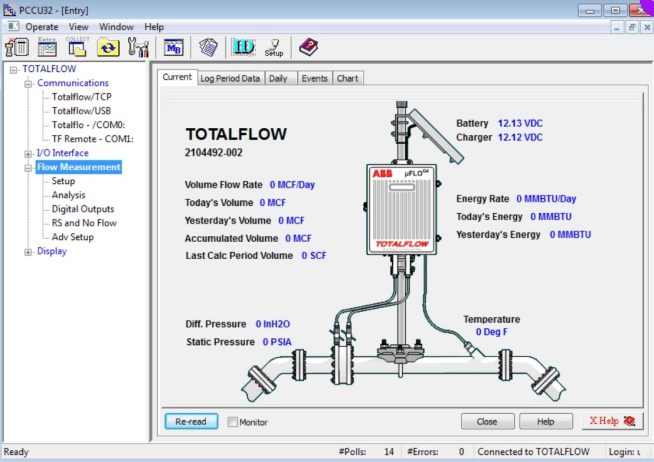
Oil and Gas Companies Are Vulnerable Due to High-Severity Flaw
Oil and Gas Companies Are Vulnerable Due to High-Severity FlawA new vulnerability was found by cybersecurity researchers, in systems used across oil and gas organizations. If...
Organizations Should Break into Their Own Networks
Organizations Should Break into Their Own NetworksBy John Meyer, Arcfield VP, Cyber Products and Services With talent and resources stretched thin, organizations may not […] The...
US Health Dept warns of Venus ransomware targeting healthcare orgs
US Health Dept warns of Venus ransomware targeting healthcare orgsThe U.S. Department of Health and Human Services (HHS) warned today that Venus ransomware attacks are also targeting...
The Future of Attack Surface Management: How to Prepare
The Future of Attack Surface Management: How to PrepareBy David Monnier, Team Cymru Fellow To stay ahead of threat actors, organizations must monitor their attack surfaces...
Microsoft fixes MoTW zero-day used to drop malware via ISO files
Microsoft fixes MoTW zero-day used to drop malware via ISO filesWindows has fixed a bug that prevented Mark of the Web flags from propagating to files...
Phishing drops IceXLoader malware on thousands of home, corporate devices
Phishing drops IceXLoader malware on thousands of home, corporate devicesA ongoing phishing campaign has infected thousands of home and corporate users with a new version of...
Windows 11 Task Manager will let you filter processes by name, PID
Windows 11 Task Manager will let you filter processes by name, PIDWindows 11 will soon let you filter processes in the Task Manager by their name,...
CVE-2019-8561: A Hard-to-Banish PackageKit Framework Vulnerability in macOS
CVE-2019-8561: A Hard-to-Banish PackageKit Framework Vulnerability in macOSThis blog entry details our investigation of CVE-2019-8561, a vulnerability that exists in the macOS PackageKit framework, a component...
Royal Mail down: Tracking unavailable as outage exceeds 24 hours
Royal Mail down: Tracking unavailable as outage exceeds 24 hoursRoyal Mail, UK's leading mail and parcel delivery service, has been experiencing ongoing outages with its online...
MSA-22-0023: Stored XSS and page denial of service risks due to recursive rendering in Mustache template helpers
MSA-22-0023: Stored XSS and page denial of service risks due to recursive rendering in Mustache template helpersот Michael Hawkins. Recursive rendering of Mustache template helpers containing...
MSA-22-0021: Upgrade Mustache to latest version (upstream)
MSA-22-0021: Upgrade Mustache to latest version (upstream)от Michael Hawkins. The Mustache template library included with Moodle has been upgraded to the latest version, which includes a...
MSA-22-0022: CSRF risk in enabling/disabling installed H5P libraries
MSA-22-0022: CSRF risk in enabling/disabling installed H5P librariesот Michael Hawkins. Enabling and disabling installed H5P libraries did not include the necessary token to prevent a CSRF...
‘We know who you are’: Australian police say Russian cybercriminals behind Medibank hack
‘We know who you are’: Australian police say Russian cybercriminals behind Medibank hackCommissioner Reece Kershaw says AFP has ‘significant runs on the scoreboard when it comes...
Worok hackers hide new malware in PNGs using steganography
Worok hackers hide new malware in PNGs using steganographyA threat group tracked as 'Worok' hides malware within PNG images to infect victims' machines with information-stealing malware...
A bug in ABB Totalflow flow computers exposed oil and gas companies to attack
A bug in ABB Totalflow flow computers exposed oil and gas companies to attackA flaw in the ABB Totalflow system used in oil and gas organizations could...
Researchers warn of malicious packages on PyPI using steganography
Researchers warn of malicious packages on PyPI using steganographyExperts discovered a malicious package on the Python Package Index (PyPI) that uses steganographic to hide malware within...
Apple out-of-band patches fix remote code execution bugs in iOS and macOS
Apple out-of-band patches fix remote code execution bugs in iOS and macOSApple released out-of-band patches for iOS and macOS to fix a couple of code execution...
Test post delete one – 10-11
Test post delete one – 10-11 “Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut...
Update your Lenovo laptop’s firmware now! Flaws could help malware survive a hard disk wipe
Update your Lenovo laptop’s firmware now! Flaws could help malware survive a hard disk wipePC manufacturer Lenovo has been forced to push out a security update...
Test post for network capture – 10 Nov
Test post for network capture – 10 NovWhat is Lorem Ipsum? Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been...
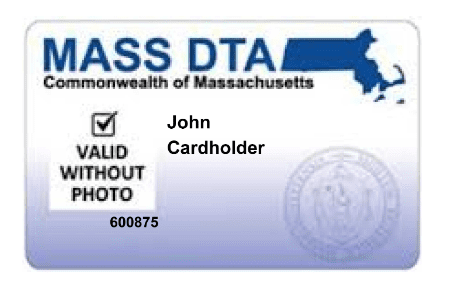
Lawsuit Seeks Food Benefits Stolen By Skimmers
Lawsuit Seeks Food Benefits Stolen By SkimmersA nonprofit organization is suing the state of Massachusetts on behalf of thousands of low-income families who were collectively robbed...