Source: www.techrepublic.com – Author: Nicole Rennolds We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
Author: CISO2CISO Editor 2
Zero Trust Access: The Transformative Blueprint for Achieving Regulatory Compliance – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Ironclad compliance through the Zero Trust innovation mindset By Roy Kikuchi, Director of Strategic Alliances at Safous, Internet Initiative Japan...
The Quantum Shift – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Preparing Cybersecurity for a New Era By Sercan Okur, VP of Technology, NextRay In contrast to my previous pieces, I...
CISO Life: the Good, the Bad, the Ugly – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary What type of things can go wrong with Senior Leadership, the Org, Legal, HR, etc. by Dan K. Anderson In today’s...
The Pitfalls of Periodic Penetration Testing & What to Do Instead – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Periodic penetration testing approaches can be likened to regular tire inspections for vehicles. While they provide valuable insights into the...
US Federal Data Privacy Law Introduced by Legislators – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A bipartisan US federal data protection law has been drafted by two US lawmakers, aiming to codify and enforce privacy rights...
Byakugan Infostealer Capabilities Revealed – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New research has shed light on the intricate workings of the Byakugan malware, initially detected in January. During an investigation into...
New Malware “Latrodectus” Linked to IcedID – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity researchers have identified a new loader named “Latrodectus,” discovered in November 2023, which has since been associated with nearly a...
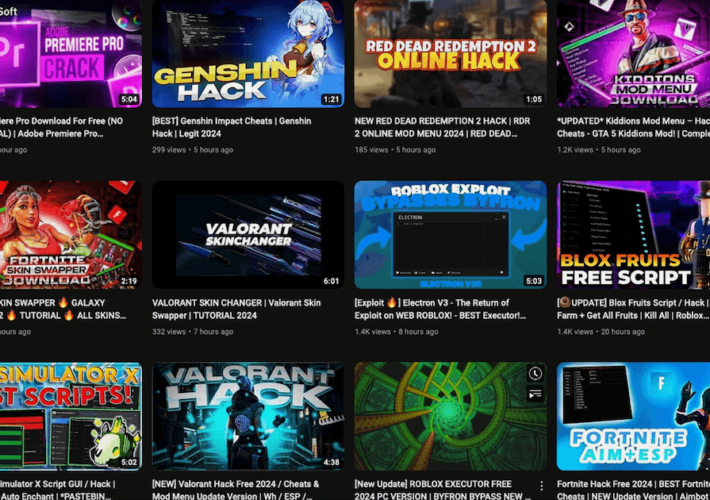
Famous YouTube Channels Hacked to Distribute Infostealers – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Threat actors increasingly utilize YouTube to distribute information stealer malware (infostealers) by appropriating legitimate channels as well as using their own...
UK Retailers Lost £11.3bn to Fraud in 2023 – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 More than a third (35%) of UK retailers fell victim to fraudulent activity, cyber-attacks or data leaks over the past 12...
Hospital IT Helpdesks Targeted By Voice Fraudsters, Warns HHS – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Department of Health and Human Services (HHS) has warned IT helpdesk operators in the sector of a surge in...
No 10 tells MPs to be cautious about unsolicited messages after attempted ‘honeytrap’ – Source: www.theguardian.com
Source: www.theguardian.com – Author: Kiran Stacey Political correspondent Downing Street has urged MPs to be cautious when responding to unsolicited messages, after the “spear-phishing” attack that...
Solar Spider Spins Up New Malware to Entrap Saudi Arabian Financial Firms – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Irina Shi via Shutterstock The sophisticated threat group behind a complex JavaScript remote access Trojan (RAT) known...
Massive AT&T Data Leak, The Danger of Thread Hijacking – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston Episode 324 features discussions on a significant AT&T data breach affecting 73 million customers and a sophisticated thread jacking attack...
Conn. CISO Raises Security Concerns Over BadGPT, FraudGPT – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Almost everyone has heard of ChatGPT. But Jeff Brown, CISO for the state of Connecticut, shares his concerns on...
9 Best Practices for Using AWS Access Analyzer – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ofir Stein Maintaining a strong security posture is crucial in today’s digital landscape, and it begins with users. Trusting users with access...
XZ-Utils Supply Chain Backdoor Vulnerability Updated Advisory (CVE-2024-3094) – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS Vulnerability Overview Recently, NSFOCUS CERT detected that the security community disclosed a supply chain backdoor vulnerability in XZ-Utils (CVE-2024-3094), with a...
The new features coming in Windows 11 24H2, expected this fall – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Windows 11 24H2 is set to arrive on existing devices this fall with several new features, mostly Copilot-related improvements. Additionally,...
Home Depot confirms third-party data breach exposed employee info – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Home Depot has confirmed that it suffered a data breach after one of its SaaS vendors mistakenly exposed a small...
New Windows driver blocks software from changing default web browser – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft is now using a Windows driver to prevent users from changing the configured Windows 10 and Windows 11 default...
The Case Study: The Exploitation of Mechatronics Systems – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Milica D. Djekic The mechatronics systems are a common part of the industrial control systems (ICS) or – in...
Strengthening Financial Services: Embracing the Digital Operational Resilience Act (DORA) for Cybersecurity Resilience – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Boris Khazin, Head of Governance, Risk & Compliance at EPAM Systems, Inc. While concerns about market volatility, liquidity management...
Speaking Cyber-Truth: The CISO’s Critical Role in Influencing Reluctant Leadership – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Craig Burland, CISO, Inversion6 In the C-Suites and boardrooms of modern enterprises, there’s an unwelcome guest that often disrupts...
US Health Dept warns hospitals of hackers targeting IT help desks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Department of Health and Human Services (HHS) warns that hackers are now using social engineering tactics to target...
Over 92,000 exposed D-Link NAS devices have a backdoor account – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A threat researcher has disclosed a new arbitrary command injection and hardcoded backdoor flaw in multiple end-of-life D-Link Network Attached...
Data Privacy in Email Communication: Compliance, Risks, and Best Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra Reading Time: 5 min Since the EU adopted the General Data Protection Regulation (GDRP) in 2018, businesses have been forced...
When Man Pages Go Weird – Source: securityboulevard.com
Source: securityboulevard.com – Author: Branden Williams You may not realize that I got my start in the technology world in the early 1990s learning Unix. From...
Malicious Latrodectus Downloader Picks Up Where QBot Left Off – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Source: Yuri Arcurs via Alamy Stock Photo At first, analysts thought the downloader was a variant of well-known malware IcedID —...
YouTube channels found using pirated video games as bait for malware campaign – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Hackers are distributing malware through multiple YouTube channels that promote cracked or pirated video games, according to researchers at Proofpoint. In...
“Hope Is Not a Strategy”: Cyber Leaders on the Real Keys to Executing a Defense-in-Depth Strategy – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Jesse Fasolo, Director, Technology Infrastructure & Cyber Security, St. Joseph’s Health When it comes to cybersecurity — and by extension, patient...