Source: securityboulevard.com – Author: Maycie Belmore The adoption of artificial intelligence (AI) in cybersecurity continues to spark intense discussions, especially around its impact on efficiency and...
Author: CISO2CISO Editor 2
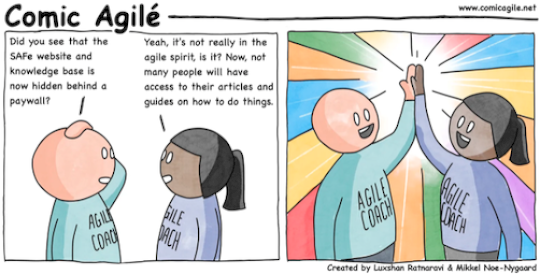
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #317 – Paywall – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the respected Software Engineering expertise of Mikkel Noe-Nygaard and the lauded Software Engineering / Enterprise Agile Coaching work of Luxshan Ratnaravi at Comic Agilé! Permalink *** This is a...
Log4Shell Vulnerability | Why it Still Exists and How to Protect Yourself | Contrast Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Contrast Marketing Three years ago, Log4Shell was the worst holiday gift ever for security teams, particularly given that it was wrapped in...
AI-Powered Actions Cybersecurity Leaders Are Taking to Outwit Bad Actors – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Gosschalk As a cybersecurity executive, your job is clear: protect business operations, safeguard consumers and ensure the security of your employees....
Diamond Bank Addresses Spoof Websites – Source: securityboulevard.com
Source: securityboulevard.com – Author: pmiquel Diamond Bank is a community bank with 14 branches and thousands of customers in the Southwest Arkansas region. The bank celebrated...
DEF CON 32 – Measuring the Tor Network – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Friday, December 20, 2024 Home » Security Bloggers Network » DEF CON 32 – Measuring the Tor Network Authors/Presenters: Silvia...
Impart is now available in the AWS Marketplace | Impart Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Impart Security Blog Today, we are thrilled to announce that Impart is now available in the AWS Marketplace. More Streamlined Contracting AWS customers...
SAML (Security Assertion Markup Language): A Comprehensive Guide – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Security Assertion Markup Language (SAML) is an open standard for exchanging authentication and authorization data...
Bitter APT Targets Turkish Defense Sector with WmRAT and MiyaRAT Malware – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: Dec 17, 2024Ravie LakshmananCyber Espionage / Malware A suspected South Asian cyber espionage threat group known as Bitter targeted a Turkish defense...
Friday Squid Blogging: Squid Sticker – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
How to Protect Your Environment From the NTLM Vulnerability – Source: www.darkreading.com
Source: www.darkreading.com – Author: Roy Akerman Roy Akerman, VP of Identity Security Strategy, Silverfort December 20, 2024 4 Min Read Source: Supapixx via Alamy Stock Photo...
LockBit Ransomware Developer Arrested in Israel – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Peter Werner via Alamy Stock Photo NEWS BRIEF A newly unsealed criminal complaint by US...
US Ban on TP-Link Routers More About Politics Than Exploitation Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: metamorworks via Shutterstock With US government agencies and lawmakers reportedly considering a ban on TP-Link’s products in...
How Nation-State Cybercriminals Are Targeting the Enterprise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Adam Finkelstein Adam Finkelstein, Senior Vice President of Global Client Leadership, Sygnia December 20, 2024 5 Min Read Source: Pablo Lagarto via...
Managing Threats When Most of the Security Team Is Out of the Office – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joan Goodchild Source: Anastasia Nelen via Unsplash Experienced security leaders know that attackers are patient. Attackers can infiltrate corporate chat systems like...
US order is a reminder that cloud platforms aren’t secure out of the box – Source: www.csoonline.com
Source: www.csoonline.com – Author: A Binding Directive from CISA orders the implementation by federal agencies of baseline configurations for SaaS platforms. This week’s binding directive to...
Enhance Microsoft security by ditching your hybrid setup for Entra-only join – Source: www.csoonline.com
Source: www.csoonline.com – Author: Prepare now for the eventual end of Microsoft Active Directory as it’s phased out in favor of the more secure, less risky...
Russia fires its biggest cyberweapon against Ukraine – Source: www.csoonline.com
Source: www.csoonline.com – Author: The largest cyberattack in recent memory halts critical government services in Ukraine as officials rush to restore operations and safeguard systems. Ukraine...
Die 10 besten API-Security-Tools – Source: www.csoonline.com
Source: www.csoonline.com – Author: Hier stellen wir Ihnen zehn API-Sicherheitslösungen vor, die Ihnen helfen, Ihre Schnittstellen zu überblicken und abzusichern. Mithilfe von APIs können verschiedene Software-Komponenten...
BellaCPP: Discovering a new BellaCiao variant written in C++ – Source: securelist.com
Source: securelist.com – Author: Mert Degirmenci Introduction BellaCiao is a .NET-based malware family that adds a unique twist to an intrusion, combining the stealthy persistence of...
Understanding Basics of Apache Kafka – Source: socprime.com
Source: socprime.com – Author: Oleksii K. WRITTEN BY Oleksii K. DevOps Engineer [post-views] December 20, 2024 · 2 min read Apache Kafka is an open-source platform...
Using map Command in Splunk – Source: socprime.com
Source: socprime.com – Author: Alex Verbniak WRITTEN BY Alex Verbniak Senior Security Engineer [post-views] December 20, 2024 · 3 min read The map command in Splunk...
Splunk: Using collect Command for Creating New Events in a New Index – Source: socprime.com
Source: socprime.com – Author: Alex Verbniak WRITTEN BY Alex Verbniak Senior Security Engineer [post-views] December 20, 2024 · 2 min read In some scenarios, you may...
Ransomware Group Claims Theft of Personal, Financial Data From Krispy Kreme – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Play ransomware group has claimed responsibility for the cyberattack that disrupted operations at donut and coffee retail chain Krispy...
Another NetWalker Ransomware Affiliate Gets 20-Year Prison Sentence in US – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A Romanian national accused of conducting cyberattacks using the NetWalker ransomware has been sentenced to 20 years in prison in...
CISA Urges Immediate Patching of Exploited BeyondTrust Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US cybersecurity agency CISA warns that a recently disclosed vulnerability in BeyondTrust’s remote access products has been exploited in...
Rockwell PowerMonitor Vulnerabilities Allow Remote Hacking of Industrial Systems – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Critical vulnerabilities patched by Rockwell Automation in its Allen-Bradley PowerMonitor 1000 product could allow remote hackers to breach an organization’s...
How to Implement Impactful Security Benchmarks for Software Development Teams – Source: www.securityweek.com
Source: www.securityweek.com – Author: Matias Madou Vulnerabilities introduced from third-party components continue to create major issues for organizations: Nearly all codebases, for example, contain open-source components,...
CISA Releases Mobile Security Guidance After Chinese Telecom Hacking – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US cybersecurity agency CISA on Wednesday released guidance for highly targeted individuals to protect their mobile communications against exploitation...
Ukrainian Raccoon Infostealer Operator Sentenced to Prison in US – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Department of Justice on Wednesday announced the sentencing of a Ukrainian national for his role in the distribution...