Source: www.csoonline.com – Author: Die Black Basta-Gruppe hat auch über den Jahreswechsel hinaus gezielte Ransomware-Angriffe durchgeführt. So schützen sich Unternehmen gegen die neue Methode. Ein lückenloser...
Author: CISO2CISO Editor 2
AMD’s unpatched chip microcode glitch may require extreme measures by CISOs – Source: www.csoonline.com
Source: www.csoonline.com – Author: AMD has confirmed an unpatched “processor vulnerability” that may require CISOs to isolate their systems or even air gap them until there’s...
Warning to FortiGate admins: You need to run a compromise assessment now – Source: www.csoonline.com
Source: www.csoonline.com – Author: This comes after stolen configuration data and passwords from a two-year old hack were leaked last week. Network administrators with Fortinet’s FortiGate...
Palo Alto Networks firewalls have UEFI flaws, Secure Boot bypasses – Source: www.csoonline.com
Source: www.csoonline.com – Author: Security researchers have uncovered known firmware flaws in three Palo Alto enterprise firewall devices built on commodity hardware. Researchers have discovered that...
Phishing Emails Targeting Australian Firms Rise by 30% in 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson The number of phishing emails received by Australians surged by 30% last year, new research by security firm Abnormal Security...
War Game Pits China Against Taiwan in All-Out Cyberwar – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Kevin M. Law via Alamy Stock Photo If China attacked Taiwan, how could Taiwan defend its critical...
Tesla Gear Gets Hacked Multiple Times in Pwn2Own Contests – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading Source: VDWI Automotive via Alamy Stock Photo NEWS BRIEF Researchers at the this year’s Pwn2Own Automotive...
CISA Calls For Action to Close the Software Understanding Gap – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WASHINGTON – Today, the Cybersecurity and Infrastructure Security Agency (CISA), in partnership with the Defense Advanced Research Projects Agency (DARPA),...
Omdia Finds Phishing Attacks Top Smartphone Security Concern for Consumers – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE LONDON, Jan. 20, 2025 /PRNewswire/ — A new survey from Omdia reveals that phishing scams are the leading security threat for smartphone users, with...
Automox Releases Endpoint Management With FastAgent – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE AUSTIN, TX, Jan. 21, 2025 (GLOBE NEWSWIRE) — Automox launches FastAgent, a breakthrough in modern agent technology designed to deliver unprecedented speed,...
84% of Healthcare Organizations Spotted a Cyberattack in the Late Year – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE FRISCO, Texas, January 21, 2025 – Netwrix, a vendor specializing in cybersecurity solutions focused on data and identity threats, surveyed 1,309 IT and security...
Cloudflare CDN Bug Outs User Locations on Signal, Discord – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Brian Jackson via Alamy Stock Photo A flaw in the widely used Cloudflare content delivery network (CDN)...
North Korean IT Workers Holding Data Hostage for Extortion, FBI Warns – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: The FBI has warned that North Korean IT worker schemes are stealing data to extort their victims as part of efforts to...
Ransomware Gangs Linked by Shared Code and Ransom Notes – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Two recently identified ransomware gangs are using payloads that contain almost identical code, suggesting that the groups’ affiliates are using shared infrastructure....
Chained Vulnerabilities Exploited in Ivanti Cloud Service Appliances – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Threat actors have been actively exploiting chained vulnerabilities in Ivanti Cloud Service Appliances (CSA), significantly amplifying the impact of their cyber-attacks. The...
Bookmakers Ramp Up Efforts to Combat Arbitrage Betting Fraud – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: A growing wave of arbitrage betting fraud, driven by automation and advanced money laundering techniques, has been forcing bookmakers to adopt stricter...
The Power of Many: Crowdsourcing as A Game-Changer for Modern Cyber Defense – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team With the rapid technological advancement and the world entering the AI era, the cyber threat landscape has significantly evolved in...
Operational Security: The Backbone of Effective Police Communication – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team In the fast-paced and dynamic world of law enforcement, effective communication is essential for ensuring public safety and successful operations....
A K-12 Guide to the Digital Classroom – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alexa Sander Digital tools have transformed how teachers and students engage in classroom activities, creating opportunities to enhance learning, communication, and organization....
Understanding the 3-Layers of Non-Human Identity (NHI) Security in TrustFour’s Posture and Attack Surface Management Framework – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jim Curtin In today’s interconnected digital ecosystems, securing Non-Human Identities (NHIs) has become a critical focus. NHIs—representing machines, applications, containers, and microservices—outnumber...
Safe Secrets Rotation: A Must for Modern Clouds – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Why is Secrets Rotation Crucial for Cloud Security? Are you familiar with the concept of secrets rotation? Does it sound...
Boosting Confidence in Cloud-Native Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Are You Confident in Your Cloud-Native Security? Navigating cybersecurity can be like walking through a maze filled with lurking threats....
Unlocking Innovation with Protected Machine Identities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Cohn Is Your Organization Paying Enough Attention to Non-Human Identities? Organizations extensively utilize cloud services and automated systems. In doing so,...
How to Stop Layer 7 DDoS Attacks in 2025 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Andrew Hendry Imagine your website humming with activity, traffic soaring, and your brand capturing the attention it deserves. But what if that...
6 Ways IT Can Help You Modernize Case Management Software – Source: securityboulevard.com
Source: securityboulevard.com – Author: Manish Mehta Article Your IT department can be a valuable ally in overcoming inevitable resistance to change Related Resources Modern and effective...
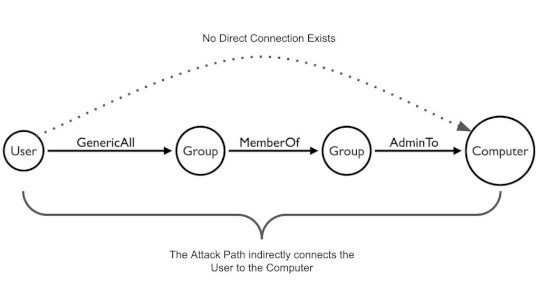
Insurance companies can reduce risk with Attack Path Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kirsten Gibson TL;DR Insurance companies host large amounts of sensitive data (PII, PHI, etc.) and often have complex environments due to M&A...
DEF CON 32 – The Wild And Wonderful World Of Early Microprocessors With A Focus On 6502 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Thursday, January 23, 2025 Home » Security Bloggers Network » DEF CON 32 – The Wild And Wonderful World Of...
SOC vs MSSP: Which is Right for Your Business? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rebecca Kappel One of the most pivotal decisions an organization faces is whether to build an in-house Security Operations Center (SOC) or...
Proofpoint and Ingram Micro Team to Radically Simplify and Accelerate Sales Cycles for Partners – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: Channel partners benefit from an unparalleled agile procurement process to strengthen their business opportunities and close deals faster SUNNYVALE, Calif., January 23,...
Automating endpoint management doesn’t mean ceding control – Source: www.csoonline.com
Source: www.csoonline.com – Author: AEM can help solve persistent skills gaps, tool sprawl, and budget constraints. Beset with cybersecurity risks, compliance regimes, and digital experience challenges,...