Microsoft linked Prestige ransomware attacks against organizations in Ukraine and Poland to Russia-linked threat actors.
In Mid-October, Microsoft Threat Intelligence Center (MSTIC) researchers uncovered previously undetected ransomware, tracked as Prestige ransomware, employed in attacks targeting organizations in the transportation and related logistics industries in Ukraine and Poland.
Microsoft has identified a new ransomware strain “Prestige” in limited targeted attacks in Ukraine and Poland. Several notable features differentiate this ransomware from other campaigns and payloads tracked by MSTIC. Get TTPs and protection info: https://t.co/4E3gaj1K7b
— Microsoft Security Intelligence (@MsftSecIntel) October 14, 2022
The Prestige ransomware first appeared in the threat landscape on October 11 in attacks occurring within an hour of each other across all victims.
A notable feature of this campaign is that it is uncommon to observe the threat actors attempting to deploy ransomware into the networks of Ukrainian enterprises.
The campaign shares victimology with recent operations conducted by Russia-linked threat actors.
In an update provided by Microsoft this week, MSTIC attributed the campaign to the IRIDIUM (aka Sandworm) cyberespionage group.
Sandworm (aka BlackEnergy and TeleBots) has been active since 2000, it operates under the control of Unit 74455 of the Russian GRU’s Main Center for Special Technologies (GTsST).
The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017, causing billions worth of damage.
In April, Sandworm targeted energy facilities in Ukraine with a new strain of the Industroyer ICS malware (INDUSTROYER2) and a new version of the CaddyWiper wiper.
The APT hacking group is believed to have been behind numerous attacks this year, including an attack on Ukrainian energy infrastructure and the deployment of a persistent botnet called “Cyclops Blink” dismantled by the US government in April.
From August 2022, Recorded Future researchers observed a rise in command and control (C2) infrastructure used by Sandworm (tracked by Ukraine’s CERT-UA as UAC-0113).
The researchers observed C2 infrastructure relying on dynamic DNS domains masquerading as Ukrainian telecommunication service providers.
Microsoft’s attribution to IRIDIUM is based on forensic artifacts, as well as overlaps in victimology, TTPs, and infrastructure, with the Russia-linked APT group.
“The Prestige campaign may highlight a measured shift in IRIDIUM’s destructive attack calculus, signaling increased risk to organizations directly supplying or transporting humanitarian or military assistance to Ukraine. More broadly, it may represent an increased risk to organizations in Eastern Europe that may be considered by the Russian state to be providing support relating to the war.” MSTIC said.
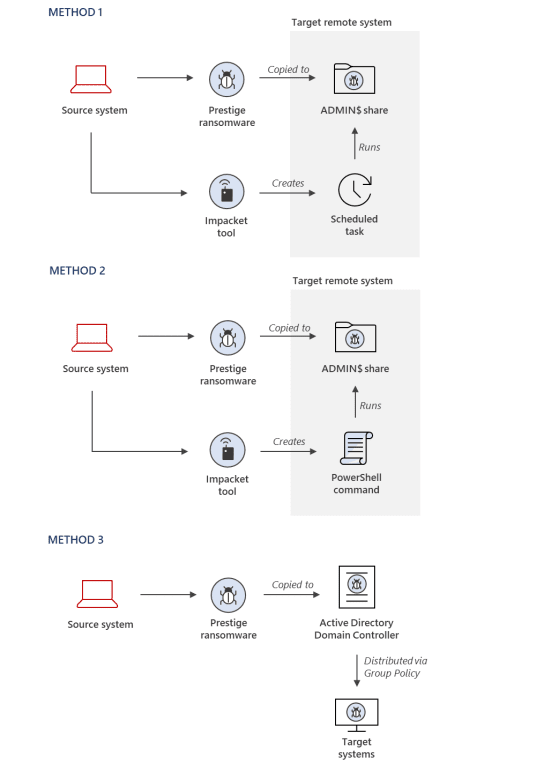
MSTIC researchers observed threat actors using three methods to deploy the Prestige ransomware:
Method 1: The ransomware payload is copied to the ADMIN$ share of a remote system, and Impacket is used to remotely create a Windows Scheduled Task on target systems to execute the payload
Method 2: The ransomware payload is copied to the ADMIN$ share of a remote system, and Impacket is used to remotely invoke an encoded PowerShell command on target systems to execute the payload
Method 3: The ransomware payload is copied to an Active Directory Domain Controller and deployed to systems using the Default Domain Group Policy Object
Microsoft published a list of indicators of compromise (IOCs) and advanced hunting queries detect Prestige ransomware infections.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Prestige ransomware)
The post Russia-linked IRIDIUM APT linked to Prestige ransomware attacks against Ukraine appeared first on Security Affairs.
Leer másSecurity Affairs
Views: 0