The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Author: Lucas Coletta
GUÍA PRÁCTICA DEL GDPR
The document emphasizes the importance of legally qualifying actors in the processing of personal data, particularly in the context of public affairs professionals. It mentions that...
Guia de Resposta a Incidentes de Segurança para LGPD
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Google Cloud Architecture Framework
Security, privacy and compliance The document outlines key steps to enhance cloud security, including conducting third-party audits like ISO 27017 for compliance verification, establishing security, privacy,...
CYBER-RISK OVERSIGHT HANDBOOK FOR CORPORATE BOARDS
The document acknowledges the contributions of various professionals and organizations in developing the Handbook, emphasizing that the content reflects collective inputs and consensus rather than individual...
FIREWALL Audit CHECKLIST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
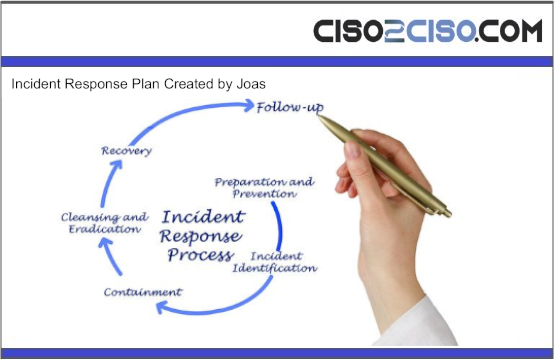
INCIDENT RESPONSE PLAN
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
INCIDENT REPORTING TEMPLATE
The Incident Response Form captures essential details related to incident management within an organization. It includes sections such as Incident Response Details, Incident Report Information, Incident...
Incident Response Recommendations and Considerations for Cybersecurity Risk Management
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
From plan to deployment: Implementing a cloud-native application protection platform(CNAPP) strategy
The document emphasizes the importance of Cloud Security Posture Management (CSPM) and the utilization of Defender for Cloud to enhance security measures. It highlights the need...
Identity and Access Management Policy
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Artificial Intelligence Risk Management Framework
Generative Artificial Intelligence Profile The document “NIST AI 600-1, Artificial Intelligence Risk Management Framework: Generative Artificial Intelligence Profile” outlines a comprehensive framework for managing risks associated...
National Cyber Strategy 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ley Marco de Ciberseguridad e Infraestructura Crítica de la Información
La Ley Marco de Ciberseguridad tiene como objetivo principal establecer un marco normativo que regule y coordine la ciberseguridad entre organismos estatales y privados. Esta ley...
MALWARE DEVELOPMENT PROCESS DIARIES
IN THIS COMPREHENSIVE GUIDE, WE DELVE INTO THE WORLD OF ANDROID SECURITY FROM AN OFFENSIVE PERSPECTIVE, SHEDDING LIGHT ON THE VARIOUS TECHNIQUES AND METHODOLOGIES USED BY...
MALWARE DEVELOPMENT EVADING DIARIES
IN THE INTRICATE LANDSCAPE OF CYBERSECURITY, MALWARE STANDS AS A PERVASIVE AND EVER-EVOLVING THREAT, CONTINUALLY ADAPTING TO CIRCUMVENT DETECTION AND EXPLOIT VULNERABILITIES IN DIGITAL SYSTEMS. ITS...
Malware prevention tips for businesses
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Mail Server Attacks Cheat Sheet
A cheat sheet that contains common enumeration and attack methods for Mail Server. The document provides a comprehensive overview of various attacks and information gathering techniques...
MERGERS AND ACQUISITIONS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Loaders Unleashed
The technical summary delves into loaders in various programming languages, emphasizing their functionalities and mechanisms. C/C++ loaders are vital for linking external resources, enhancing application efficiency...
Linux Privilege Escalation
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Artificial Intelligence and Cybersecurity
The Centre for European Policy Studies (CEPS) launched a Task Force on Artificial Intelligence (AI) and Cybersecurity in the autumn of 2019. The goal of this...
National Cybersecurity Strategy
The National Cybersecurity Strategy in Saudi Arabia aims to enhance cybersecurity measures in alignment with the Kingdom’s Vision 2030 and the evolving digital landscape. Developed with...
How to build a SOC with limited resources
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Kubernetes and Cloud Native Associate (KCNA) Study Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Management structures and responsibilities
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Metaverse Identity:
Defining the Self in a Blended Reality The document delves into the significance of identity within the metaverse, emphasizing its pivotal role in shaping human experiences...
Manual nmap
The Nmap Reference Guide provides comprehensive information on Nmap, a security scanner developed by Insecure.Com LLC. It covers topics such as port scanning, TCP window probing,...
MEMORY FORENSICS VOLATILITY
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Managing Artificial Intelligence-Specific Cybersecurity Risks in the Financial Services Sector
The U.S. Department of the Treasury’s report focuses on the use of Artificial Intelligence (AI) in the financial services sector, particularly in cybersecurity and fraud protection....